Question: Write a shell script program to emulate the PowerShell environment (translate the PowerShell commands below using linux bash shell script.) 1. Get-Process (Then let
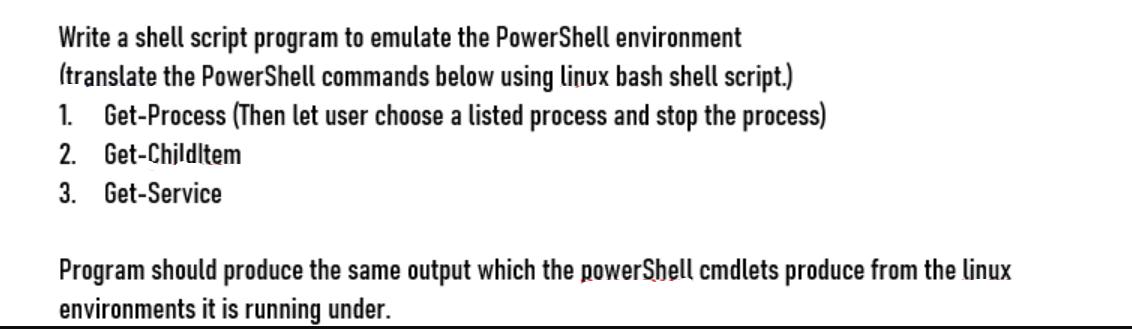
Write a shell script program to emulate the PowerShell environment (translate the PowerShell commands below using linux bash shell script.) 1. Get-Process (Then let user choose a listed process and stop the process) 2. Get-Childltem 3. Get-Service Program should produce the same output which the powerShell cmdlets produce from the linux environments it is running under.
Step by Step Solution
There are 3 Steps involved in it
To emulate the PowerShell environment in a Linux bash shell script you can use the following script ... View full answer

Get step-by-step solutions from verified subject matter experts


