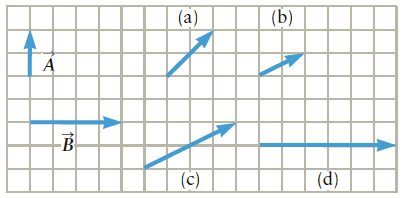
Question: Which vector in Figure P1.51 might equal A(vector) + B(vector)? Figure P1.51 ? (a) (b) -B (c) (d)
Which vector in Figure P1.51 might equal A(vector) + B(vector)?
Figure P1.51
 ?
?
(a) (b) -B (c) (d)
Step by Step Solution
3.37 Rating (163 Votes )
There are 3 Steps involved in it
The graphical sum of vectors is identified by orienting the v... View full answer

Get step-by-step solutions from verified subject matter experts


