Question: You desire to prove a vulnerability can be a problem. The best method would be to use a(n) scan? 1) credentialed 2) non-intrusive 3) non-credentialed
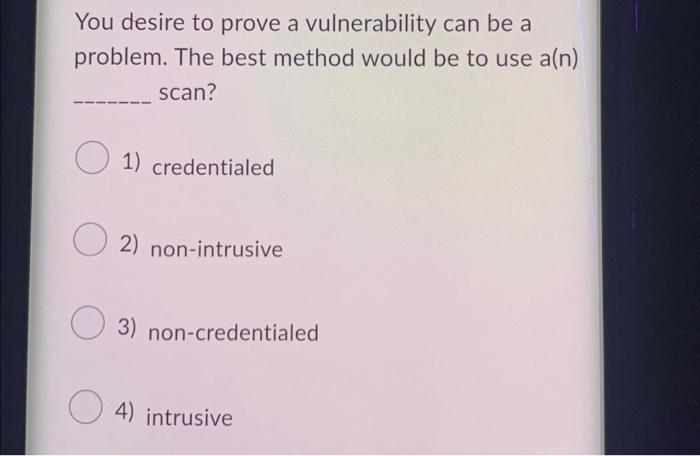
You desire to prove a vulnerability can be a problem. The best method would be to use a(n) scan? 1) credentialed 2) non-intrusive 3) non-credentialed 4) intrusive
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


