Draw a matrix similar to Table 1.4 that shows the relationship between security mechanisms and attacks. Table
Question:
Draw a matrix similar to Table 1.4 that shows the relationship between security mechanisms and attacks.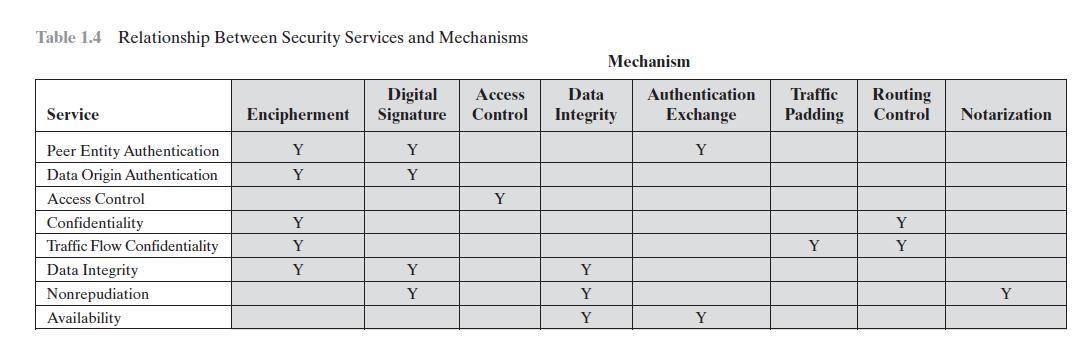
Transcribed Image Text:
Table 1.4 Relationship Between Security Services and Mechanisms Service Peer Entity Authentication Data Origin Authentication Access Control Confidentiality Traffic Flow Confidentiality Data Integrity Nonrepudiation Availability Digital Encipherment Signature Y Y Y Y Y Y Y Y Y Access Data Control Integrity Y Mechanism Y Y Y Authentication Traffic Routing Exchange Padding Control Notarization Y Y Y Y Y
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (2 reviews)
Encipherment Digital signature Access control Data integ...View the full answer

Answered By

HARSH RANJAN
Taken classes at college to graduates, Also worked as an expert to a freelancer online question-solving portal for more than 8 months with an average rating greater than 4.2 out of 5.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Draw a matrix similar to Table 1.4 that shows the relationship between security services and attacks. Table 1.4 Relationship Between Security Services and Mechanisms Service Peer Entity...
-
Use the following data to work Problems. Draw a graph that shows the relationship between the two variables x and y: a. Is the relationship positive or negative? b. Does the slope of the relationship...
-
The following table shows the relationship between the price of custard pies and the number of pies Jacob buys per week: a. Is the relationship between the price of pies and the number of pies Jacob...
-
Francis and Peter are in a partnership sharing profits and losses in the ratio 3:2. The following is their trial balance as at 30 September 2020. particulars D ebit C redit Buildings (cost: RM...
-
Consider the gas mixture fed to the combustors in the integrated gasification combined cycle power plant, as described in Problem 14.12. If the adiabatic flame temperature should be limited to 1500...
-
Horace Culpepper, CPA, was retained by Pulsar Cable to prepare financial statements for April 2020. Horace accumulated all the ledger balances per Pulsars records and found the following. Horace...
-
Identify the four components of an ecosystem. After you do this try to visualize the interactions of these four components of an ecosystem as illustrated by Figure 2. 2 in the textbook. Does this...
-
Presented below is information related to Taylor Co. for the month of January 2014. Instructions (a) Prepare the necessary adjusting entry for inventory. (b) Prepare the necessary closingentries....
-
3) Lets revisit the 2-D shallow water equations, but this time assume no rotation (f= 0) but the wave is embedded in a mean zonal flow U: V= (U+u'(x, 1)) + v'(x, 1); (1) where variables in bold are...
-
What are the essential ingredients of a symmetric cipher?
-
Repeat Problem 1.1 for a telephone switching system that routes calls through a switching network based on the telephone number requested by the caller. Problem 1.1 Consider an automated teller...
-
A discrete-time system has a unit impulse response h[n]. (a) Let the input to the discrete-time system be a pulse x[n] = u[n] u[n 4] compute the output of the system in terms of the impulse...
-
British historian of late 19th century, (Acton, 1887) said that "power tends to corrupt; absolute power corrupts absolutely," suggesting that a person's sense of morality lessens as his or her power...
-
If speculators expect a rising exchange to reverse itself we say that expectation is inelastic and speculation stabilizing. In the reverse case we have elastic exceptions and destabilizing...
-
Write four paragraphs describing effective persuasive communication in personal, professional, and academic contexts. No matter the context, you need to choose the most appropriate audience, method...
-
Discuss the differences between "I" and "me." Explain whether they are always different?
-
Explain: Agriculture's requirements from industry and government Elimination of urban bias Institutional reform land reform extension of infrastructure Appropriate technology Appropriate trade...
-
The following information pertains to Gilmore Company. 1. Cash balance per bank, July 31, $7,328. 2. July bank service charge not recorded by the depositor $40. 3. Cash balance per books, July 31,...
-
On average there are four traffic accidents in a city during one hour of rush-hour traffic. Use the Poisson distribution to calculate the probability that in one such hour there arc (a) No accidents...
-
Explain the difference between datagram and virtual circuit operation.
-
What are some of the limitations of using a circuit-switching network for data transmission?
-
What is a value-added network (VAN)?
-
What is Clinical Psychology? Answers I specifically have are: What does this specialty work on specifically? How do the different types of psychologies relate to the study Clinical Psychologists do?...
-
There are many early players in the field of psychology. Names that have become synonymous with psychology and even popular culture. These men and women have created ideas and concepts that respected...
-
if you decided to pursue a career in Psychology, which one of these research areas would you choose? explain why you would choose Humanistic Psychology?

Study smarter with the SolutionInn App


