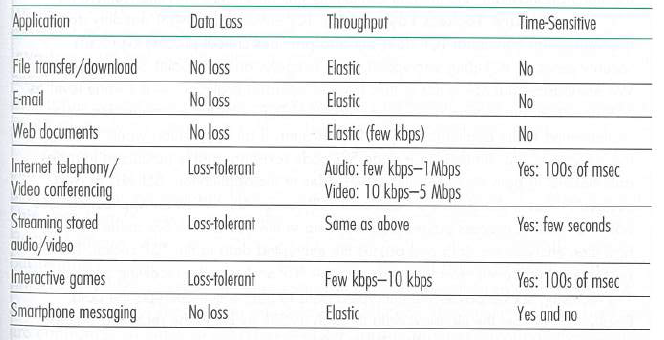
Referring to Figure 2.4, we see that none of the applications listed in Figure 2.4 requires both
Question:
Figure 2.4
Transcribed Image Text:
Application Throughput Data Loss Time-Sensitive File transfer/download No loss Elastic No Email No loss Elastic No Web documents No loss Elostic (few kbps) No Internet telephony/ Video conferencing Audio: few kbps-1 Mbps Video: 10 kbps-5 Mbps Loss-tolerant Yes: 100s of msec Streaming stored audio/vidao Loss-tolerant Same as above Yes: few seconds Interactive games Few kbps-10 kbps Loss-tolerant Yes: 100s of msec Smartphone messaging No loss Elostic Yes and no
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 60% (15 reviews)
One such example is remote word p...View the full answer

Answered By

Allan Olal
I have vast tutoring experience of more than 8 years and my primary objective as a tutor is to ensure that a student achieves their academic goals.
4.70+
78+ Reviews
412+ Question Solved
Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Question Posted:
Students also viewed these Computer science questions
-
With reference to Table 2.4, we see that the relative performance of the IBM 360 Model 75 is 50 times that of the 360 Model 30, yet the instruction cycle time is only 5 times as fast. How do you...
-
During the course of an algorithm, we sometimes find that we need to maintain past versions of a dynamic set as it is updated. Such a set is called persistent. One way to implement a persistent set...
-
We are given a noisy signal x(t) = s(t) + η(t) where s(t) is the desired signal and η(t) is additive noise. From experience, we know that the average power of the desired...
-
1.3 WANEFMAC7 1.3.007. Find the equation of the given linear function. \[ f(x)= \] WANEFMAC7 1.3.015. Find the slope of the given line, if it is defined. (If an answer is undefined, enter UNDEFINED.)...
-
1. How did the California legislature define the term "completion"? Was this definition clear? Discuss. 2. How did the owner of the project at the center of this case want the court to interpret...
-
Identify the models explained in this chapter and their relationship to each other.
-
Investigate the contribution of workforce metrics and analytics
-
Suppose that we modify the model of the firm's investment behavior by assuming that any capital the firm has remaining at the end of the period can be sold at the price p'K (in our model we assumed...
-
Where did you get 3 2 per unit and 2 2 per unit when calculating the costs?
-
A baseball player's slugging percentage SLG can be calculated with the following formula (which is an example of a rational function): SLG = H+2B+2x(3B)+3x(HR) AB Q Image transcription text H+2B+2x...
-
Consider a TCP connection between Host A and Host B. Suppose that the TCP segments traveling from Host A to Host B have source port number x and destination port number y. What are the source and...
-
SMS, iMessage. and WhatsApp are ail smartphone real-time messaging systems. After doing some research on the Internet, for each of these systems write one paragraph about the protocols they use. Then...
-
Consider a project in which you are currently involved (or in which you have recently been involved). a. Describe the objectives, scope, schedule, cost, and any assumptions made. b. Where are you in...
-
A certain random process \(U(t)\) takes on equally probable values +1 or 0 with changes occurring randomly in time. The probability that \(n\) changes occur in time \(\tau\) is known to be \[...
-
The focal points of the two converging lenses shown in Figure P33.121 are denoted by solid dots for the left lens and open dots for the right lens. Draw a simplified ray diagram to locate the final...
-
Suppose that country A has 9,000 worker hours available for production and that it initially has the technology given by case 3 of Exercise 1. Derive its PPF and determine its exact dimensions. data...
-
The table shows experimental values of the variables x and y. The variables are known to be related by the equation y = a e nx where a and n are constants. a. Draw the graph of ln y against x. b....
-
Construct the Nyquist diagram for a single-degree-of-freedom system with hysteretic damping.
-
In Exercise use a graphing utility to graph the function and estimate the limit (if it exists). What is the domain of the function? Can you detect a possible error in determining the domain of a...
-
Assume Eq. 6-14 gives the drag force on a pilot plus ejection seat just after they are ejected from a plane traveling horizontally at 1300 km/h. Assume also that the mass of the seat is equal to the...
-
Assume PPP is in the authentication phase, show payload exchanged between the nodes if PPP is using a. PAP b. CHAP
-
Define piggybacking and its benefit.
-
Assume the only computer in the residence uses PPP to communicate with the ISP. If the user sends 10 network-layer packets to ISP, how many frames are exchanged in each of the following cases: a....
-
Practice Problem 1 The stockholders equity accounts of Bramble Corp. on January 1, 2017, were as follows. Preferred Stock (6%, $100 par noncumulative, 4,400 shares authorized) $264,000 Common Stock...
-
JVCU Which of the following is considered cash for financial reporting purposes? 1 JVCU Which of the following is considered cash for financial reporting purposes? 1
-
Required information The Foundational 15 [LO8-2, LO8-3, LO8-4, LO8-5, LO8-7, LO8-9, L08-10) (The following information applies to the questions displayed below.) Morganton Company makes one product...

Study smarter with the SolutionInn App


