1. [3 marks] Suppose you are responsible for the IT infrastructure of an organization, which has...
Fantastic news! We've Found the answer you've been seeking!
Question:
![1. [3 marks] Suppose you are responsible for the IT infrastructure of an organization, which has about 20](https://dsd5zvtm8ll6.cloudfront.net/questions/2023/10/6540c21ae7395_1698742805758.jpg)
Transcribed Image Text:
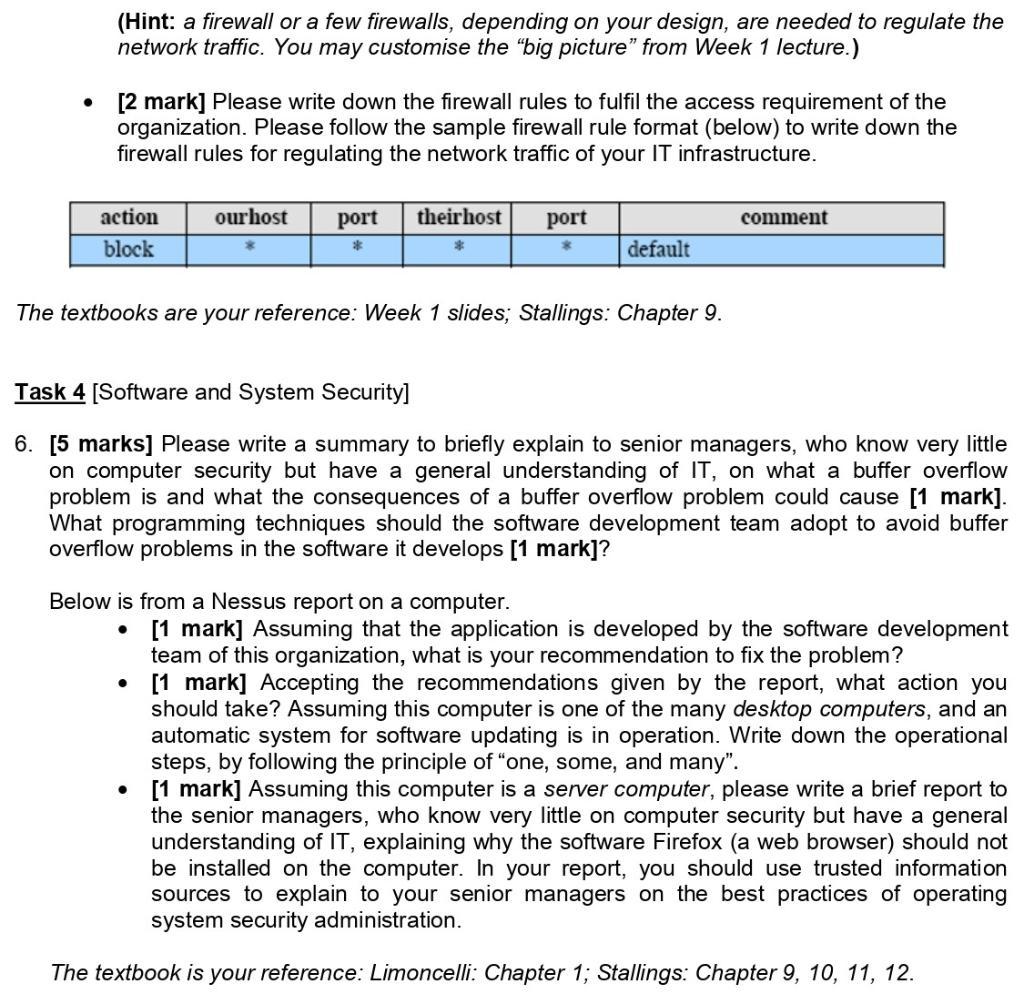
1. [3 marks] Suppose you are responsible for the IT infrastructure of an organization, which has about 20 desktop computers. You are advised that automation for uniformity is a good solution. What does "automation for uniformity" mean? Why is it a good solution in principle? Will you implement a fully automatic system in this case of yours? 2. [2 marks] Please summarise the technologies used in server computers to improve reliability. availability, and performance. 3. [2 mark] Please summarise the essentials of running a well organised Helpdesk operation. Task 2 [Cryptography] 4. [3 marks] Suppose that you are responsible for the IT department of a university with students around the world. It is infeasible to meet each student in person. The IT department is responsible for all secure communication with the students. Assume that there is a trusted certificate authority which can securely issue certificates to all involved parties. Please explain: • Why the trusted certificate authority is essential to establish a secure communication? What role does it play in the secure communication between the IT department and the students? From time to time, your department, on behalf of the University, makes public announcements. The announcements are of public nature and can be shared and transmitted by any interested parties, say, prospective students. How would you guarantee the authenticity of your announcements? It is not a solution to publish the announcement on a website for students to compare and decide if the received copies are the same as the web copies. Task 3 [DoS and Firewall] 5. [5 marks] An organization has two server computers and several desktop computers, a few printers (IP address: p1.p2.p3.p4) and routers (IP address: r1.r2.r3.r4). All of them are connected via an internal network, and the network is connected to the Internet via the border router of the organization. From the outside of the organization, on the Internet, only these two server computers are visible. One of them is the email server (IP address: e1.e2.e3.e4), and the other one is the web server (IP address: w1.w2.w3.w4). In other words, only these two server computers accept requesting incoming network traffic. All desktop computers (IP address: d1.d2.d3.d4) are allowed to access the Internet, without any restriction. Therefore, they accept responding incoming network traffic, but cannot accept any requesting incoming network traffic. . [3 marks] Please design the network and draw the network diagram. You have the freedom to assume the internal network structure. In the diagram, in addition to the two servers, you should also include a few desktop computers and a printer. Please explain the rationale on why you put a computer or a printer in its designated location, one example for each location. A subnet (or a segment) is regarded as the same location. (Hint: a firewall or a few firewalls, depending on your design, are needed to regulate the network traffic. You may customise the "big picture" from Week 1 lecture.) [2 mark] Please write down the firewall rules to fulfil the access requirement of the organization. Please follow the sample firewall rule format (below) to write down the firewall rules for regulating the network traffic of your IT infrastructure. action block ourhost port * theirhost port * ● The textbooks are your reference: Week 1 slides; Stallings: Chapter 9. Below is from a Nessus report on a computer. ● * default Task 4 [Software and System Security] 6. [5 marks] Please write a summary to briefly explain to senior managers, who know very little on computer security but have a general understanding of IT, on what a buffer overflow problem is and what the consequences of a buffer overflow problem could cause [1 mark]. What programming techniques should the software development team adopt to avoid buffer overflow problems in the software it develops [1 mark]? comment [1 mark] Assuming that the application is developed by the software development team of this organization, what is your recommendation to fix the problem? [1 mark] Accepting the recommendations given by the report, what action you should take? Assuming this computer is one of the many desktop computers, and an automatic system for software updating is in operation. Write down the operational steps, by following the principle of "one, some, and many". • [1 mark] Assuming this computer is a server computer, please write a brief report to the senior managers, who know very little on computer security but have a general understanding of IT, explaining why the software Firefox (a web browser) should not be installed on the computer. In your report, you should use trusted information sources to explain to your senior managers on the best practices of operating system security administration. The textbook is your reference: Limoncelli: Chapter 1; Stallings: Chapter 9, 10, 11, 12. 1. [3 marks] Suppose you are responsible for the IT infrastructure of an organization, which has about 20 desktop computers. You are advised that automation for uniformity is a good solution. What does "automation for uniformity" mean? Why is it a good solution in principle? Will you implement a fully automatic system in this case of yours? 2. [2 marks] Please summarise the technologies used in server computers to improve reliability. availability, and performance. 3. [2 mark] Please summarise the essentials of running a well organised Helpdesk operation. Task 2 [Cryptography] 4. [3 marks] Suppose that you are responsible for the IT department of a university with students around the world. It is infeasible to meet each student in person. The IT department is responsible for all secure communication with the students. Assume that there is a trusted certificate authority which can securely issue certificates to all involved parties. Please explain: • Why the trusted certificate authority is essential to establish a secure communication? What role does it play in the secure communication between the IT department and the students? From time to time, your department, on behalf of the University, makes public announcements. The announcements are of public nature and can be shared and transmitted by any interested parties, say, prospective students. How would you guarantee the authenticity of your announcements? It is not a solution to publish the announcement on a website for students to compare and decide if the received copies are the same as the web copies. Task 3 [DoS and Firewall] 5. [5 marks] An organization has two server computers and several desktop computers, a few printers (IP address: p1.p2.p3.p4) and routers (IP address: r1.r2.r3.r4). All of them are connected via an internal network, and the network is connected to the Internet via the border router of the organization. From the outside of the organization, on the Internet, only these two server computers are visible. One of them is the email server (IP address: e1.e2.e3.e4), and the other one is the web server (IP address: w1.w2.w3.w4). In other words, only these two server computers accept requesting incoming network traffic. All desktop computers (IP address: d1.d2.d3.d4) are allowed to access the Internet, without any restriction. Therefore, they accept responding incoming network traffic, but cannot accept any requesting incoming network traffic. . [3 marks] Please design the network and draw the network diagram. You have the freedom to assume the internal network structure. In the diagram, in addition to the two servers, you should also include a few desktop computers and a printer. Please explain the rationale on why you put a computer or a printer in its designated location, one example for each location. A subnet (or a segment) is regarded as the same location. (Hint: a firewall or a few firewalls, depending on your design, are needed to regulate the network traffic. You may customise the "big picture" from Week 1 lecture.) [2 mark] Please write down the firewall rules to fulfil the access requirement of the organization. Please follow the sample firewall rule format (below) to write down the firewall rules for regulating the network traffic of your IT infrastructure. action block ourhost port * theirhost port * ● The textbooks are your reference: Week 1 slides; Stallings: Chapter 9. Below is from a Nessus report on a computer. ● * default Task 4 [Software and System Security] 6. [5 marks] Please write a summary to briefly explain to senior managers, who know very little on computer security but have a general understanding of IT, on what a buffer overflow problem is and what the consequences of a buffer overflow problem could cause [1 mark]. What programming techniques should the software development team adopt to avoid buffer overflow problems in the software it develops [1 mark]? comment [1 mark] Assuming that the application is developed by the software development team of this organization, what is your recommendation to fix the problem? [1 mark] Accepting the recommendations given by the report, what action you should take? Assuming this computer is one of the many desktop computers, and an automatic system for software updating is in operation. Write down the operational steps, by following the principle of "one, some, and many". • [1 mark] Assuming this computer is a server computer, please write a brief report to the senior managers, who know very little on computer security but have a general understanding of IT, explaining why the software Firefox (a web browser) should not be installed on the computer. In your report, you should use trusted information sources to explain to your senior managers on the best practices of operating system security administration. The textbook is your reference: Limoncelli: Chapter 1; Stallings: Chapter 9, 10, 11, 12.
Expert Answer:
Answer rating: 100% (QA)
Answer to question 1 Automation for uniformity means using automation to ensure that all IT infrastructure components are configured and managed in the same way This can be achieved by using scripts c... View the full answer

Related Book For 

Smith and Roberson Business Law
ISBN: 978-0538473637
15th Edition
Authors: Richard A. Mann, Barry S. Roberts
Posted Date:
Students also viewed these computer network questions
-
The probability distribution is given below for the random variable X = "number of days between the placement of an order and receiving an order". Probability Days 2 0.15 3 0.45 4 0.30 5 0.10 Find...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Identify 3 ethical and 3 legal issues regarding Genomics ? with examples? Genomic services provided for gaining a better understanding of the interactions between genes and the environment but there...
-
Use this North Pole overhead view of the three sites of the Deep Space Network to answer following Exercises. 1. If the three sites of the Deep Space Network (red dots shown) are about the same...
-
A lease agreement calls for quarterly lease payments of $5,376 over a 10-year lease term, with the first payment at July 1, the leases inception. The interest rate is 8%. Both the fair value and the...
-
Prove that, for the system considered in Section 13.5.1, the minimum value of \(\omega^{2}\) for which the amplitude of subharmonic oscillations \(A\) will have a real value is given by...
-
Charter Corp. has issued 2,500 debentures with a total principal value of $2,500,000. The bonds have a coupon interest rate of 7%. a. What dollar amount of interest per bond can an investor expect to...
-
In Module Five we looked at instances of persons who disseminated/leaked/published classified information for what they considered to be righteous reasons. A recent Washington Post article that we...
-
The entity reports the following transactions for the 2022 tax year. The trustee accumulates all accounting income for the year. Operating income from a business $500,000 30,000 Dividend income, all...
-
Why should the board and board quality committee regularly review quality dashboard reports showing metrics that are considered to be indicators of quality outcomes, safety, experience, and value?
-
Financial planners (and engineering economists) unanimously encourage people to seek out the highest rate of return possible within their personal level of risk tolerance. To illustrate this point,...
-
Show that the two terms in the Ising model Hamiltonian (23.9) do not commute and thus represent competing, incompatible tendencies in the corresponding system. Data from Eq. 23.9 H=-(80+001),
-
An investment has the following cash flow profile. MARR is 12 percent/year. What is the minimum value of \(X\) such that the investment is attractive based on a future worth measure of merit? End of...
-
This problem and Problem 23.2 give a qualitative feeling for the difference between a phase dominated by classical thermal effects and one dominated by quantum effects by considering the...
-
Based on the strategy, what type of sampling technique will be used to identify the sample? a. Why did you choose this type of technique?
-
The BL over a plate is described by u/u1-sin(pai*y/2*sigma). Show that the momentum thickness is 0.1378.
-
Determine which of the following limits exist. Compute the limits that exist. lim x-0 1- + 3x X
-
Carl, a salesman for Smith, comes to Bensons home and sells him a complete set of gourmet cooking utensils that are worth approximately $300. Benson, an eighty-year-old man living alone in a one-room...
-
Civil Code 1719, subdivision (a) provides in part that any person who draws a check that is dishonored due to insufficient funds shall be liable to the payee for the amount owing upon the check and...
-
Discuss the contractual liability of the principal, agent, and third party when the principal is (a) disclosed, (b) partially disclosed, and (c) undisclosed.
-
Assume that \(y\) is normally distributed with mean \(\mu\) and variance \(\sigma^{2}\). Let \(\phi(\cdot)\) and \(\Phi(\cdot)\) be the standard normal density and distribution functions,...
-
Use equation (17.2) to establish the following distributional relationships that are helpful for calculating quantiles. a. Assume that \(y_{0}=\alpha_{1} F / \alpha_{2}\), where \(F\) has an...
-
Consider a GB2 probability density function given in equation (17.3). a. Reparameterize the distribution by defining the new parameter \(\theta=e^{\mu}\). Show that the density can be expressed as...

Study smarter with the SolutionInn App