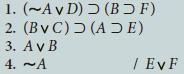
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments:
Question:
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments:
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (7 reviews)
To derive the conclusion EvF line 5 from the given premises using the first eight rules of inferenc...View the full answer

Answered By

GERALD KAMAU
non-plagiarism work, timely work and A++ work
4.40+
6+ Reviews
11+ Question Solved
Related Book For 

A Concise Introduction to Logic
ISBN: 978-1305958098
13th edition
Authors: Patrick J. Hurley, Lori Watson
Question Posted:
Students also viewed these Social Science questions
-
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments: 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. 17. 18. 19. 20. 21. 22. 23. 24. 25. 26....
-
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments:
-
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments:
-
A firm has initial fund of $800. The market rate of return is 12%. The firm has identified good investment opportunities to invest $640 at an average 25 per cent rate of return. How much dividend...
-
Nokia, Research In Motion, Apple, and Palm are competitors in the global marketplace. Selected data for Nokia follow. Required 1. Review the discussion of the importance of the cost of goods sold...
-
What is the preemptive right, and what are the two primary reasons for its existence? AppendixLO1
-
6. What is the purpose of a capital projects fund? Are all general fixed assets of a governmental unit acquired through capital projects funds? Explain.
-
The following pension-related data pertain to Metro Recreation's noncontributory, defined benefit pension plan for 2011: Required: Prepare a pension spreadsheet that shows the relationships among the...
-
Using the double declining balance (DDB) method: (38) The depreciation amount in the second year is close to: :) $1800 b) $1250 c) $1300 d) $1370 Questions (36-41): The purchase price of a machine is...
-
A company conducts a consumer survey with questions about home ownership (OwnHome: Yes/No), car ownership (OwnCar: Yes/No), annual household spending on food (Food), and annual household spending on...
-
Assume you are part of a development team that is working on a new warehouse management system. You have the task of investigating software packages that are available through ASPs. Using the World...
-
Use the first eight rules of inference to derive the conclusions of the following symbolized arguments:
-
The receipts and year of release of five successful movies, along with the CPI data of each year are presented below. Assuming that the receipts for each of the movies were derived during their year...
-
Select a qualitative research design to establish whether the strike by the federal workers in Canada may have been caused by a leadership
-
There is a single loop circuit with three resistors as follows. Take R-D 2, R= D/2 2 and R= D/3 2 and connect to 12 V battery. a. What can you say about the connection of R., R2 and Rs, Explain the...
-
1:This week we learned about Team Communication and Difficult conversation. Reflect on your own experience of a difficult conversation that you had to handle. Explain what happened and how you...
-
What is the value chain of Doordash? Name their primary and support activities.
-
Blue Water Clinic is a mobile field medical facility that has been offering Covid-19 vaccination services to rural communities in southwest Ontario under the supervision of medical authorities. With...
-
The comparative balance sheet of Navaria Inc. for December 31, 20Y3 and 20Y2, is as follows: The income statement for the year ended December 31, 20Y3, is as follows: Additional data obtained from an...
-
You are the newly appointed tax practitioner to complete Emilys tax return and have downloaded the prefill report for Emilys tax return (hint, you can read what a prefill report is here (Links to an...
-
The data from exercise 1 follow. a. Compute the mean square error using equation (14.15). b. Compute the standard error of the estimate using equation (14.16). c. Compute the estimated standard...
-
The data from exercise 1 follow. a. Compute the mean square error using equation (14.15). b. Compute the standard error of the estimate using equation (14.16). c. Compute the estimated standard...
-
In exercise 18 the data on price ($) and the overall score for six stereo headphones tested by Consumer Reports were as follows (Consumer Reports website, March 5, 2012). Brand _______________ Price...
-
Physical Units Method, Relative Sales Value Method Farleigh Petroleum, Inc., is a small company that acquires high - grade crude oil from low - volume production wells owned by individuals and small...
-
A proposed $2.5 M investment in new equipment at a 100 MG/y M&Ms factory will save the plant $800,000/y in energy costs. Assuming an annual interest rate of 5%/y (compounded annually), and an...
-
Brief Exercise 10-7 Coronado Company obtained land by issuing 2,250 shares of its $14 par value common stock. The land was recently appraised at $103,240. The common stock is actively traded at $44...

Study smarter with the SolutionInn App


