Question: For problems below, use the information about access time for every type of memory in the following table. Find how long it takes to read
For problems below, use the information about access time for every type of memory in the following table.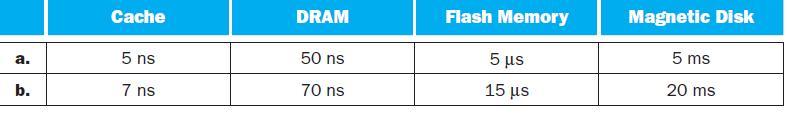
Find how long it takes to read a file from a DRAM if it takes 2 microseconds from the cache memory.
a. b. Cache 5 ns 7 ns DRAM 50 ns 70 ns Flash Memory 5 15 s Magnetic Disk 5 ms 20 ms
Step by Step Solution
3.50 Rating (160 Votes )
There are 3 Steps involved in it
To find out how long it takes to read a file from DRAM when it takes 2 micr... View full answer

Get step-by-step solutions from verified subject matter experts


