Question: What algorithm does the following pseudocode perform? Declare Integer maxElement Declare Integer index For maxElement = For index arraySize - 1 To 0 Step 1
What algorithm does the following pseudocode perform?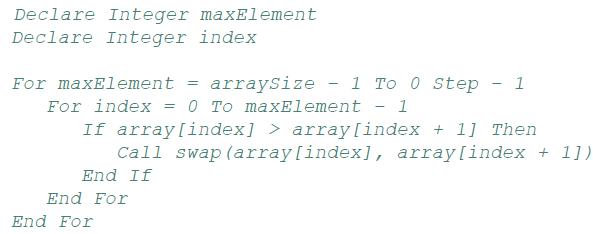
Declare Integer maxElement Declare Integer index For maxElement = For index arraySize - 1 To 0 Step 1 0 To maxElement - 1 = End For If array[index]> array[index + 1] Then Call swap (array[index], array[index + 1]) End If End For
Step by Step Solution
3.26 Rating (155 Votes )
There are 3 Steps involved in it
The pseudocode you provided does not perform any algorithm It is a fragment of code that is missing ... View full answer

Get step-by-step solutions from verified subject matter experts


