Question: In Figure 31.9, we have two straight permutation operations: initial permutation and final permutation. Experts believe these operations are useless and do not help to
In Figure 31.9, we have two straight permutation operations: initial permutation and final permutation. Experts believe these operations are useless and do not help to make the cipher stronger. Can you find the reason for this statement?
Figure 31.9
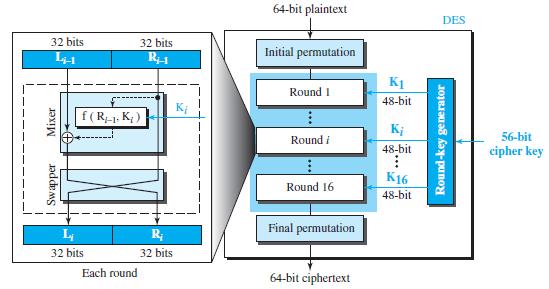
64-bit plaintext DES 32 bits 32 bits Initial permutation K1 Round I 48-bit f( R1. K; ) K; Round i 56-bit 48-bit cipher key K16 Round 16 48-bit Final permutation 32 bits 32 bits Each round 64-bit ciphertext
Step by Step Solution
3.44 Rating (173 Votes )
There are 3 Steps involved in it
Both operations are keyless ... View full answer

Get step-by-step solutions from verified subject matter experts


