Question: Figure 6.12b shows an alternative to CTS for producing ciphertext of equal length to the plaintext when the plaintext is not an integer multiple of
Figure 6.12b shows an alternative to CTS for producing ciphertext of equal length to the plaintext when the plaintext is not an integer multiple of the block size.
a. Explain the algorithm.
b. Explain why CTS is preferable to this approach illustrated in Figure 6.12b.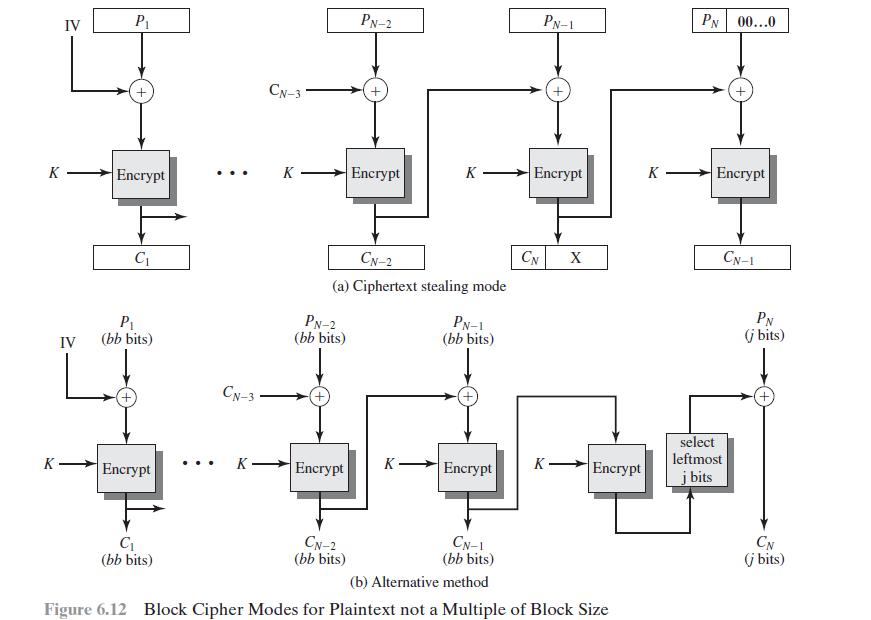
K K IV P Encrypt C P IV (bb bits) Encrypt C (bb bits) ... CN-3 K CN-3 K PN-2 (bb bits) Encrypt PN-2 CN-2 (a) Ciphertext stealing mode CN-2 (bb bits) Encrypt K PN-1 (bb bits) K- Encrypt CN-1 (bb bits) PN-1 Encrypt CN K- X Encrypt (b) Alternative method Figure 6.12 Block Cipher Modes for Plaintext not a Multiple of Block Size K PN 00...0 Encrypt CN-1 select leftmost j bits PN (j bits) + CN (j bits)
Step by Step Solution
3.46 Rating (159 Votes )
There are 3 Steps involved in it
a Assume that the last block leftmathrmPmathrmNight h... View full answer

Get step-by-step solutions from verified subject matter experts


