What are the differences among the firewalls of Figure 22.1? program V := {goto main; 1234567; subroutine
Question:
What are the differences among the firewalls of Figure 22.1?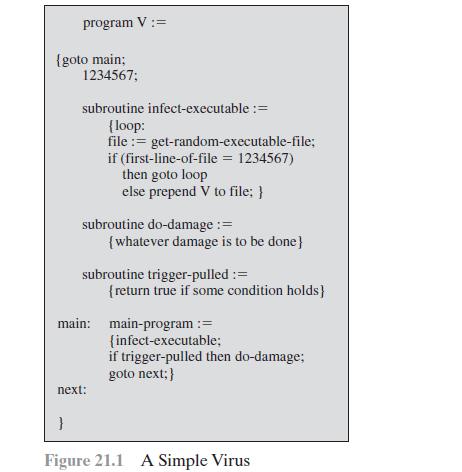
Transcribed Image Text:
program V := {goto main; 1234567; subroutine infect-executable := {loop: file := get-random-executable-file; if (first-line-of-file = 1234567) then goto loop else prepend V to file; } } subroutine do-damage := {whatever damage is to be done} subroutine trigger-pulled := next: main: main-program := {infect-executable; if trigger-pulled then do-damage; goto next; } {return true if some condition holds] Figure 21.1 A Simple Virus
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (1 review)
Packet filtering firewall Applies a set of rules to each incoming and outgoing IP packet and then forwards or discards the packet Stateful inspection ...View the full answer

Answered By

Susan Juma
I'm available and reachable 24/7. I have high experience in helping students with their assignments, proposals, and dissertations. Most importantly, I'm a professional accountant and I can handle all kinds of accounting and finance problems.
4.40+
15+ Reviews
45+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
What are the differences among debentures, serial bonds, and callable bonds?
-
What are the differences among loading fees, exit fees, and 12b-1 fees?
-
Multiple Choice 1. Which of the following concepts are pervasive in the application of generally accepted auditing standards, particularly the standards of field work and reporting? a. Internal...
-
A piston/cylinder contains 10 lbm of butane gas at 900 R, 750 lbf/in 2. The butane expands in a reversible polytropic process with polytropic exponent, n 1.05, until the final...
-
Tiny and Tim each own half of the 100 outstanding shares of Flower Corporation. This year, Flower reported taxable income of $10,000. In addition, Flower received $20,000 of life insurance proceeds...
-
Redesign the VOCs adsorber of Example 9.15 for a breakthrough time of \(4.0 \mathrm{~h}\). The pressure drop through the bed [calculated using the Ergun equation (2-95)] should not exceed \(1.0...
-
The chart of accounts of Lopez Company includes the following selected accounts. 112 Accounts Receivable 401 Sales 120 Merchandise Inventory 412 Sales Returns and Allowances 126 Supplies 505 Cost of...
-
Fickle Sickles collects 15,000 checks per 365-day year with average amount $170 and total delay 5 days. A lockbox system would reduce that delay to 3 days, and it would also reduce FISI's check...
-
What are the common characteristics of a bastion host?
-
What is a circuit-level gateway?
-
Can dividend be paid out of profit arising out of forfeited and re-issue of shares?
-
How do social movements and grassroots activism contribute to the mobilization of collective agency and the realization of progressive social change, particularly in the face of entrenched power...
-
To what extent do macro-level factors, such as globalization, climate change, and demographic shifts, drive systemic transformations and redefine the contours of social change on a global scale ?
-
What are some of the areas of public life that psychology is contributing to in the present day? What are some of the areas that psychology might or should be contributing to?
-
How have views on evolutionary psychology changed over the history of psychology? How has the idea of the individual differences changed?
-
Can roles be viewed as dynamic and context-dependent constructs, evolving over time and across different social contexts, or are they primarily static and predetermined by social structures ?
-
Reeble Company Inc. had a beginning inventory of 200 units of Product MLN at a cost of $8 per unit. During the year, purchases were: Feb. 20 700 units at $ 9 May 5 500 units at $10 Aug. 12 400 units...
-
Sundial Technologies produces and sells customized network systems in New Brunswick. The company offers a 60-day, all software and labor-and an extra 90-day, parts-only- warranty on all of its...
-
a. Consider an L1 cache with an access time of 1 ns and a hit ratio of H = 0.95. Suppose that we can change the cache design (size of cache, cache organization) such that we increase H to 0.97, but...
-
Consider a single-level cache with an access time of 2.5 ns, a line size of 64 bytes, and a hit ratio of H = 0.95. Main memory uses a block transfer capability that has a first-word (4 bytes) access...
-
A computer has a cache, main memory, and a disk used for virtual memory. If a referenced word is in the cache, 20 ns are required to access it. If it is in main memory but not in the cache, 60 ns are...
-
11. Consider a stock index currently standing at 250. The dividend yield, q, on the index is 4% per annum and the risk-free rate, r, is 6% per annum. A 3-month European Call option on the index with...
-
How do resistance movements, anti-globalization protests, and grassroots initiatives challenge dominant narratives of globalization and advocate for alternative visions of global justice, solidarity,...
-
Suppose Peloton company's stock has a beta of 0.26 and a required rate of return for the stock is 8%. If the average market return is 11%, what is the risk free rate of return? (Round your answer to...

Study smarter with the SolutionInn App


