1. (10 points) Consider sending a large file of size 8MB from source to destination. Assume...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
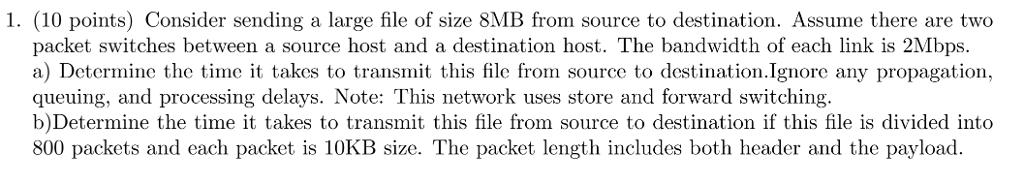
1. (10 points) Consider sending a large file of size 8MB from source to destination. Assume there are two packet switches between a source host and a destination host. The bandwidth of each link is 2Mbps. a) Determine the time it takes to transmit this file from source to destination.Ignore any propagation, queuing, and processing delays. Note: This network uses store and forward switching. b)Determine the time it takes to transmit this file from source to destination if this file is divided into 800 packets and each packet is 10KB size. The packet length includes both header and the payload. 1. (10 points) Consider sending a large file of size 8MB from source to destination. Assume there are two packet switches between a source host and a destination host. The bandwidth of each link is 2Mbps. a) Determine the time it takes to transmit this file from source to destination.Ignore any propagation, queuing, and processing delays. Note: This network uses store and forward switching. b)Determine the time it takes to transmit this file from source to destination if this file is divided into 800 packets and each packet is 10KB size. The packet length includes both header and the payload.
Expert Answer:
Answer rating: 100% (QA)
SOLUTION a To calculate the time it takes to transmit the file we need to calculate the number of pa... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Problem 1. (16 points) Information about Internet protocol stack. a. What are the five layers in the Internet protocol stack? b. What is the packet called in each of layer of Internet protocol stack?...
-
Consider sending a large file of F bits from Host A to Host B. There are three links (and two switches) between A and B, and the links are uncongested (that is, no queuing delays). Host A segments...
-
How can we measure a security's contribution to the risk of the market portfolio?
-
(a) As a source of long-term financing, what are the major advantages of bonds over ordinary shares? (b) What are the major disadvantages in using bonds for long-term financing?
-
Scientists have used Mongolian gerbils when con- ducting neurological research. A certain breed of these gerbils were crossed and gave progeny of the following colors32: (a) What is the value of the...
-
Petitioner Christy Brzonkala met respondents Antonio Morrison and James Crawford at a campus party at Virginia Polytechnic Institute (Virginia Tech), where they were all students. At the party, the...
-
Melissa's Photo Studio offers both individual and group portrait options. The process flow diagram in Figure shows that all customers must first register and then pay at one of two cashiers. Then...
-
Please share a quote from Dr. Thom Garfat's piece where he signals, implicitly or explicitly, how this relational model frames youths. Identify something the relational CYC/"inter-personal...
-
If you declare a variable in C++ and use it before initializing it what the compiler will generate?
-
Sketch curves for throughput, delay, and power, each as a function of load, for the following networks. Throughput is to be measured as a percentage of the maximum. Load is to be measured (somewhat...
-
Using the data in the file named Toysrusformat.xlsx, highlight in red all quarters for which revenue has increased over at least the last two quarters. Highlight all fourth quarter revenues in blue...
-
Amis, Lodge and Pym were in partnership sharing profits and losses in the ratio 5 : 3 : 2. The following trial balance has been extracted from their books of account as at 31 March 20X8: Additional...
-
Write the electron dot formula and draw the structural formula for stibine, SbH 3 , whose central atom is a semimetal.
-
Using a single test described in 4.8.1, we can test for faults in several different signals, but typically not all of them. Describe a series of tests to look for this fault in all Mux outputs (every...
-
Due to an unequal distribution of fuel in the wing tanks, the centers of gravity for the airplane fuselage A and wings B and C are located as shown. Draw a free-body diagram of the airplane. If these...
-
Burberrys competitive advantage is through its differentiation strategy. What risk should Burberry remain aware of?
-
Suppose Alice wants to send an e-mail to Bob. Bob has a public-private key pair (K+B,K-B)' and Alice has Bob's certificate. But Alice does not have a public, private key pair. Alice and Bob (and the...
-
Section 7.3 describes two FEC schemes. Briefly summarize them. Both schemes increase the transmission rate of the stream by adding overhead. Does interleaving also increase the transmission rate?
-
What are some typical compression ratios (ratio of the number of bits in an uncompressed object to the number of bits in the compressed version of that object) for image and audio applications, and...
-
A probability experiment consists of rolling a single fair die. (a) Identify the outcomes of the probability experiment. (b) Determine the sample space. (c) Define the event E = roll an even number....
-
A pair of fair dice is rolled. Fair die are die where each outcome is equally likely. (a) Compute the probability of rolling a seven. (b) Compute the probability of rolling snake eyes; that is,...
-
Our number system consists of the digits 0, 1, 2, 3, 4, 5, 6, 7, 8, and 9. Because we do not write numbers such as 12 as 012, the first significant digit in any number must be 1, 2, 3, 4, 5, 6, 7, 8,...

Study smarter with the SolutionInn App


