Question: In the Internet File Server example (Figure 6-6), can the connect( ) system call on the client fail for any reason other than listen queue
Figure 6-6
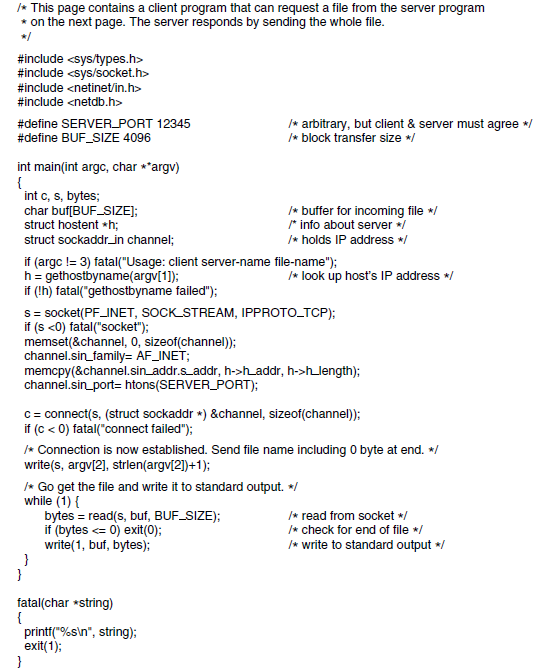
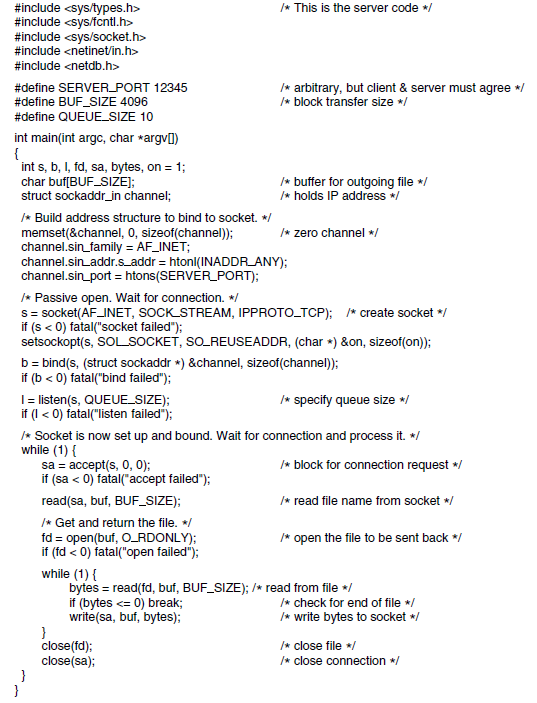
* This page contains a client program that can request a file from the server program * on the next page. The server responds by sending the whole file. */ #include #include #include #include #define SERVER_PORT 12345 #define BUF_SIZE 4096 /* arbitrary, but client & server must agree */ /* block transfer size */ int main(int argc, char **argv) { int c, s, bytes; char buf[BUF_SIZEJ; struct hostent *h; /* buffer for incoming file / * info about server */ struct sockaddr_in channel; /* holds IP address */ if (argc != 3) fatal("Usage: client server-name file-name"); h = gethostbyname(argv[1]); if (!h) fatal("gethostbyname failed"); /* look up host's IP address */ S = socket(PF_INET, SOCK STREAM, IPPROTO_TCP); if (s haddr, h->hlength); channel.sin_port= htons(SERVER_PORT); c= connect(s, (struct sockaddr *) &channel, sizeof(channel)); if (c < 0) fatal("connect failed"); /* Connection is now established. Send file name including O byte at end. */ write(s, argv[2], strlen(argv[2])+1); I* Go get the file and write it to standard output. */ while (1) { bytes = read(s, buf, BUF_SIZE); if (bytes
Step by Step Solution
3.47 Rating (180 Votes )
There are 3 Steps involved in it
The connect ma... View full answer

Get step-by-step solutions from verified subject matter experts


