(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
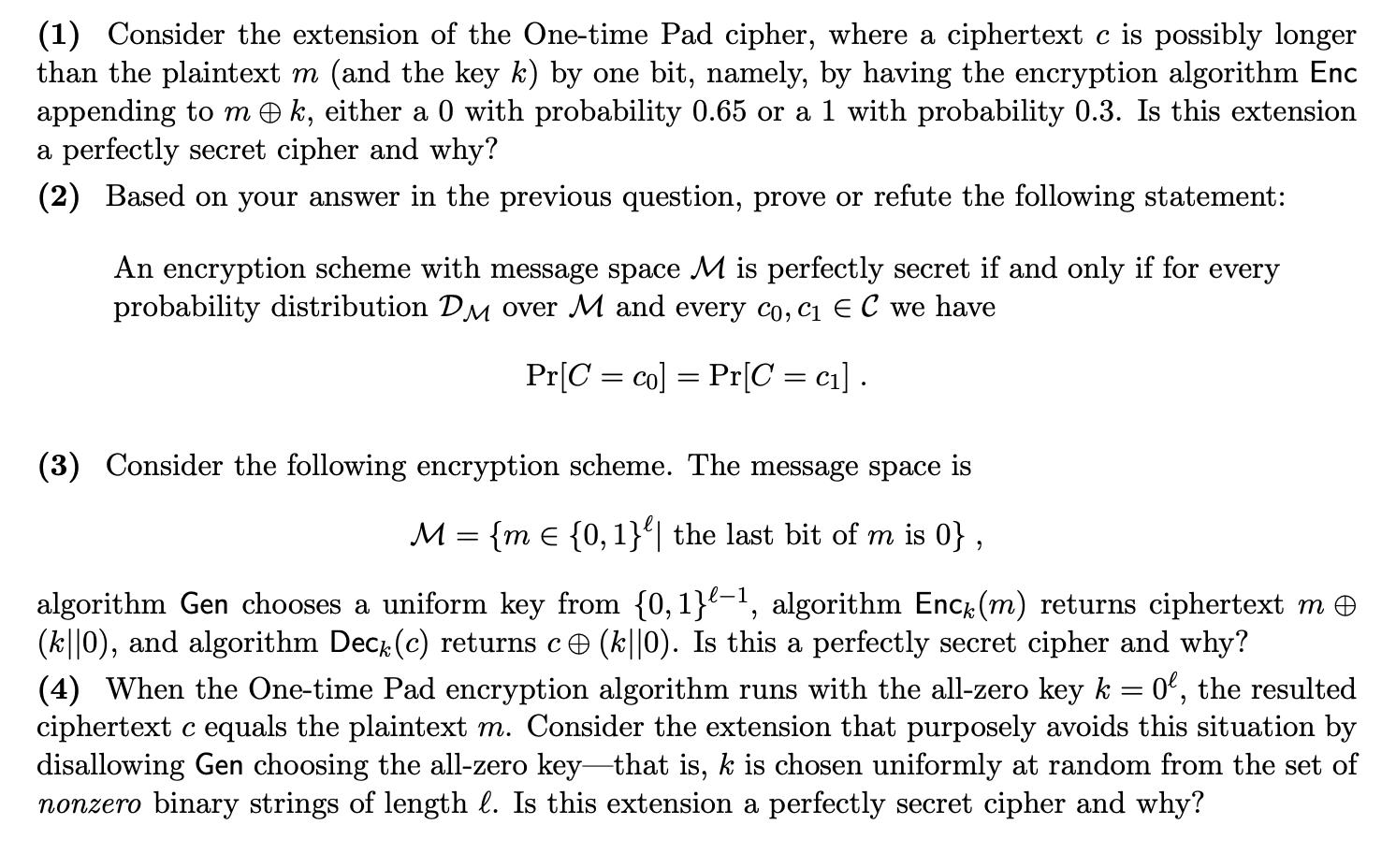
(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why? (1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why?
Expert Answer:
Answer rating: 100% (QA)
Extension of Onetime Pad This extension is not a perfectly secret cipher In a perfectly secret ciphe... View the full answer

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
In 1999, GLSEN identified that little was known about the school experiences of lesbian, gay, bisexual, transgender, and queer (LGBTQ+) youth and that LGBTQ+ youth were nearly absent from national...
-
The article notes that the hospital did not fully understand how its electronic health record system would estimate expected revenue. This was obviously happening at the hospital for some time. How...
-
Consider a repeated version of the game in exercise 24.5. In this version, we do not give all the proposal power to one person but rather imagine that the players are bargaining by making different...
-
Someone offered the investment options to Hendry on January 1, 2023: 1. Hendry has to save up to 5 times the initial deposit of US $ 150,000/year. 2. The savings cannot be taken for 20 years until...
-
Explain how a proper work surface height would be determined.
-
An ideal gas is expanded reversibly and isothermally. Decide which of q, w, U, and H is positive, negative, or zero.
-
The following information relates to the business of Restaurant Gigi, and the owner is concerned about the profitability and financial structure of his business at 30 June 2025, especially since the...
-
Table contains data for the installation of new equipment in a manufacturing process at Excello Corporation. Your company is responsible for the installation project. Indirect costs are $15,000 per...
-
1. Over the past thirty years, post-secondary tuition rates in Canada have increased dramatically. Had tuition grown at the rate of inflation, the average in 2019-20 would have been only $2,541. What...
-
corporation is resisting the personal holding company tax, but the Tax Court sides with the IRS. Within 90 days after the adverse decision, one shareholder transfers his stock and $10,000 in cash to...
-
A good project plan has to keep the project on time and within thebudget. Let's explore how to reduce project duration. There are risks and benefits to reducing project duration. The figure belowis a...
-
To be a successful member of an IMC campaign, guerrilla marketing must accomplish four specific things. What are they? Define and explain each.
-
Alternative media vehicles have more diverse options than any other advertising and promotional category. What does the advertised message need to relay visually and verbally to strategically express...
-
What is important when writing and designing for mobile?
-
How are quick response (QR) codes employed in mobile advertising?
-
Why is social media considered technologys answer to personal selling?
-
A 57g tennis ball is served at 45m/s . If the ball started from rest, what impulse was applied to theball by the racket? Express your answer using two significant figures.
-
How can a promoter avoid personal liability for pre-incorporation contracts?
-
In the ring topology in Figure 1.7, what happens if one of the stations is unplugged? Figure 1.7 Repeater Repeater Repeater |Repeater Repeater Repeater
-
Referring to the CRC-8 in Table 5.4, answer the following questions: a. Does it detect a single error? Defend your answer. b. Does it detect a burst error of size 6? Defend your answer. c. What is...
-
Write a statement in Java to create a socket address bound to the local host and the HTTP server process.
-
Examine Fowlers account pattern on following characteristics: a. Simplicity b. Generality c. Completeness d. Stability e. Visual and graphical model f. Testability
-
Draw a class diagram for resource rental pattern and its installation for library service by using analogy approach.
-
What is Fowlers account pattern? Explain with the help of a diagram.

Study smarter with the SolutionInn App


