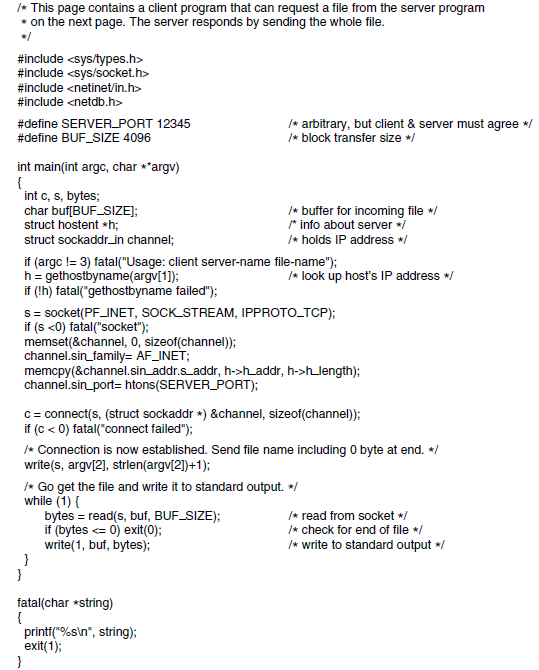
Question: The file server of Fig. 6-6 is far from perfect and could use a few improvements. Make the following modifications.(a) Give the client a third
The file server of Fig. 6-6 is far from perfect and could use a few improvements. Make the following modifications.(a) Give the client a third argument that specifies a byte range.(b) Add a client flag ?w that allows the file to be written to the server.
Figure 6-6
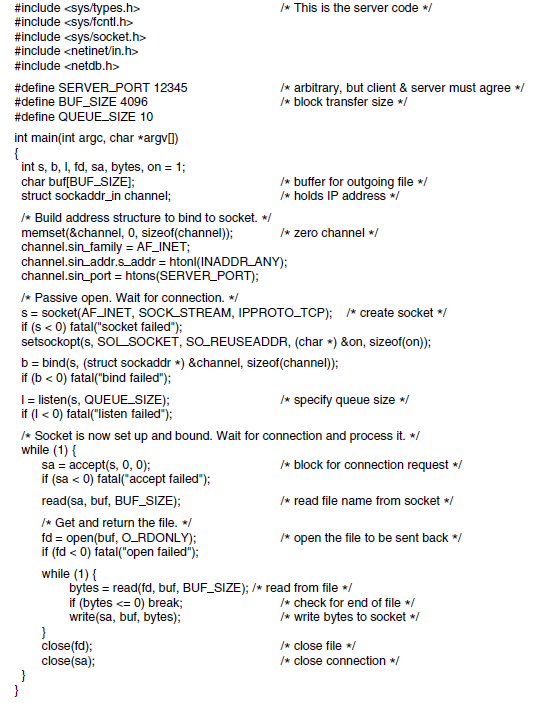
#include #include #include #include /* This is the server code / #include #define SERVER PORT 12345 /* arbitrary, but client & server must agree */ /* block transfer size */ #define BUF_SIZE 4096 #define QUEUE SIZE 10 int main(int argc, char *argv]) { int s, b, I, fd, sa, bytes, on = 1; char buf[BUF_SIZEJ; struct sockaddr_in channel; I* buffer for outgoing file / /* holds IP address */ /* Build address structure to bind to socket. */ memset(&channel, 0, sizeof(channel)); channel.sin_family = AF_INET; channel.sin_addr.s_addr = htonl(INADDRANY); channel.sin_port = htons(SERVER_PORT); /* zero channel */ * Passive open. Wait for connection. */ S = socket(AF_INET, SOCK STREAM, IPPROTO_TCP); * create socket */ if (s < 0) fatal("socket failed"); setsockopt(s, SOLSOCKET, SO REUSEADDR, (char ) &on, sizeof(on)); b= bind(s, (struct sockaddr *) &channel, sizeof(channel)); if (b < 0) fatal("bind failed"); I= isten(s, QUEUE_SIZE); if (I < 0) fatal("listen failed"); /* Socket is now set up and bound. Wait for connection and process it. */ while (1) { sa = accept(s, 0, 0); if (sa < 0) tatal("accept failed"); /* specify queue size */ /* block for connection request / read(sa, buf, BUF_SIZE); /* read file name from socket */ /* Get and return the file. */ fd = open(buf, O_RDONLY); if (fd < 0) tatal("open failed"); /* open the file to be sent back */ while (1) { bytes = read(fd, buf, BUF_SIZE); /* read from file */ if (bytes
Step by Step Solution
3.34 Rating (160 Votes )
There are 3 Steps involved in it
a To give the client a third argument that specifies a byte range we can modify the clientserver co... View full answer

Get step-by-step solutions from verified subject matter experts


