You have been selected to be the leader of a Secret Spy Team! As a mathematician...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
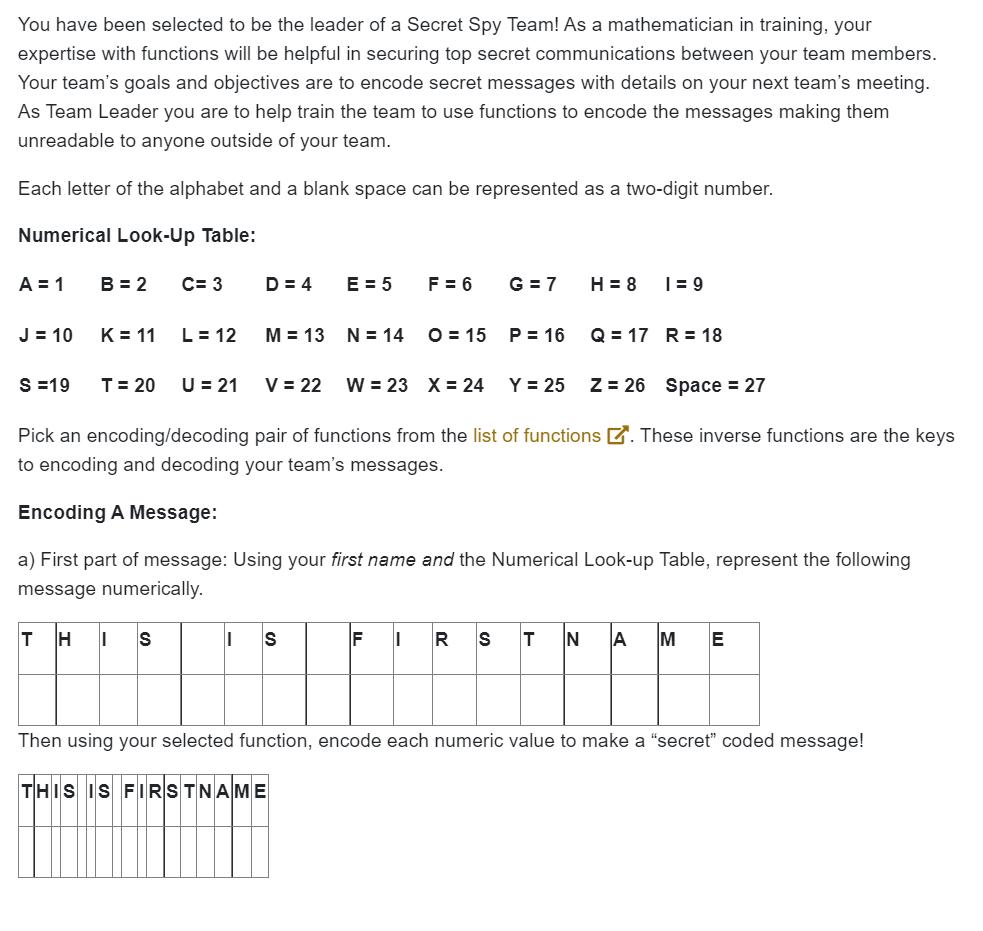
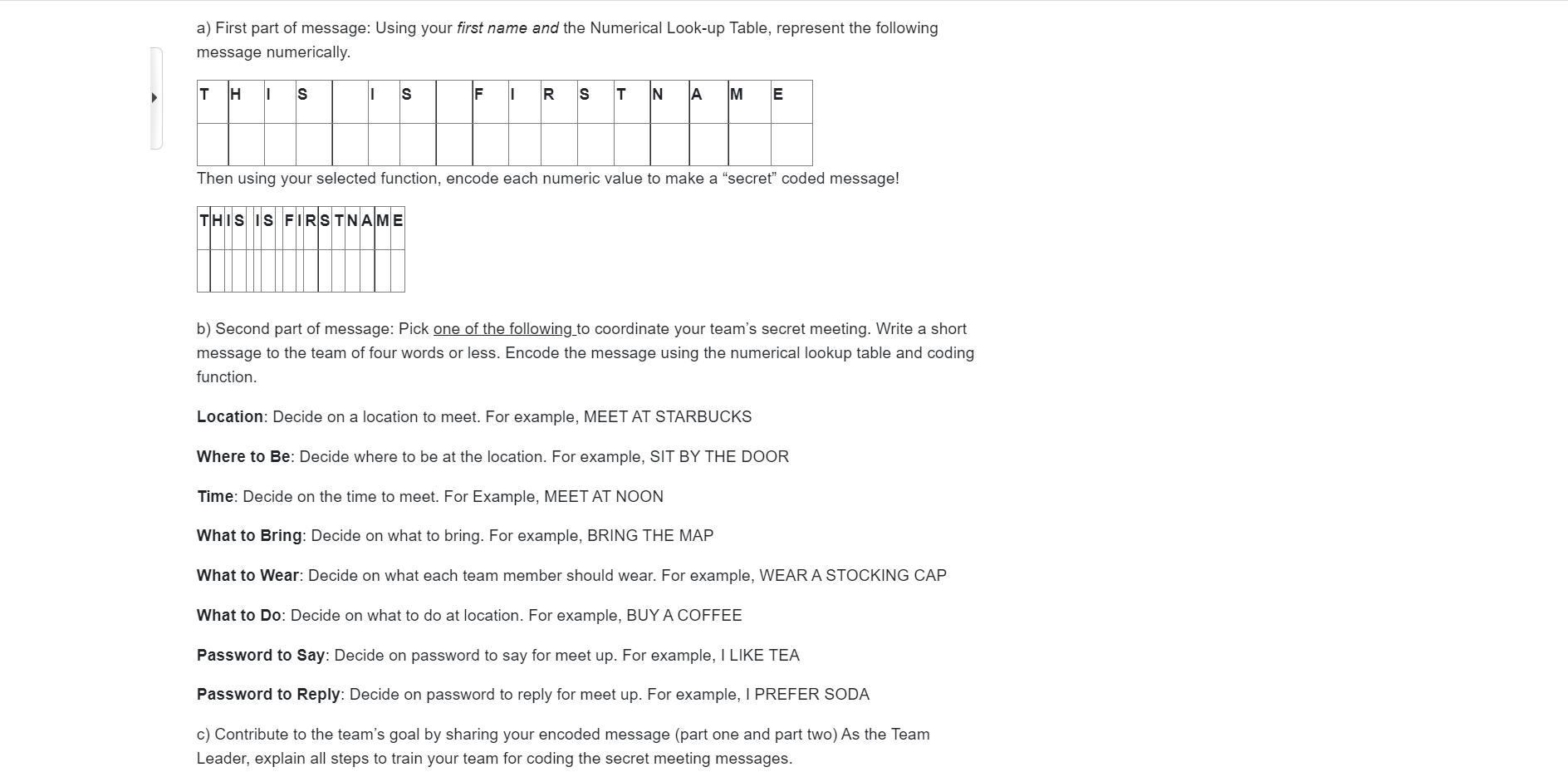
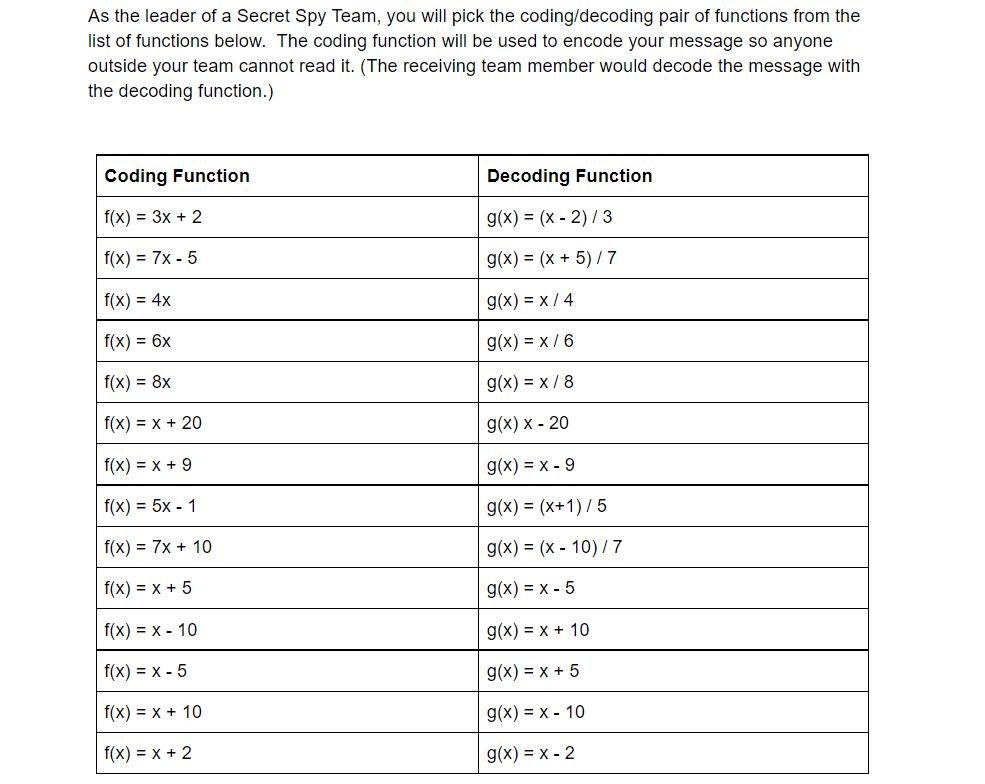
You have been selected to be the leader of a Secret Spy Team! As a mathematician in training, your expertise with functions will be helpful in securing top secret communications between your team members. Your team's goals and objectives are to encode secret messages with details on your next team's meeting. As Team Leader you are to help train the team to use functions to encode the messages making them unreadable to anyone outside of your team. Each letter of the alphabet and a blank space can be represented as a two-digit number. Numerical Look-Up Table: A = 1 J = 10 S =19 B = 2 K = 11 T = 20 C= 3 L=12 U = 21 D = 4 M = 13 E = 5 N = 14 || S F = 6 G=7 V = 22 W = 23 X = 24 Y = 25 O 15 P = 16 IF H = 8 1=9 Q = 17 R = 18 Pick an encoding/decoding pair of functions from the list of functions. These inverse functions are the keys to encoding and decoding your team's messages. Z = 26 Space = 27 Encoding A Message: a) First part of message: Using your first name and the Numerical Look-up Table, represent the following message numerically. THIS E Then using your selected function, encode each numeric value to make a "secret" coded message! THIS IS FIRSTNAME a) First part of message: Using your first name and the Numerical Look-up Table, represent the following message numerically. T HISI S F I STNA IM E Then using your selected function, encode each numeric value to make a "secret" coded message! THIS IS FIRSTNAME b) Second part of message: Pick one of the following to coordinate your team's secret meeting. Write a short message to the team of four words or less. Encode the message using the numerical lookup table and coding function. Location: Decide on a location to meet. For example, MEET AT STARBUCKS Where to Be: Decide where to be at the location. For example, SIT BY THE DOOR Time: Decide on the time to meet. For Example, MEET AT NOON What to Bring: Decide on what to bring. For example, BRING THE MAP What to Wear: Decide on what each team member should wear. For example, WEAR A STOCKING CAP What to Do: Decide on what to do at location. For example, BUY A COFFEE Password to Say: Decide on password to say for meet up. For example, I LIKE TEA Password to Reply: Decide on password to reply for meet up. For example, I PREFER SODA c) Contribute to the team's goal by sharing your encoded message (part one and part two) As the Team Leader, explain all steps to train your team for coding the secret meeting messages. As the leader of a Secret Spy Team, you will pick the coding/decoding pair of functions from the list of functions below. The coding function will be used to encode your message so anyone outside your team cannot read it. (The receiving team member would decode the message with the decoding function.) Coding Function f(x) = 3x + 2 f(x) = 7x-5 f(x) = 4x f(x) = 6x f(x) = 8x f(x) = x + 20 f(x) = x + 9 f(x) = 5x - 1 f(x) = 7x + 10 f(x) = x + 5 f(x) = x - 10 f(x) = x-5 f(x) = x + 10 f(x) = x + 2 Decoding Function g(x) = (x - 2)/3 g(x) = (x + 5)/7 g(x) = x/4 g(x) = x/6 g(x)=x/8 g(x) x - 20 g(x) = x - 9 g(x) = (x+1)/5 g(x) = (x-10) / 7 g(x) = x-5 g(x) = x + 10 g(x) = x + 5 g(x)= x 10 g(x) = x -2 You have been selected to be the leader of a Secret Spy Team! As a mathematician in training, your expertise with functions will be helpful in securing top secret communications between your team members. Your team's goals and objectives are to encode secret messages with details on your next team's meeting. As Team Leader you are to help train the team to use functions to encode the messages making them unreadable to anyone outside of your team. Each letter of the alphabet and a blank space can be represented as a two-digit number. Numerical Look-Up Table: A = 1 J = 10 S =19 B = 2 K = 11 T = 20 C= 3 L=12 U = 21 D = 4 M = 13 E = 5 N = 14 || S F = 6 G=7 V = 22 W = 23 X = 24 Y = 25 O 15 P = 16 IF H = 8 1=9 Q = 17 R = 18 Pick an encoding/decoding pair of functions from the list of functions. These inverse functions are the keys to encoding and decoding your team's messages. Z = 26 Space = 27 Encoding A Message: a) First part of message: Using your first name and the Numerical Look-up Table, represent the following message numerically. THIS E Then using your selected function, encode each numeric value to make a "secret" coded message! THIS IS FIRSTNAME a) First part of message: Using your first name and the Numerical Look-up Table, represent the following message numerically. T HISI S F I STNA IM E Then using your selected function, encode each numeric value to make a "secret" coded message! THIS IS FIRSTNAME b) Second part of message: Pick one of the following to coordinate your team's secret meeting. Write a short message to the team of four words or less. Encode the message using the numerical lookup table and coding function. Location: Decide on a location to meet. For example, MEET AT STARBUCKS Where to Be: Decide where to be at the location. For example, SIT BY THE DOOR Time: Decide on the time to meet. For Example, MEET AT NOON What to Bring: Decide on what to bring. For example, BRING THE MAP What to Wear: Decide on what each team member should wear. For example, WEAR A STOCKING CAP What to Do: Decide on what to do at location. For example, BUY A COFFEE Password to Say: Decide on password to say for meet up. For example, I LIKE TEA Password to Reply: Decide on password to reply for meet up. For example, I PREFER SODA c) Contribute to the team's goal by sharing your encoded message (part one and part two) As the Team Leader, explain all steps to train your team for coding the secret meeting messages. As the leader of a Secret Spy Team, you will pick the coding/decoding pair of functions from the list of functions below. The coding function will be used to encode your message so anyone outside your team cannot read it. (The receiving team member would decode the message with the decoding function.) Coding Function f(x) = 3x + 2 f(x) = 7x-5 f(x) = 4x f(x) = 6x f(x) = 8x f(x) = x + 20 f(x) = x + 9 f(x) = 5x - 1 f(x) = 7x + 10 f(x) = x + 5 f(x) = x - 10 f(x) = x-5 f(x) = x + 10 f(x) = x + 2 Decoding Function g(x) = (x - 2)/3 g(x) = (x + 5)/7 g(x) = x/4 g(x) = x/6 g(x)=x/8 g(x) x - 20 g(x) = x - 9 g(x) = (x+1)/5 g(x) = (x-10) / 7 g(x) = x-5 g(x) = x + 10 g(x) = x + 5 g(x)= x 10 g(x) = x -2
Expert Answer:

Related Book For 

Systems analysis and design
ISBN: ?978-1118808177
5th edition
Authors: Alan Dennis, Barbara Haley Wixom, Roberta m. Roth
Posted Date:
Students also viewed these general management questions
-
You have been selected to be the Project Manager (for a project of your choice). The project that you decide to use should meet the key criteria of a project, such as (a) having a beginning and an...
-
You have been selected to find the best client-server computing architecture for a Web-based order entry system that is being developed for L.L. Bean. Write a short memo that describes to the project...
-
You have been selected to represent the student body on a project to develop a new student database for your school. What is the first step in developing the database? What actions might you take to...
-
a. Show that if the position x of a moving point is given by a quadratic function of t, x = At 2 + Bt + C, then the average velocity over any time interval [t 1 , t 2 ] is equal to the instantaneous...
-
The Scholastic Aptitude Test (SAT), which is organized by the Educational Testing Service (ETS), is important to high school students seeking admission to colleges and universities throughout the...
-
For each of the following cost classification terms, give a definition and give one example of how the definition applies in practice to a person providing car repairs from a rented garage: (a)...
-
Time waveform collections should have settings that ensure how many full cycles of 1 running speed?
-
The comparative balance sheet of Navaria Inc. for December 31, 20Y3 and 20Y2, is shown as follows: Additional data obtained from an examination of the accounts in the ledger for 20Y3 are as follows:...
-
How does the use of dynamic process simulation differ from steady-state simulation, particularly in terms of modeling process transients and evaluating system robustness to disturbances ?
-
1. Why wasnt money an adequate remedy in this case? 2. What does Wilcox mean when he alleges that Shollmier engaged in collusion? 3. How could Wilcox have prevented the property from being sold below...
-
Question 8 (a) 4 Question k= (a) 13/2 Question (a) 1 (11-2| + |2|) da (b) 3.5 (c) 3 (d) 2 (e) none of these 9 Suppose that f, f(x) dx = = -4 = , 2g(r) dr. If k is a constant and f[3f(x) kg(r)] dr =...
-
One secondary channel for Apple computers is Best Buy. This channel addition expands Apples market presence. For participation credit, substantively discuss what challenges Apple faces/can face with...
-
On one graph show how supply and demand side market failures emerge. How does the market forces clear the failures for normal goods
-
A vacation rental company touts its five-star average rating. Sally writes a one-star review after a poor experience but notices it has been removed from the companys website the next day and...
-
Canadian inflation is currently 6 percent - next month it is projected to rise to 8 percent, The Canadian nominal interest rate is currently 10 percent - next month it is projected to fall to 9...
-
If the economy is moving too slowly, which economic problem is more likely to exist-high unemployment or high inflation? In this situation, should the federal government increase taxes or decrease...
-
Adelaide Ltd has the following sales forecast in units for the second half of the current year: June 24,000 July 22,000 August 26,000 September 30,000 At the end of each month the company requires: a...
-
What is the difference between adsorption and absorption?
-
Think about your school or local library and the processes involved in checking out books, signing up new borrowers, and sending out overdue notices, all from the librarys perspective. Describe three...
-
Why are interface standards important?
-
Create a use case diagram that would illustrate the use cases for the following online university registration system: The system should enable the staff members of each academic department to...
-
How is financial accounting different from management accounting?
-
As the new controller, reply to the following comment made by your plant manager: When I employ a proper accounting software, which can process all my daily accounting records and provide me with all...
-
Describe the five-step decision-making process.

Study smarter with the SolutionInn App