Question: Write a python program that ciphers a plain text message using double transposition scheme and vice versa. The program should accept five tuples of
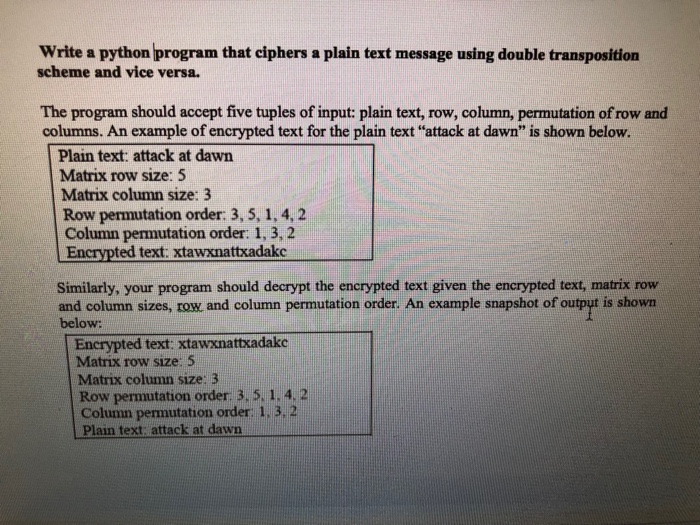
Write a python program that ciphers a plain text message using double transposition scheme and vice versa. The program should accept five tuples of input: plain text, row, column, permutation of row and columns. An example of encrypted text for the plain text "attack at dawn" is shown below. Plain text: attack at dawn Matrix row size: 5 Matrix column size: 3 Row permutation order: 3, 5, 1, 4, 2 Column permutation order: 1, 3, 2 Encrypted text: xtawxnattxadakc Similarly, your program should decrypt the encrypted text given the encrypted text, matrix row is shown and column sizes, row, and column permutation order. An example snapshot of output below: Encrypted text: xtawxnattxadake Matrix row size: 5 Matrix column size: 3 Row permutation order: 3, 5, 1, 4, 2 Column permutation order: 1. 3. 2 Plain text: attack at dawn
Step by Step Solution
3.42 Rating (158 Votes )
There are 3 Steps involved in it
To solve this problem using Python you need to implement a double transposition cipher Heres how you can do it Ciphering Process 1 Arrange the plainte... View full answer

Get step-by-step solutions from verified subject matter experts


