You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
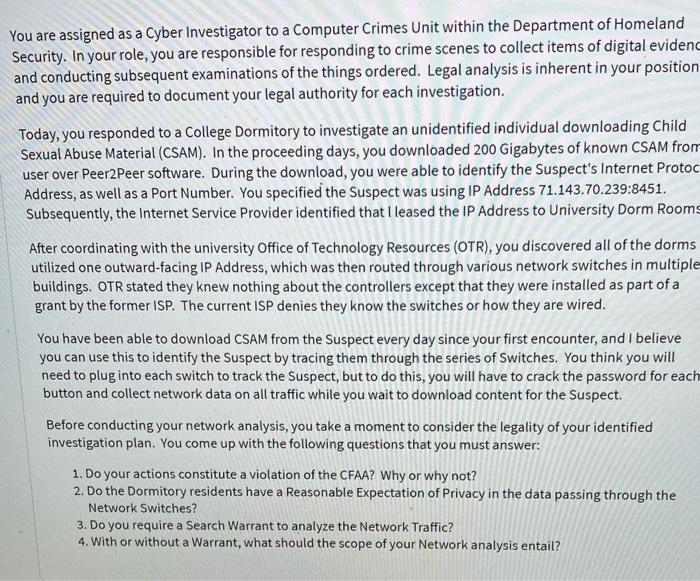
You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of Homeland Security. In your role, you are responsible for responding to crime scenes to collect items of digital evidenc and conducting subsequent examinations of the things ordered. Legal analysis is inherent in your position and you are required to document your legal authority for each investigation. Today, you responded to a College Dormitory to investigate an unidentified individual downloading Child Sexual Abuse Material (CSAM). In the proceeding days, you downloaded 200 Gigabytes of known CSAM from user over Peer2Peer software. During the download, you were able to identify the Suspect's Internet Protoc Address, as well as a Port Number. You specified the Suspect was using IP Address 71.143.70.239:8451. Subsequently, the Internet Service Provider identified that I leased the IP Address to University Dorm Rooms After coordinating with the university Office of Technology Resources (OTR), you discovered all of the dorms utilized one outward-facing IP Address, which was then routed through various network switches in multiple buildings. OTR stated they knew nothing about the controllers except that they were installed as part of a grant by the former ISP. The current ISP denies they know the switches or how they are wired. You have been able to download CSAM from the Suspect every day since your first encounter, and I believe you can use this to identify the Suspect by tracing them through the series of Switches. You think you will need to plug into each switch to track the Suspect, but to do this, you will have to crack the password for each button and collect network data on all traffic while you wait to download content for the Suspect. Before conducting your network analysis, you take a moment to consider the legality of your identified investigation plan. You come up with the following questions that you must answer: 1. Do your actions constitute a violation of the CFAA? Why or why not? 2. Do the Dormitory residents have a Reasonable Expectation of Privacy in the data passing through the Network Switches? 3. Do you require a Search Warrant to analyze the Network Traffic? 4. With or without a Warrant, what should the scope of your Network analysis entail? You are assigned as a Cyber Investigator to a Computer Crimes Unit within the Department of Homeland Security. In your role, you are responsible for responding to crime scenes to collect items of digital evidenc and conducting subsequent examinations of the things ordered. Legal analysis is inherent in your position and you are required to document your legal authority for each investigation. Today, you responded to a College Dormitory to investigate an unidentified individual downloading Child Sexual Abuse Material (CSAM). In the proceeding days, you downloaded 200 Gigabytes of known CSAM from user over Peer2Peer software. During the download, you were able to identify the Suspect's Internet Protoc Address, as well as a Port Number. You specified the Suspect was using IP Address 71.143.70.239:8451. Subsequently, the Internet Service Provider identified that I leased the IP Address to University Dorm Rooms After coordinating with the university Office of Technology Resources (OTR), you discovered all of the dorms utilized one outward-facing IP Address, which was then routed through various network switches in multiple buildings. OTR stated they knew nothing about the controllers except that they were installed as part of a grant by the former ISP. The current ISP denies they know the switches or how they are wired. You have been able to download CSAM from the Suspect every day since your first encounter, and I believe you can use this to identify the Suspect by tracing them through the series of Switches. You think you will need to plug into each switch to track the Suspect, but to do this, you will have to crack the password for each button and collect network data on all traffic while you wait to download content for the Suspect. Before conducting your network analysis, you take a moment to consider the legality of your identified investigation plan. You come up with the following questions that you must answer: 1. Do your actions constitute a violation of the CFAA? Why or why not? 2. Do the Dormitory residents have a Reasonable Expectation of Privacy in the data passing through the Network Switches? 3. Do you require a Search Warrant to analyze the Network Traffic? 4. With or without a Warrant, what should the scope of your Network analysis entail?
Expert Answer:
Answer rating: 100% (QA)
1 Whether your actions constitute a violation of the Computer Fraud and Abuse Act CFAA depends on the specifics of the situation and how you access an... View the full answer

Related Book For 

Cost Management A Strategic Emphasis
ISBN: 978-0078025532
6th edition
Authors: Edward Blocher, David Stout, Paul Juras, Gary Cokins
Posted Date:
Students also viewed these business communication questions
-
Using the article Comparing Crime Rates between Undocumented Immigrants, Legal Immigrants, and Native-born US citizens in Texas, write a 2-3 page-paper (double-spaced, 1-inch margins, times roman...
-
Answer the questions in your journal. Which contemporary issue interested you the most, and why? (M424) Define Explain Personal Experience What do you think is another contemporary issue the army...
-
Find a couple of bad project management examples from around the world. What were the reasons for the failure? (500 words max) Find a couple of good project management examples from around the world....
-
On December 31, 2012, Marsh Company held 1,000 shares of Xenon Company common stock in its portfolio of available-for-sale securities. The stock had cost $15 per share and has a current market value...
-
Rondo Ltd. (RL) is a wholesaler operation, with an active warehouse. Staff at RL have prepared a preliminary list of inventory, following its count on November 30. Required: Determine the dollar...
-
For Problem 6.8, (a) Fit the corresponding negative binomial model with the same linear predictor. (b) Compare the analysis between part (a) and that from Problem 6.8. 6.8 For the Sexual Health pilot...
-
The Stone River Textile Mill was inspected by OSHA and found to be in violation of a number of safety regulations. The OSHA inspectors ordered the mill to alter some existing machinery to make it...
-
An 80 kg person stands in an elevator which is ascending towards the top of a building. A) As the elevator begins its ascent, it accelerates at the rate of 1 m/s2 . Draw the free body diagram showing...
-
Use the balanced equation, N+O-2NO, to answer the following question. How many grams of O, are needed to react completely with 10.2 g of N? Be sure your answer has the correct number of significant...
-
A kickback scheme has been discovered in a warehouse company that purchases office supplies for resale. The perpetrator is the purchasing agent. The agent personally benefited from receiving around...
-
Music lessons for your child will cost $1,265 per year. If you get a part-time job that pays $6.05 per hour, how many hours will you have to work in a year to pay for the music lessons?
-
Ben opened a retail store on 1 April 2017. He introduced the following into the business. Inventory 15 200 Shop fittings 14 300 Cash 17 900 (of which $17 400 was paid into a business bank account) On...
-
Prepare the finance department's budget for next year. He thinks expenses will be about $120,000, but decides to add a cushion of $80,000, for a total submitted budget of $200,000.
-
Prepare the required March 31st and June 30th journal entries. You are only completing the payroll and vacation accrual portion of the payroll entries and cash can be credited to account for actual...
-
1. Why do you think it was so hard to integrate the different companies that were merged? 2. What are some challenges involved with managing a very large, diverse financial services company? You must...
-
The unadjusted trial balance of Secretarial Services is as follows: SECRETARIAL SERVICES Unadjusted Trial Balance as at 31 December 2017 Account Debit Credit Cash at bank Office supplies Prepaid...
-
Consider the following information for Fair Wind Yachts, Inc., a manufacturer of sailboat rigging, blocks, and cordage. Advertising Expenses. $ 150,000 Depreciation Expense--Admin. Office 75,000...
-
To maintain profit growth, several manufacturing companies have responded to the recession by cutting jobs. Harley-Davidson reduced its workforce by 1,400 in 2010 and 1,600 more in 2011. As sales...
-
Holly Company has the following information for December 1 to December 31. All direct materials are 100% complete. Required Calculate equivalent units using the weighted-average and FIFO methods....
-
An analyst is reviewing various asset alternatives and is presented with the following information relating to the broad equity market of Switzerland and various industries within the Swiss market...
-
An Australian investor currently holds an A$240 million equity portfolio. He is considering rebalancing the portfolio based on an assessment of the risk and return prospects facing the Australian...
-
Identify risks faced by investors in emerging market equities over and above those that are faced by fixed-income investors in such markets.

Study smarter with the SolutionInn App