Question: Recall that we the Internet checksum being used in both transport-layer segment (in UDP and TCP headers, Figures 3.7 and 3.29 respectively) and in network-layer
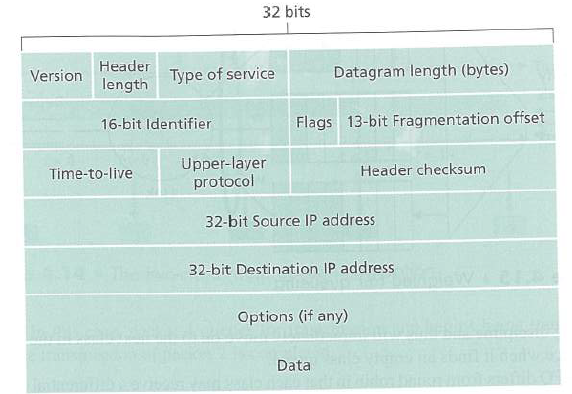
Recall that we the Internet checksum being used in both transport-layer segment (in UDP and TCP headers, Figures 3.7 and 3.29 respectively) and in network-layer data-grarns (IP header, Figure 4.16). Now consider a transport layer segment encapsulated in an IP data-gram. Are the check-sums in the segment header and data-gram header computed over any common bytes in the IP data-gram? Explain your answer.
Figure 3.7
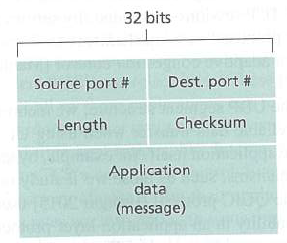
Figure 3.29
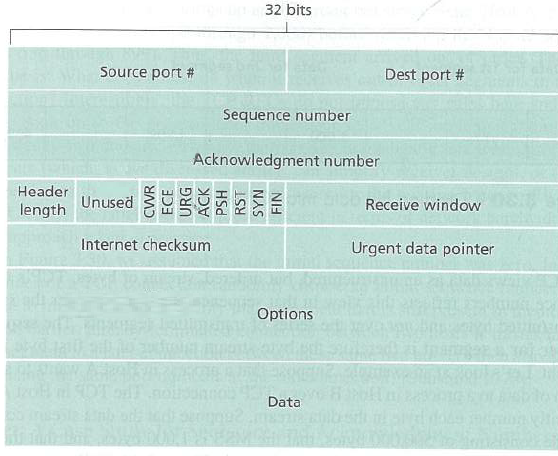
Figure 4.16
32 bits Dest. port # Source port # Checksum Length Application data (message) 32 bits Source port # Dest port # Sequence number Acknowledgment number Header Unused 3 Receive window length Internet checksum Urgent data pointer Options Data NIH NAS HSd ACK URG
Step by Step Solution
3.43 Rating (166 Votes )
There are 3 Steps involved in it
No IP header checksum only compu... View full answer

Get step-by-step solutions from verified subject matter experts


