Question: Which statement best describes the following method? A. It is not susceptible to any common attacks. B. It is at risk of SQL injection attack
Which statement best describes the following method?
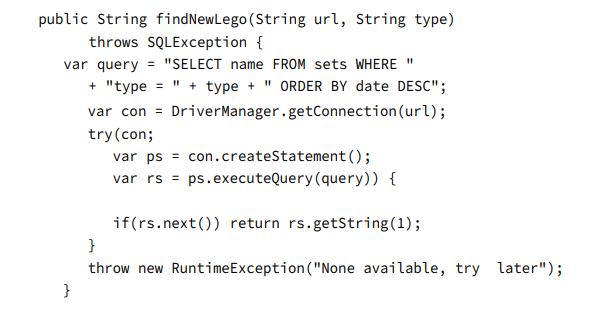
A. It is not susceptible to any common attacks.
B. It is at risk of SQL injection attack only.
C. It is at risk of a denial of service attack only.
D. It is at risk of both SQL injection and denial of service attacks.
E. The method does not compile.
F. None of the above.
public String findNewLego (String url, String type) throws SQLException { var query = "SELECT name FROM sets WHERE " } + "type = " + type +" ORDER BY date DESC"; var con = DriverManager.getConnection (url); try (con; var ps con.createStatement (); var rs = ps.executeQuery (query)) { if(rs.next()) return rs.getString(1); } throw new RuntimeException ("None available, try later");
Step by Step Solution
3.48 Rating (155 Votes )
There are 3 Steps involved in it
Based on the provided code snippet the correct answer would be B It is at risk of SQL injection atta... View full answer

Get step-by-step solutions from verified subject matter experts


