Question: Redraw Figure 19.18 for the case where the mobile host acts as a foreign agent. Figure 19.18 Data transfer Home network Mobile host Remote network
Redraw Figure 19.18 for the case where the mobile host acts as a foreign agent.
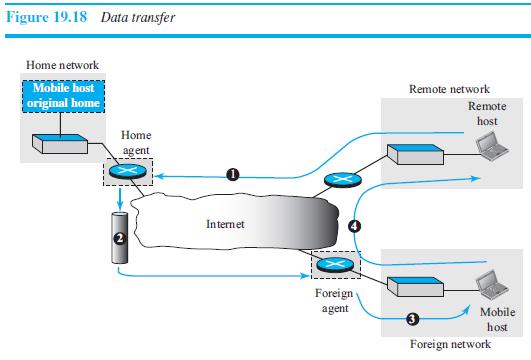
Figure 19.18 Data transfer Home network Mobile host Remote network original home Remote host Home ag ent Internet Foreign agent Mobile host Foreign network
Step by Step Solution
3.42 Rating (171 Votes )
There are 3 Steps involved in it
See the following figure Hom... View full answer

Get step-by-step solutions from verified subject matter experts


