Question: Assume a datagram carries no option. Do we still need a value for the next header field in Figure 22.7 ? Figure 22.7 Payload in
Assume a datagram carries no option. Do we still need a value for the next header field in Figure 22.7?
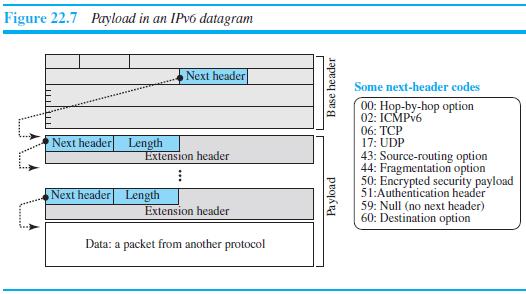
Figure 22.7 Payload in an IPV6 datagram Next header Some next-header codes 00: Hop-by-hop option 02: ICMPV6 Next header Length 06: TCP 17: UDP Extension header 43: Source-routing option 44: Fragmentation option 50: Encrypted security payload 51:Authentication header 59: Null (no next header) 60: Destination option Next header Length Extension header Data: a packet from another protocol Payload Base header
Step by Step Solution
3.36 Rating (159 Votes )
There are 3 Steps involved in it
We still needs the ... View full answer

Get step-by-step solutions from verified subject matter experts


