Question: Redo the checksum in Figure 19.11 using decimal values and modular arithmetic. Figure 19.11 Example of checksum calculation 8 9 TEST 8 & 0 00001000
Redo the checksum in Figure 19.11 using decimal values and modular arithmetic.
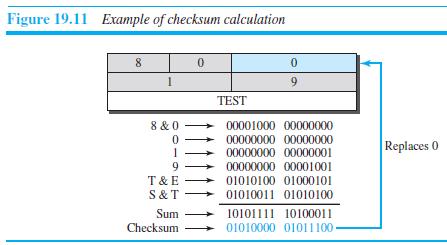
Figure 19.11 Example of checksum calculation 8 9 TEST 8 & 0 00001000 00000000 00000000 00000000 00000000 00000001 Replaces 0 9. 00000000 00001001 T & E 01010100 01000101 S& T 01010011 01010100 Sum 10101111 10100011 Checksum 01010000 01011100-
Step by Step Solution
3.35 Rating (161 Votes )
There are 3 Steps involved in it
We show the value of each word in decimal and then add them to get t... View full answer

Get step-by-step solutions from verified subject matter experts


