Question: In Fig. 6-36 we saw that in addition to the 32-bit acknowledgement field, there is an ACK bit in the fourth word. Does this really
In Fig. 6-36 we saw that in addition to the 32-bit acknowledgement field, there is an ACK bit in the fourth word. Does this really add anything? Why or why not?
Figure 6-36
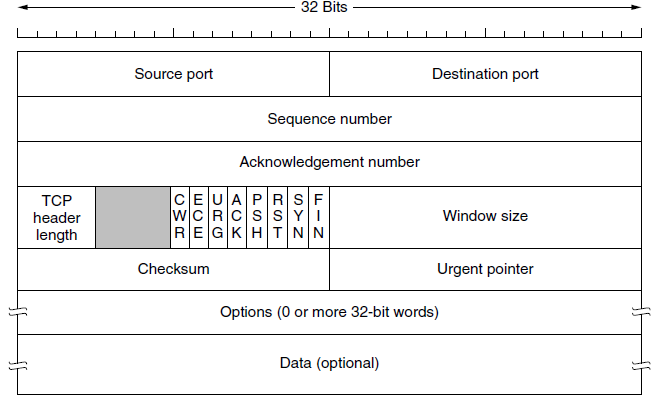
32 Bits Source port Destination port Sequence number Acknowledgement number CEUAPRS F WCRCSSYI REGKHTNN TCP Window size header length Checksum Urgent pointer Options (0 or more 32-bit words) Data (optional)
Step by Step Solution
3.27 Rating (156 Votes )
There are 3 Steps involved in it
The ACK bit is used to tell whether the 32bit field is used But if it were not ... View full answer

Get step-by-step solutions from verified subject matter experts


