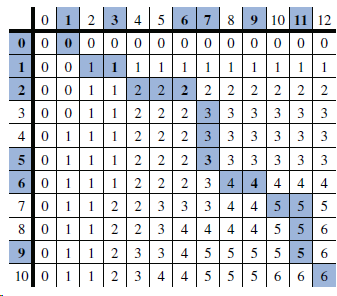
In Figure 13.14, we illustrate that GTTTAA is a longest common subsequence for the given strings X
Question:
Transcribed Image Text:
0 12 3 4 5678 0000000000 0 000 10011 1 1111 1111 00112 2 2 2 2 2 3001|122 9 10 11 12 2 2 2 2 3 3 3 3 33 4 0111 2 2 2 3 3 3 01112 2 2 3 3 3 0 1112|2 2 3 4 70112 2 3 3 3 4 4 0112 2 3 444 0|1123 345 10 0112 3 4 333 3 3 3 3 3 4 4 5 55 4 4 4 4 5 |5 6 5 5 5 5 6 455 5 6. 6. 6.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 75% (8 reviews)
Two additi...View the full answer

Answered By

Nikita Naik
I graduated with Latin Honor (Cum Laude) having a degree of B.S. Civil Engineering in 2017 and passed the professional board examination for Civil Engineer in the same year. Now, I am currently working as a Planning and Design Engineer II at the Department of Public Works and Highways, Tarlac, Philippines with 5+ years of working experience. I am a member of our CE Honor Society where in we teach college students in Mathematics when I was still studying. I have an experience for being a Math expert from various platforms such as coursehero and freelancercareers.org.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Question Posted:
Students also viewed these Computer science questions
-
The longest common subsequence problem is as follows: Given two sequences A = a1, a2, . . . , aM, and B = b1, b2, . . . , bN, find the length, k, of the longest sequence C = c1, c2, . . . , ck such...
-
During the course of an algorithm, we sometimes find that we need to maintain past versions of a dynamic set as it is updated. Such a set is called persistent. One way to implement a persistent set...
-
Illustrate how multipath routing can be done between nodes 1 and 26 of Problem P13.7. Which multipath routing technique is beneficial and why? Explan clearly. A snapshot of an ad hoc network is shown...
-
Has Mississippi enacted the Uniform Real Property Electronic Recording Act? Provide the URL/web address of your source. Provide the citation to where this law is found in the Miss. Code (including...
-
Monitor Muffler sells franchise arrangements throughout the United States and Canada. Under a franchise agreement, Monitor receives $600,000 in exchange for satisfying the following separate...
-
A fully differential op amp with CMFB is shown in Fig. 12.57. For M 1 , M 1C , M 2 , and M 2C , use W/L = (64 µm) / (0.8 µm). For M 3 M 4 , M 26 M 27 and M 11 , W / L = (96 µm) /...
-
Assume that in a digital communication channel, the number of bits received in error can be modeled by a binomial random variable, and assume that the probability that a bit is received in error is...
-
Dynamo Corporation manufactures toasters. Each toaster comes with a five-year warranty. The toasters sell for $50 each and during Year 1 Dynamo sells 500 toasters. Past experience shows that the...
-
What strategies does Lean Management employ to empower employees through skill development, cross-functional training, and collaborative problem-solving initiatives? Explain
-
XYZ is an unlevered firm and is currently valued at $820,000. It has 15,000 shares outstanding. As part of a Management Buyout (MBO), XYX is planning to borrow $400,000 from a bank at an annual...
-
Describe an example of a text T of length n and a pattern P of length m such that the brute-force pattern-matching algorithm achieves a running time that is (nm).
-
What is the longest (proper) prefix of the string "cgtacgttcgtacg" that is also a suffix of this string?
-
Graph f(x) = -0.25x 4 +0.67x 3 + 9.5x 2 - 20x - 50. (a) Approximate any local extrema. (b) Approximate any absolute extrema. (c) Determine where f is increasing or decreasing.
-
Suppose two people want to play poker over the network. To deal the cards, they need a mechanism for fairly choosing a random number x between them; each party stands to lose if the other party can...
-
What are the peculiarities of CBA approach adopted by the EIB?
-
Which method would use to value a private hospital room relative to a shared room?
-
In TCP Vegas, the calculation of ActualRate is done by dividing the amount of data transmitted in one RTT interval by the length of the RTT. (a) Show that for any TCP, if the window size remains...
-
Suppose, in the other direction, we abandon any pretense at all of DNS hierarchy and simply move all the .com entries to the root name server: www.cisco.com would become www.cisco, or perhaps just...
-
An economist believed that as nations become wealthier, they produce more greenhouse gases. He took a country and found both its gross domestic product (GDP) and the total tons of CO 2 emissions for...
-
The packaging division of a company having considered several alternative package designs for the company's new product has finally brought down their choices to two designs of which only one has to...
-
Prove that 2 i=1 + N
-
A language L is complete for a language class C with respect to polynomial-time reductions if L C and L P L for all L C. Show that ; and {0, 1} * are the only languages in P that are not complete...
-
A hamiltonian path in a graph is a simple path that visits every vertex exactly once. Show that the language HAM-PATH = {G, u, : there is a Hamiltonian path from u to in graph G} belongs to NP.
-
How can bash shell scripting improve resource utilization and process management in Unix systems?
-
A solid sphere that is uniformly positively charged produces an electric field. Assume no other objects are around. What is the magnitude of the electric field a distance r from the center of the...
-
Why is potential difference important in x - ray production?

Study smarter with the SolutionInn App