Question: The actual layout of cells is seldom as regular that as shown in Fig. 2-45. Even the shapes of individual cells are typically irregular. Give
The actual layout of cells is seldom as regular that as shown in Fig. 2-45. Even the shapes of individual cells are typically irregular. Give a possible reason why this might be. How do these irregular shapes affect frequency assignment to each cell?
Figure 2-45
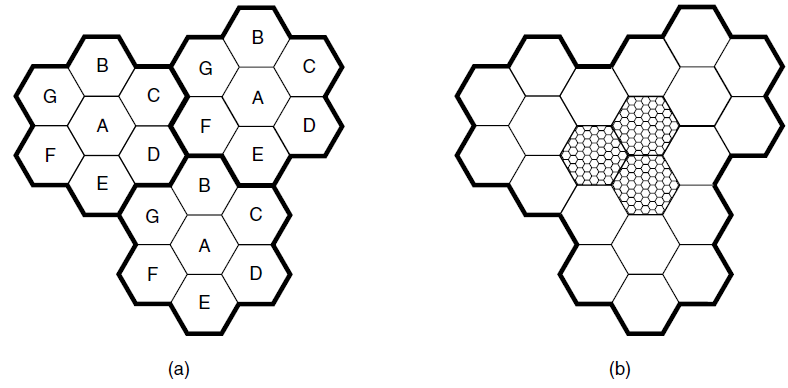
B B G G A D A B G D (a) (b)
Step by Step Solution
3.45 Rating (155 Votes )
There are 3 Steps involved in it
First initial deployment simply placed cells in regions where there was a high density of human or v... View full answer

Get step-by-step solutions from verified subject matter experts


