According to Figure 8.6, a course can be taught by how many instructors?
Question:
According to Figure 8.6, a course can be taught by how many instructors?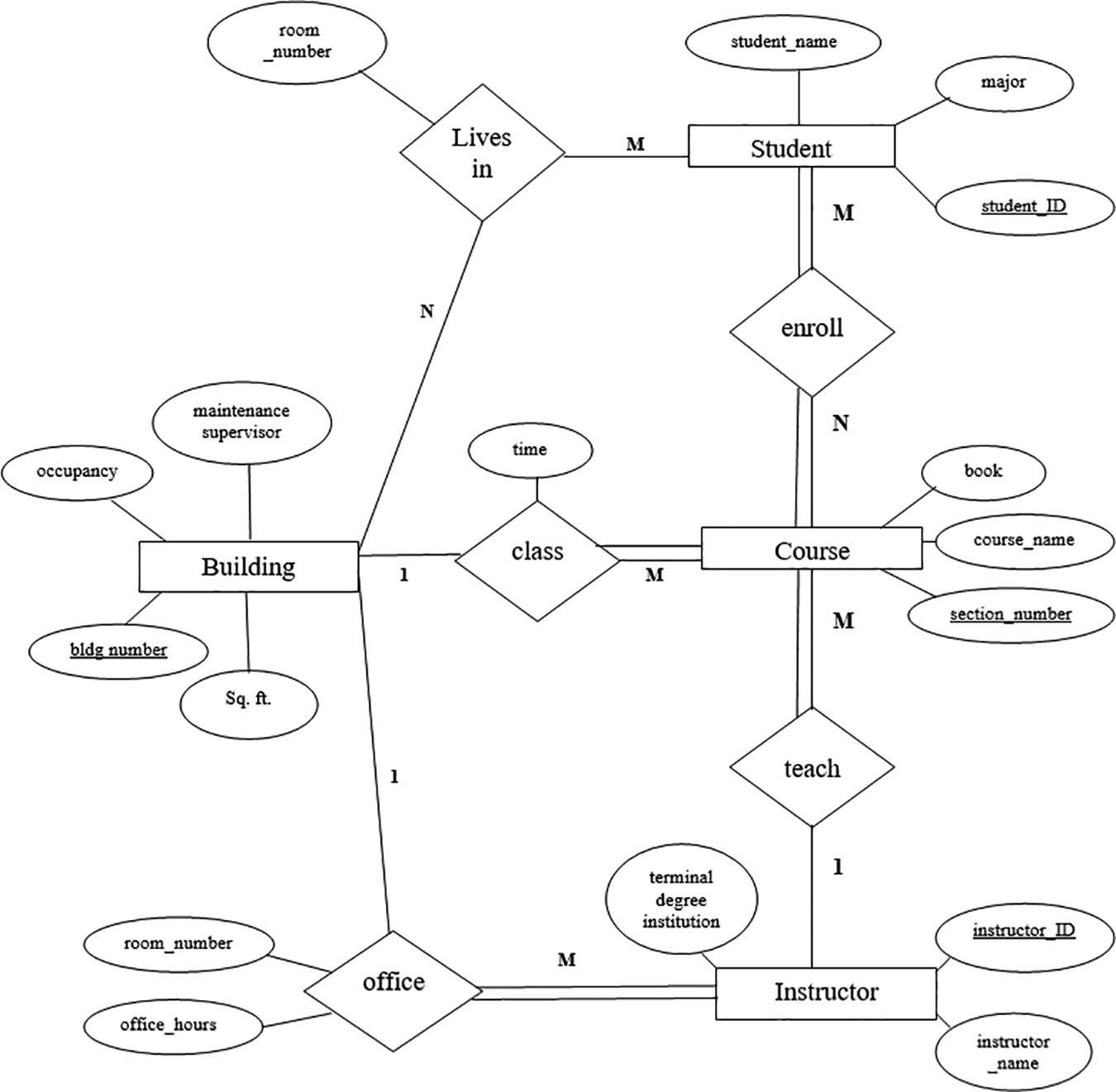
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)
In light of the data displayed in the image a class can be t...View the full answer

Answered By

Muhammad Umair
I have done job as Embedded System Engineer for just four months but after it i have decided to open my own lab and to work on projects that i can launch my own product in market. I work on different softwares like Proteus, Mikroc to program Embedded Systems. My basic work is on Embedded Systems. I have skills in Autocad, Proteus, C++, C programming and i love to share these skills to other to enhance my knowledge too.
3.50+
1+ Reviews
10+ Question Solved
Related Book For 

Database Design Using Entity Relationship Diagrams
ISBN: 9781032017181
3rd Edition
Authors: Sikha Saha Bagui, Richard Walsh Earp
Question Posted:
Students also viewed these Computer science questions
-
Business Process, Inc. (BPI), a consulting company offering business process reengineering and application system development expertise, wants to develop a prototype of a simple University...
-
Consider the following relation and convert to the normal form indicated. If the relation set is in its highest form simply state 2NF is also 3NF or similar under the appropriate normal form. 0NF:...
-
Is the answer correct? The graph of a y = f(x) is shown. 6 + 5 14 m ~ 1 -6 -5 -4 -3 2 -1 -1 -2 -3 A w -4 -5- -6+ 1 2 3 4 The domain of f(x) is x = [-3,3] The domain of g(x) = notation) S 6 f(x) is a ...
-
Orient each of the following drawings so that the lowest-priority group is toward the rear, and then assign R or Sconfiguration: (b) (a) (c) 2 2
-
A battery has an emf of 15.0 V. The terminal voltage of the battery is 11.6 V when it is delivering 20.0 W of power to an external load resistor R. (a) What is the value of R? (b) What is the...
-
The filament-wound E-glass/epoxy pressure vessel described in Example 4.4 is to be used in a hot-wet environment with temperature \(T=100^{\circ} \mathrm{F}\) \(\left(38^{\circ} \mathrm{C} ight)\)...
-
What microenvironmental factors have affected Targets performance over the past few years? When you hear the term discount retail, two names that usually come to mind: Walmart and Target. The two...
-
A zookeeper finds an escaped monkey hanging from a light pole. Aiming her tranquilizer gun at the monkey, she kneels 10.0 m above the ground. At the same moment that the monkey drops a banana, the...
-
What is a recursive relationship?
-
According to Figure 8.6, does a course have to be taught by an instructor?
-
In a gasliquid interface mass-transfer process, the bulk mole fraction composition of solute A in the inert carrier gas is 0.010, and the bulk mole fraction composition of solute A in the inert...
-
How did New York Times v. Sullivan change the face of defamation?
-
True Or False Those who distribute or sell defamatory materials are liable even if they can show they had no reason to believe the materials were defamatory.
-
____________ statutes may bar a plaintiffs recovery if the defendant withdraws a defamatory statement within a given time period.
-
True Or False In cases of slander, pecuniary losses are not necessary.
-
True Or False A defamation plaintiff who suffers no quantifiable damages cannot go to trial.
-
EKU, Inc., issued $560,000 of 6%, 10-year bonds payable at a price of 80.5 on March 31, 2012. The market interest rate at the date of issuance was 9%, and the EKU bonds pay interest semiannually. 1....
-
Element compound homogeneous mixture (heterogeneous mixture) 4) A piece of gold has a mass of 49.75 g. What should the volume be if it is pure gold? Gold has a density of 19.3 g/cm (3 points) D=m/v...
-
The java.util.Collection interface includes a method, contains(o), that returns true if the collection contains any object that equals Object o. Implement such a method in the ArrayList class of...
-
Describe a fast recursive algorithm for reversing a singly linked list L, so that the ordering of the nodes becomes opposite of what it was before.
-
Communication security is extremely important in computer networks, and one way many network protocols achieve security is to encrypt messages. Typical cryptographic schemes for the secure...
-
b) Who were the "Big Six"? 3. Why did March 7, 1965 come to be known as "Bloody Sunday"? 4. On August 28, 1963, speaking from the steps of the Lincoln Memorial, what did John Lewis say was the reason...
-
Which type of groups can make up a 'care network' for consumers?
-
Create an FML meeting agenda with the following FML Process Proposal This FML Process Change Presentation is a comprehensive solution for proposing efficient changes that improve how our employees...

Study smarter with the SolutionInn App