For each of the cybercrimes cited in Table 23.1, indicate whether it falls into the category of
Question:
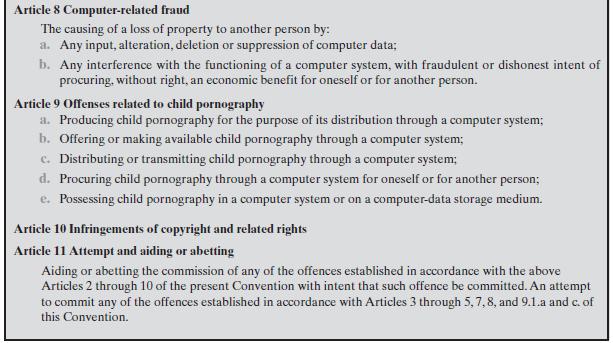
For each of the cybercrimes cited in Table 23.1, indicate whether it falls into the category of computer as target, computer as storage device, or computer as communications tool. In the first case, indicate whether the crime is primarily an attack on data integrity, system integrity, data confidentiality, privacy, or availability.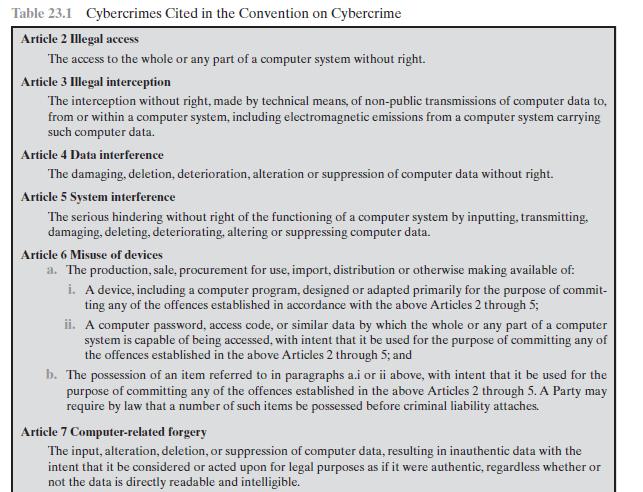
Transcribed Image Text:
Table 23.1 Cybercrimes Cited in the Convention on Cybercrime Article 2 Illegal access The access to the whole or any part of a computer system without right. Article 3 Illegal interception The interception without right, made by technical means, of non-public transmissions of computer data to, from or within a computer system, including electromagnetic emissions from a computer system carrying such computer data. Article 4 Data interference The damaging, deletion, deterioration, alteration or suppression of computer data without right. Article 5 System interference The serious hindering without right of the functioning of a computer system by inputting, transmitting, damaging, deleting, deteriorating, altering or suppressing computer data. Article 6 Misuse of devices a. The production, sale, procurement for use, import, distribution or otherwise making available of: i. A device, including a computer program, designed or adapted primarily for the purpose of commit- ting any of the offences established in accordance with the above Articles 2 through 5; ii. A computer password, access code, or similar data by which the whole or any part of a computer system is capable of being accessed, with intent that it be used for the purpose of committing any of the offences established in the above Articles 2 through 5; and b. The possession of an item referred to in paragraphs a.i or ii above, with intent that it be used for the purpose of committing any of the offences established in the above Articles 2 through 5. A Party may require by law that a number of such items be possessed before criminal liability attaches. Article 7 Computer-related forgery The input, alteration, deletion, or suppression of computer data, resulting in inauthentic data with the intent that it be considered or acted upon for legal purposes as if it were authentic, regardless whether or not the data is directly readable and intelligible.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (3 reviews)
Article 2 Illegal access This is a general threat the could fall into any of the t...View the full answer

Answered By

Felix Onchweri
I have enough knowledge to handle different assignments and projects in the computing world. Besides, I can handle essays in different fields such as business and history. I can also handle both short and long research issues as per the requirements of the client. I believe in early delivery of orders so that the client has enough time to go through the work before submitting it. Am indeed the best option that any client that can think about.
4.50+
5+ Reviews
19+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
1. How strong are the competitive forces confronting J. Crew in the market for specialty retail? Do a [Michael Porter] five-forces analysis to support your answer. (see chapter 3 in the textfor...
-
During one week, four production employees of Martinez Manufacturing Company worked the hours shown below. All these employees receive overtime pay at one and one-half times their regular hourly rate...
-
Liquid propane is burned with dry air. A volumetric analysis of the products of combustion yields the following volume percent composition on a dry basis: 8.6% CO2, 0.6% CO, 7.2% O2 and 83.6% N2....
-
Environmental sustainability is not only a potential competitive advantage to an organization, but might also be a regulatory requirement. The creation of business processes to support environmental...
-
Refer to the information in Problem 21-1B. Tohono Companys actual income statement for 2017 follows. Required 1. Prepare a flexible budget performance report for 2017. Analysis Component 2. Analyze...
-
Anglers Dream Company supplies flies and fishing gear to sporting goods stores and outfitters throughout the western United States. The accounts receivable clerk for Anglers Dream prepared the...
-
5. What effect do each of the following have on the regular payment and the total interest paid on a mortgage? Change Effect on Regular Payments (up/down) Effect on Total Interest Paid (up/down)...
-
Repeat Problem 23.1 for Table 23.2. Table 23.2 CERT 2006 E-Crime Watch Survey Results Theft of intellectual property Theft of other (proprietary) info including customer records, financial records,...
-
What functions can a professional code of conduct serve to fulfill?
-
Fill in each blank so that the resulting statement is true. |x - 7| < 2 can be rewritten without absolute value bars as_____ .
-
What role do critical theories, such as critical race theory, feminist theory, and queer theory, play in deconstructing dominant discourses, challenging power structures, and advocating for social...
-
Ask if your family has a diamond. Can you piece together its biogra- phy, its social life? Was it a purchase or a gift? What stories are asso- ciated with it, and what does it mean to its owner? Do...
-
How do micro-level theories, including rational choice theory, social exchange theory, and dramaturgical theory, elucidate individual decision-making, social interactions, and the construction of...
-
How do classical and contemporary social theorists conceptualize the intricate interplay between agency and structure in shaping human behavior and societal dynamics ?
-
We will delve into the profound significance of sustainability issues that are impacting the world of business and development. As we embark on our journey through the realm of green finance, it's...
-
What principles of internal control apply to most business enterprises?
-
Draw the appropriate control flow graph of the given pseudocode.Make sure to only use one number for blocks of code which are all sequential and when the first line is executed, all of those lines...
-
An example of a host-based intrusion detection tool is the tripwire program. This is a file integrity checking tool that scans files and directories on the system on a regular basis and notifies the...
-
Test the vulnerability of a machine at the following site: grc.com/default.htm. Follow the ShieldsUP! link for a series of free tests listed midway down the page.
-
The tiny fragment attack is a form of firewall attack. The intruder uses the IP fragmentation option to create extremely small fragments and force the TCP header information into a separate packet...
-
The risk-free rate of return is 4% and the expected return on the market is 9.2%. Stock A has a beta coefficient of 1.5 and dividend growth rate 5% Current dividend is $2.10 a share. What would be...
-
How does Positive Psychology differ from Clinical Psychology? Please add references.
-
Write a paragraph about the role of color psychology in marketing and business.Write a paragraph about the role of color psychology in marketing and business.

Study smarter with the SolutionInn App


