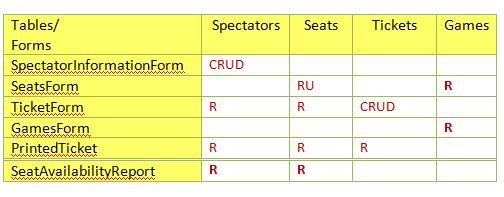
Question: 1. Given the following Security matrix, which is the most most complex form to implement? TicketForm SpectatorInformationForm PrintedTicket SeatsForm 2. Another name for a transaction
1.
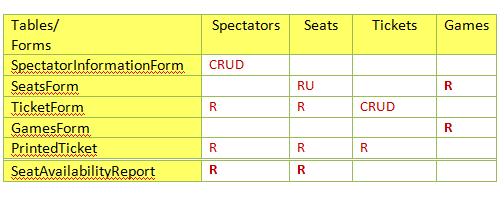
Given the following Security matrix, which is the most most complex form to implement?
| TicketForm | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| SpectatorInformationForm | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| PrintedTicket | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| SeatsForm
2. Another name for a transaction is:
|
Tables/ Forms SpectatorinformationForm CRUD Spectators Seats Tickets Games RU TicketForm GamesForm PrintedTicket SeatAvailabilityReport CRUD
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts