Question: Write a program that asks the user their first name, last name, current address, city, state, and zip code. Then write a mailing label
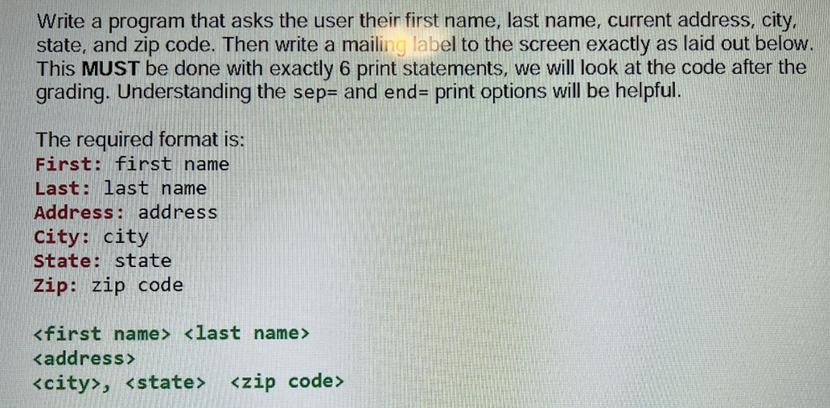
Write a program that asks the user their first name, last name, current address, city, state, and zip code. Then write a mailing label to the screen exactly as laid out below. This MUST be done with exactly 6 print statements, we will look at the code after the grading. Understanding the sep- and end= print options will be helpful. The required format is: First: first name Last: last name Address: address City: city State: state Zip: zip code ,
Step by Step Solution
There are 3 Steps involved in it
Python Get user input firstname inputEnter your first name lastname inputEnter your l... View full answer

Get step-by-step solutions from verified subject matter experts


