Question: Write the linear-time recursive function template isBST() that returns true if a binary tree is a valid Binary Search Tree, and false otherwise. Hint:
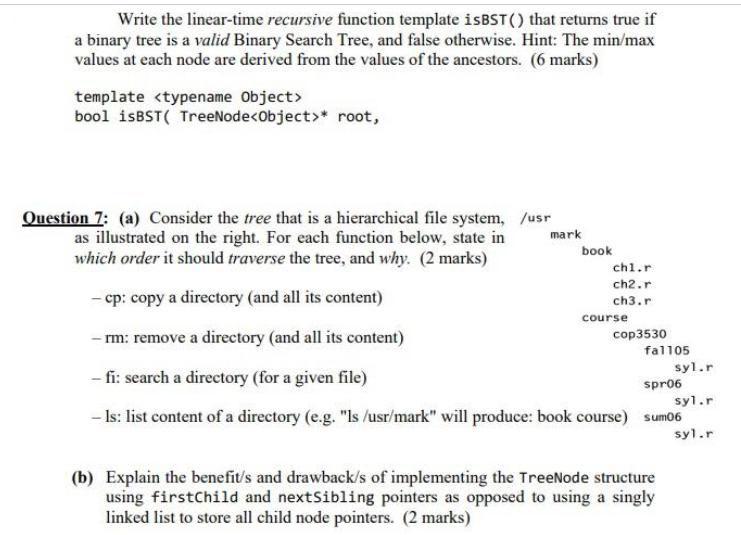
Write the linear-time recursive function template isBST() that returns true if a binary tree is a valid Binary Search Tree, and false otherwise. Hint: The min/max values at each node are derived from the values of the ancestors. (6 marks) template bool isBST( TreeNode * root, Question 7: (a) Consider the tree that is a hierarchical file system, /usr as illustrated on the right. For each function below, state in which order it should traverse the tree, and why. (2 marks) - cp: copy a directory (and all its content) -rm: remove a directory (and all its content) - fi: search a directory (for a given file) spr06 syl.r - Is: list content of a directory (e.g. "Is /usr/mark" will produce: book course) sum06 syl.r mark book chl.r ch2.r ch3.r course cop3530 fal105 (b) Explain the benefit/s and drawback/s of implementing the TreeNode structure using firstChild and nextSibling pointers as opposed to using a singly linked list to store all child node pointers. (2 marks) syl.r Write the linear-time recursive function template isBST() that returns true if a binary tree is a valid Binary Search Tree, and false otherwise. Hint: The min/max values at each node are derived from the values of the ancestors. (6 marks) template bool isBST( TreeNode * root, Question 7: (a) Consider the tree that is a hierarchical file system, /usr as illustrated on the right. For each function below, state in which order it should traverse the tree, and why. (2 marks) - cp: copy a directory (and all its content) -rm: remove a directory (and all its content) - fi: search a directory (for a given file) spr06 syl.r - Is: list content of a directory (e.g. "Is /usr/mark" will produce: book course) sum06 syl.r mark book chl.r ch2.r ch3.r course cop3530 fal105 (b) Explain the benefit/s and drawback/s of implementing the TreeNode structure using firstChild and nextSibling pointers as opposed to using a singly linked list to store all child node pointers. (2 marks) syl.r
Step by Step Solution
3.35 Rating (155 Votes )
There are 3 Steps involved in it
a Traversal orders 1 cp depthfirst traversal DFT starting from the root node visit each node in depthfirst order copying the contents of each node rec... View full answer

Get step-by-step solutions from verified subject matter experts


