In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when each word
Question:
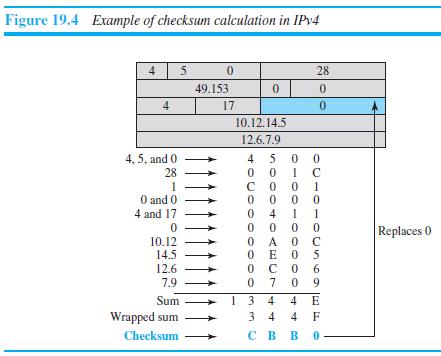
In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when each word (16 bits) is created instead of waiting for the whole packet to be created.
Transcribed Image Text:
Figure 19.4 Example of checksum calculation in IPV4 4 5 0. 28 49.153 0. 4 17 10.12.14.5 12.6.7.9 4 5 0 0 4, 5, and 0 28 1 O and 0 4 and 17 1 0 0 O A 0 C O E O 5 с о 0 9 4 Replaces 0 10.12 14.5 12.6 6. 7.9 7 1 3 4 3 4 Sum 4 E Wrapped sum 4 F Checksum св в о. 0-00-0
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (6 reviews)
We can calculate the sum wrapped sum and checksum after each word if we keep track of the sum i...View the full answer

Answered By

Sarfraz gull
have strong entrepreneurial and analytical skills which ensure quality tutoring and mentoring in your international business and management disciplines. Over last 3 years, I have expertise in the areas of Financial Planning, Business Management, Accounting, Finance, Corporate Finance, International Business, Human Resource Management, Entrepreneurship, Marketing, E-commerce, Social Media Marketing, and Supply Chain Management.
Over the years, I have been working as a business tutor and mentor for more than 3 years. Apart from tutoring online I have rich experience of working in multinational. I have worked on business management to project management.
5.00+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Show how the sum of two five-bit integers can be found using full and half adders.
-
In Figure 11.9, we show the packet path as a horizontal line, but the frame path as a diagonal line. Can you explain the reason? Figure 11.9 Sending node Receiving node Network Network Data-link...
-
Suppose, instead of waiting for the economy described in question 13 to return to long-run equilibrium, the central bank opted to use the positive supply shock as an opportunity to move to a lower...
-
If Converse introduced a new SMART WATCH for Men and Women, should they launch the product using Market Skimming or Marketing Penetration? Explain answer
-
Aquatech is a U.S.-based company that manufactures, sells, and installs water purification equipment. On April 11, the company sold a system to the City of Nagasaki, Japan, for installation in...
-
A 12-m-long and 5-m-high wall is constructed of two layers of 1-cm-thick sheetrock (k = 0.17 W/mK) spaced 16 cm by wood studs (k = 0.11 W/mK) whose cross section is 16 cm 5 cm. The studs are placed...
-
Describe in what ways the scope of nursing has changed.
-
Ken, a salaried employee, was terminated from his company in April of this year. Business had been slow since the beginning of the year, and each of the operating plants had laid off workers. Ken's...
-
14. Find the magnitude of the torque vector, measured in Newton-meters, produced by a cyclist exerting a force of F = [60, 15, 105]N on the shaft-petal = [10, 13, 50]cm long. Recall: 7=7x F
-
Thomas was raised with an understanding of the fundamental differences between right and wrong. As an adult, he wasn't making enough money to purchase a new car as quickly as he liked. He found out...
-
Mention the three auxiliary protocols at the network layer of the TCP/IP suite that are designed to help the IPv4 protocol.
-
In an IPv4 datagram, the value of the header-length (HLEN) field is (6) 16 . How many bytes of options have been added to the packet?
-
Write each expression in simplest radical form. If a radical appears in the denominator, rationalize the denominator. 4 x 104
-
Extend the Binary Search Tree ADT to include a Boolean function SimilarTrees that receives pointers to two binary trees and determines whether the shapes of the trees are the same. (The nodes do not...
-
When the financial controller of Bakers Company set the budget for the year ahead, it was expected that monthly output of cake packages would be 12,000 units. In March the output was increased to...
-
Given the following array, draw the binary tree that can be created from its elements. The elements are arranged in the array as discussed in the chapter. tree.elements [0] [1] [2] [3] [4] [5] [6]...
-
Determine the Big-O measure for SelectionSort based on the number of elements moved rather than the number of comparisons 1. for the best case. 2. for the worst case.
-
Write a client function that returns a count of the nodes that contain a value less than the parameter value.
-
Locate one of the online job websites and pick several job listings. For each job type, discuss one or more situations in which statistical analyses would be used. Base your answer on research...
-
What is beacon marketing? What are digital wallets?
-
A token bucket scheme is used for traffic shaping. A new token is put into the bucket every 5 sec. Each token is good for one short packet, which contains 48 bytes of data. What is the maximum...
-
The network of Fig. 5-34 uses RSVP with multicast trees for hosts 1 and 2 as shown. Suppose that host 3 requests a channel of bandwidth 2 MB/sec for a flow from host 1 and another channel of...
-
A router can process 2 million packets/sec. The load offered to it is 1.5 million packets/ sec on average. If a route from source to destination contains 10 routers, how much time is spent being...
-
You have just made your first $5,200 contribution to your retirement account. Assume you earn a return of 12 percent per year and make no additional contributions. a. What will your account be worth...
-
There are two components of leadership. The first is your own personal style and the second is how you choose to lead. Use the following checklist to evaluate your leadership style: What Kind of a...
-
Selected Realized Returns, 1926-2017 Average Return Standard Deviation Small-cap stocks 16.5% 31.7% Large-cap stocks 12.1 19.8 Long-term corporate bonds 6.4 8.3 Long-term government bonds 6.0 9.9...

Study smarter with the SolutionInn App


