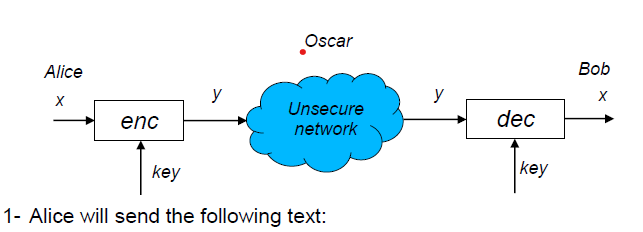
Question: write a program to achieve encryption and decryption using the Monoalphabetic Substitution Cipher system. The key can be generated randomly by Alice and sent to
write a program to achieve encryption and decryption using the Monoalphabetic Substitution Cipher system. The key can be generated randomly by Alice and sent to Bob securely The task must:
Alice will send the following text:
I remember as a child, and as a young budding naturalist, spending all my time observing and testing the world around me moving pieces, altering the flow of things, and documenting ways the world responded to me Now, as an adult and a professional naturalist, Ive approached language in the same way, not from an academic point of view but as a curious child still building little mud dams in creeks and chasing after frogs. So this book is an odd thing: it is a naturalists walk through the languagemaking landscape of the English language, and following in the naturalists tradition it combines observation, experimentation, speculation, and documentation activities we dont normally associate with language.
This book is about testing, experimenting, and playing with language. It is a handbook of tools and techniques for taking words apart and putting them back together again in ways that I hope are meaningful and legitimate or even illegitimate This book is about peeling back layers in search of the languagemaking energy of the human spirit. It is about the gaps in meaning that we urgently need to notice and name the places where our dreams and ideals are no longer fulfilled by a society that has become fastpaced and hyper commercialized.
Language is meant to be a playful, evershifting creation but we have been taught, and most of us continue to believe, that language must obediently follow precisely prescribed rules that govern clear sentence structures, specific word orders, correct spellings, and proper pronunciations. If you make a mistake or step out of bounds there are countless, selfappointed language experts who will promptly push you back into safe terrain and scold you for your errors. And in case you need reminding, there are hundreds of dictionaries and grammar books to ensure that you remember the right way to use English.
Bob will receive the ciphered text and be able to read it
Meanwhile, Oscar will attempt to hack the ciphered text and read the message without knowing the key. "Find the best way to perform the hacking and implement it
Alice will send a message in another language, such as "Select your mother language" or "German language," and repeat steps and
Task points:
Repeat Task with Polyalphabetic Substitution Cipher.
Can Oscar break the ciphering, and how long does it take
Task points:
Repeat Task Points and using DES ciphering. You have to implement all the steps of DES.
Repeat Task Points and by sending a bitmap image. Show the image before encryption, after encryption, and after decryption.
Homework submission requirements
The homework is individual work, so do not share your work with friends. Any copying will be considered as cheating, and both parties will receive a zero.
Use only Python version or Java version or above as the programming language; no other programming languages are allowed.
Write all steps in a report. Your report must include the solution, screenshots, and results. Include a report cover page.
Submit the homework in the Microsoft Teams assignment section.
Submissions via email will not be considered.
Homework without a report will not be accepted.
Submit all the codes and implemnatation test files and results, and user guide in the MsTeam Alice will send the following text: assignment section along with report in one zip file
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


