You need to generate the hashes of 16 sets of 3 random prime numbers less than 256.
Fantastic news! We've Found the answer you've been seeking!
Question:
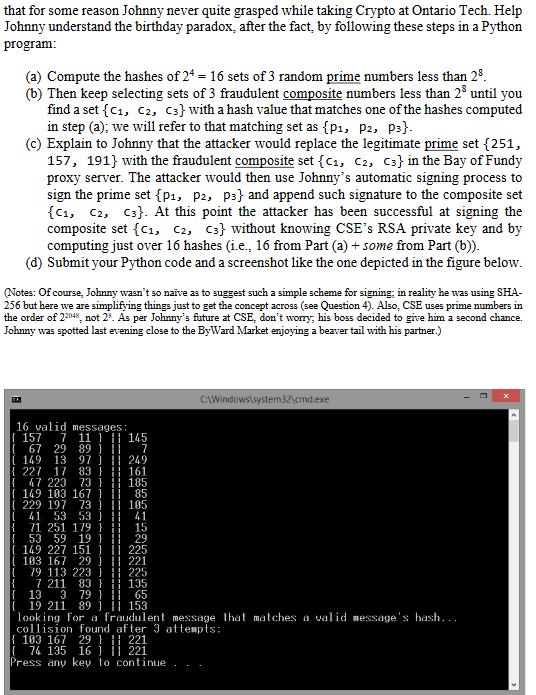
You need to generate the hashes of 16 sets of 3 random prime numbers less than 256. Then keep computing the hash value of different sets of 3 composite numbers less than 256 until you find a set that matches one of the 16 hash values of the random prime numbers. The formal definition of a "set" is "an unordered collection of distinct objects". This means a "set" has no repeated elements, and the order in which they are written doesn't matter. Therefore, no, there can't be repeated elements, and set {x, y, z} is the same as set {z, x, y}.
Transcribed Image Text:
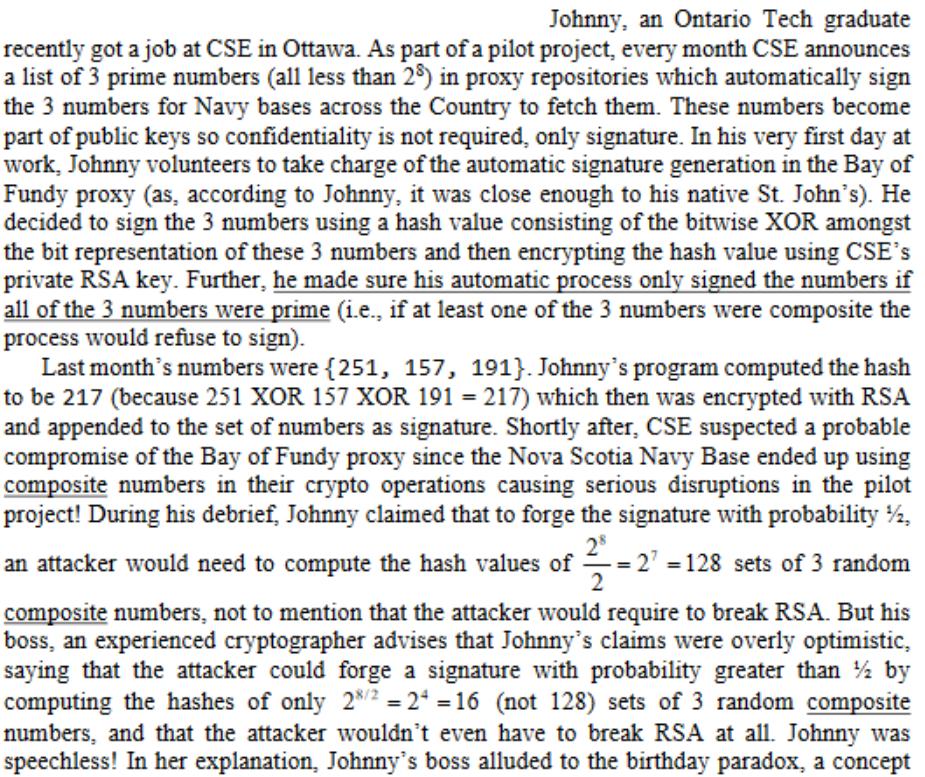
Johnny, an Ontario Tech graduate recently got a job at CSE in Ottawa. As part of a pilot project, every month CSE announces a list of 3 prime numbers (all less than 29) in proxy repositories which automatically sign the 3 numbers for Navy bases across the Country to fetch them. These numbers become part of public keys so confidentiality is not required, only signature. In his very first day at work, Johnny volunteers to take charge of the automatic signature generation in the Bay of Fundy proxy (as, according to Johnny, it was close enough to his native St. John's). He decided to sign the 3 numbers using a hash value consisting of the bitwise XOR amongst the bit representation of these 3 numbers and then encrypting the hash value using CSE's private RSA key. Further, he made sure his automatic process only signed the numbers if all of the 3 numbers were prime (i.e., if at least one of the 3 numbers were composite the process would refuse to sign). Last month's numbers were {251, 157, 191}. Johnny's program computed the hash to be 217 (because 251 XOR 157 XOR 191 = 217) which then was encrypted with RSA and appended to the set of numbers as signature. Shortly after, CSE suspected a probable compromise of the Bay of Fundy proxy since the Nova Scotia Navy Base ended up using composite numbers in their crypto operations causing serious disruptions in the pilot project! During his debrief, Johnny claimed that to forge the signature with probability ½, 28 an attacker would need to compute the hash values of =2' =128 sets of 3 random composite numbers, not to mention that the attacker would require to break RSA. But his boss, an experienced cryptographer advises that Johnny's claims were overly optimistic, saying that the attacker could forge a signature with probability greater than % by computing the hashes of only 2*2 = 2* = 16 (not 128) sets of 3 random composite numbers, and that the attacker wouldn't even have to break RSA at all. Johnny was speechless! In her explanation, Johnny's boss alluded to the birthday paradox, a concept Johnny, an Ontario Tech graduate recently got a job at CSE in Ottawa. As part of a pilot project, every month CSE announces a list of 3 prime numbers (all less than 29) in proxy repositories which automatically sign the 3 numbers for Navy bases across the Country to fetch them. These numbers become part of public keys so confidentiality is not required, only signature. In his very first day at work, Johnny volunteers to take charge of the automatic signature generation in the Bay of Fundy proxy (as, according to Johnny, it was close enough to his native St. John's). He decided to sign the 3 numbers using a hash value consisting of the bitwise XOR amongst the bit representation of these 3 numbers and then encrypting the hash value using CSE's private RSA key. Further, he made sure his automatic process only signed the numbers if all of the 3 numbers were prime (i.e., if at least one of the 3 numbers were composite the process would refuse to sign). Last month's numbers were {251, 157, 191}. Johnny's program computed the hash to be 217 (because 251 XOR 157 XOR 191 = 217) which then was encrypted with RSA and appended to the set of numbers as signature. Shortly after, CSE suspected a probable compromise of the Bay of Fundy proxy since the Nova Scotia Navy Base ended up using composite numbers in their crypto operations causing serious disruptions in the pilot project! During his debrief, Johnny claimed that to forge the signature with probability ½, 28 an attacker would need to compute the hash values of =2' =128 sets of 3 random composite numbers, not to mention that the attacker would require to break RSA. But his boss, an experienced cryptographer advises that Johnny's claims were overly optimistic, saying that the attacker could forge a signature with probability greater than % by computing the hashes of only 2*2 = 2* = 16 (not 128) sets of 3 random composite numbers, and that the attacker wouldn't even have to break RSA at all. Johnny was speechless! In her explanation, Johnny's boss alluded to the birthday paradox, a concept
Expert Answer:
Posted Date:
Students also viewed these accounting questions
-
You need to generate five uniform random numbers. (a) Prepare to do this by using the mixed congruential method to generate a sequence of five random integer numbers between 0 and 31 such that xn+1 ...
-
Rearrange the following titles in the order in which they would appear in a trial balance: J. Joy, Withdrawals Accounts Receivable Cash J. Joy, Capital Office Equipment Hair Salon Fees Earned Utility...
-
Cranberries are harvested by flooding the bogs in which they are grown and raking them into troughs for transport. At the processing plant, the surface moisture on the berries is removed as they roll...
-
Preparing and interpreting a statement of cash flows using a T-account work sheet. Financial statement data for Dickerson Manufacturing Company for the current year appear in Exhibit 5.29. Additional...
-
Under which perspective of the balanced scorecard would you classify each of the following measurements? a. On-time delivery to customers b. Time to develop the next generation of products c....
-
Henning Appliances use the periodic inventory system. Details regarding the inventory of appliances at January 1, 2006, purchases invoices during the year, and the inventory count at December 31,...
-
Assume that you are thinking about opening a musical instruments store near the college or university you are attending. Guitars, drums, and other types of musical instruments are items you would...
-
Analysis of Subsequent Expenditures Accardo Resources Group has been in its plant facility for 15 years. Although the plant is quite functional, numerous repair costs are incurred to maintain it in...
-
For this exercise, instead of using the values in the challenge, ask the user for the number of shares, the share price, and the percent commission.For this exercise, instead of using the values in...
-
The file P17_19.xlsx contains various data on 325 metropolitan cities in the United States. Cell comments in row 1 explain some of the variables. A Microsoft Data Mining add-in (not discussed here)...
-
What is the role of fluorescein and rhodamine B in Experiment 9?
-
Parents of minors took Apple to court in 2012 for supplying game applications, on iPhones, that were free but through which users could purchase in-game currencies. Apparently, parents would log on...
-
Rockstar Games, a subsidiary of Take-Two Interactive, released the video game Grand Theft Auto V in 2013. The game features a character named Lacey Jonas, a self-proclaimed actress slash singer and...
-
On June 28, 1997, in Las Vegas, heavyweight boxers Mike Tyson and Evander Holyfield met for what proved to be a night to remember. During the third round of the fight, a desperate Tyson illegally bit...
-
Sabrina Ederly worked as a reporter and contributing editor for Rolling Stone magazine. Ederly intended to write an article for the magazine that focused on the alleged rape of a University of...
-
How might a hacker access and manipulate a digital device for illegal purposes? Are the Internet of Things (IoT) devices at risk for hacker access and manipulation?
-
GT Leaders set the tone for others. How would your students, colleagues, and administrators describe the tone you set? What specific actions do you take to set and maintain that tone? *
-
Discuss the information available from the following techniques in the analysis of inorganic pigments used in antique oil paintings: (i) Powder X-ray diffraction, (ii) Infrared and Raman...
-
Identify the sample.
-
Test the overall significance of a regression model and identify the components of this test from your computer output.
-
Based on the strategy, what type of sampling technique will be used to identify the sample? a. Why did you choose this type of technique?

Study smarter with the SolutionInn App


