Question: Write a Python function max_times that consumes L, a non-empty list of non-empty lists of integers, and returns a list of length two, where
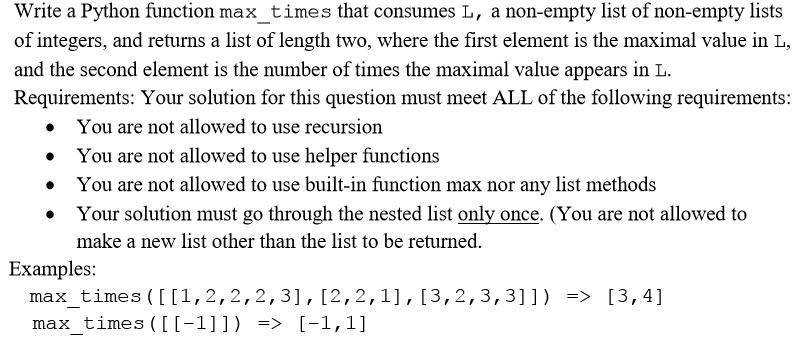
Write a Python function max_times that consumes L, a non-empty list of non-empty lists of integers, and returns a list of length two, where the first element is the maximal value in L, and the second element is the number of times the maximal value appears in L. Requirements: Your solution for this question must meet ALL of the following requirements: You are not allowed to use recursion You are not allowed to use helper functions You are not allowed to use built-in function max nor any list methods Your solution must go through the nested list only once. (You are not allowed to make a new list other than the list to be returned. Examples: max_times ([[1, 2, 2, 2, 3], [2,2,1], [3,2,3,3]]) => [3,4] max_times ([[1]]) => [-1,1]
Step by Step Solution
There are 3 Steps involved in it
The code is as follow def maxtimesL Initialize variables ... View full answer

Get step-by-step solutions from verified subject matter experts


