Consider the following fragment: What type of malicious software is this? legitimate code if data is Friday
Question:
Consider the following fragment: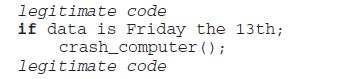
What type of malicious software is this?
Transcribed Image Text:
legitimate code if data is Friday the 13th; (); crash_computer legitimate code
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)

Answered By

Bhartendu Goyal
Professional, Experienced, and Expert tutor who will provide speedy and to-the-point solutions. I have been teaching students for 5 years now in different subjects and it's truly been one of the most rewarding experiences of my life. I have also done one-to-one tutoring with 100+ students and help them achieve great subject knowledge. I have expertise in computer subjects like C++, C, Java, and Python programming and other computer Science related fields. Many of my student's parents message me that your lessons improved their children's grades and this is the best only thing you want as a tea...
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
8. Which term describes an action that can damage or compromisean asset? A. Risk B. Vulnerability C. Countermeasure D. Threat 10. Which type of attack involves the creation of some deceptionin order...
-
Consider the following fragment in an authentication program What type of malicious software is this? username password = read_username (); read_password(); if username is "133t h4ckor" return...
-
Q3: Prove: For any sets A and B, Ax B = B A ?
-
The refrigerant fluid R-21 (see Table A.2) is to be used as the working fluid in a solar energy powered Rankine-cycle type power plant. Saturated liquid R-21 enters the pump, state 1, at 25oC, and...
-
How does the WH approach to ethics respond to an ethical problem?
-
What is the expectations gap?
-
Guillen, Inc. began work on a $7,000,000 contract in 2010 to construct an office building. Guillen uses the completed-contract method. At December 31, 2010, the balances in certain accounts were...
-
A combined solar and auxiliary energy system is used to meet the same load as in Example 12.5. The total cost of the system to cover 65% of the load (solar fraction) is $20,000. The owner will pay a...
-
The following code fragments show a sequence of virus instructions and a metamorphic version of the virus. Describe the effect produced by the metamorphic code. Original Code mov eax, 5 add eax, ebx...
-
There is a flaw in the virus program of Figure 21.1.What is it? program V := {goto main; 1234567; subroutine infect-executable := {loop: file := get-random-executable-file; } if (first-line-of-file =...
-
Why do economists promote the idea of creating markets for environmental protection?
-
Which was more effective in getting us out of the Great Recession of 2007-8, monetary or fiscal policy? Use the case on the American Recovery and Reinvestment Act, as well as your research on the...
-
Write the feature of Super's Career Development Assessment and Counseling (C-DAC) system?
-
Describe one type of role-play technique you could use in a specific group setting. Explain who would benefit from this technique and why. Toseland, R. W., & Rivas, R. F. (2017). An introduction to...
-
A couple is sitting in the middle of an auditorium before the play starts. Even though everyone in the auditorium is talking, they can only hear each other's conversation. What is this an example of?
-
Frank had been a part of the Business Projects area for three years. A young man in his early twenties, he had started with HEDB in the hope of kick starting his career in the finance industry. While...
-
The following comparative information is available for Public Company for 2010. Instructions (a) Determine net income under each approach. Assume a 30% tax rate. (b) Determine net cash provided by...
-
State whether each of the following will increase or decrease the power of a one-way between-subjects ANOVA. (a) The effect size increases. (b) Mean square error decreases. (c) Mean square between...
-
On a typical Intel 8086-based system, connected via system bus to DRAM memory, for a read operation, is activated by the trailing edge of the Address Enable signal (Figure 3.19). However, due to...
-
The memory of a particular microcomputer is built from 64K 1 DRAMs. According to the data sheet, the cell array of the DRAM is organized into 256 rows. Each row must be refreshed at least once every...
-
Figure 5.17 shows one of the early SRAMs, the 16 Ã 4 Signetics 7489 chip, which stores 16 4-bit words. a. List the mode of operation of the chip for each input pulse shown in Figure 5.17c. b....
-
Thornton Boat Company makes inexpensive aluminum fishing boats. Production is seasonal, with considerable activity occurring in the spring and summer. Sales and production tend to decline in the fall...
-
Dollar-Value LIFO On January 1, 2018, Sato Company adopted the dollar-value LIFO method of inventory costing. Sato's ending inventory records appear as follows: Year Current Cost Index 2018 $39,700...
-
Betty's BBQ reported sales of $705,000 and net income of $25,000. Betty's also reported ending total assets of $494,000 and beginning total assets of $387,000. Required: Calculate the return on...

Study smarter with the SolutionInn App


