Question: Redraw Figure 11.10 using piggybacking. Figure 11.10 Receiving node Frame Sending node ACK Network Network LCRC [CRC Data-link Data-link Logical link (duplex) Timer
Figure 11.10
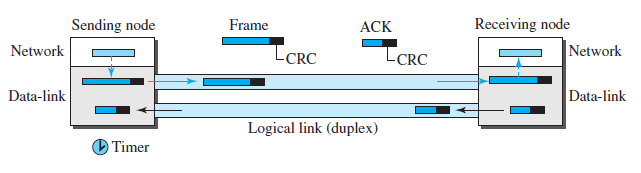
Receiving node Frame Sending node ACK Network Network LCRC [CRC Data-link Data-link Logical link (duplex) Timer
Step by Step Solution
3.43 Rating (166 Votes )
There are 3 Steps involved in it
The following figures shows t... View full answer

Get step-by-step solutions from verified subject matter experts


