Question: Consider the following fragment in an authentication program What type of malicious software is this? username password = read_username (); read_password(); if username is 133t
Consider the following fragment in an authentication program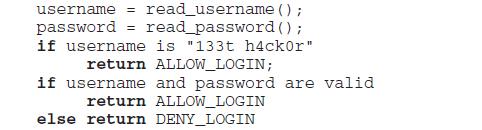
What type of malicious software is this?
username password = read_username (); read_password(); if username is "133t h4ckor" return ALLOW_LOGIN; if username and password are valid return ALLOW_LOGIN else return DENY_LOGIN =
Step by Step Solution
3.53 Rating (146 Votes )
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


