Question: 1. Let F be a secure PRP with blocklength 1. Consider the following encryption mode: Ene(k, m ||..Ime): see (K, Enclk, my...) C {1} for
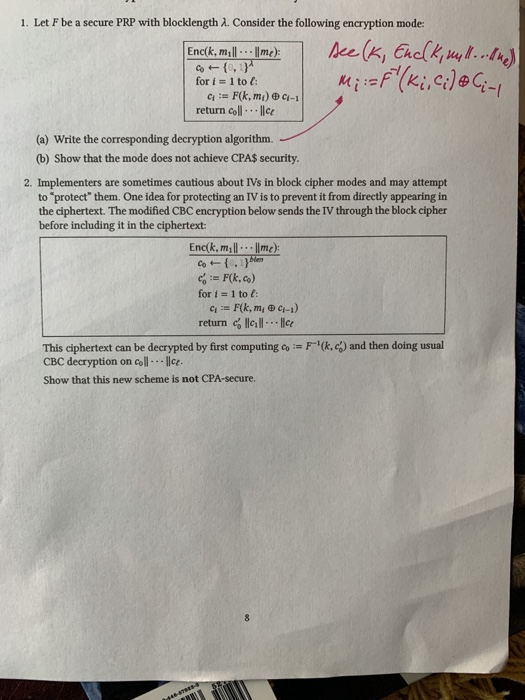
1. Let F be a secure PRP with blocklength 1. Consider the following encryption mode: Ene(k, m ||..Ime): see (K, Enclk, my...) C {1} for i = 1 to : G = F(k,mi) - return coll. ce M := F" (ki, Cile Ciny (a) Write the corresponding decryption algorithm. (b) Show that the mode does not achieve CPA$ security. 2. Implementers are sometimes cautious about IVs in block cipher modes and may attempt to protect them. One idea for protecting an IV is to prevent it from directly appearing in the ciphertext. The modified CBC encryption below sends the IV through the block cipher before including it in the ciphertext: Enck, mill... |me) C {Men = F(k.co) for 1 = 1 to : 4 = F(k, m, 6-1) return call... | ce This ciphertext can be decrypted by first computing := F"(c) and then doing usual CBC decryption on coll-llce. Show that this new scheme is not CPA-secure 1. Let F be a secure PRP with blocklength 1. Consider the following encryption mode: Ene(k, m ||..Ime): see (K, Enclk, my...) C {1} for i = 1 to : G = F(k,mi) - return coll. ce M := F" (ki, Cile Ciny (a) Write the corresponding decryption algorithm. (b) Show that the mode does not achieve CPA$ security. 2. Implementers are sometimes cautious about IVs in block cipher modes and may attempt to protect them. One idea for protecting an IV is to prevent it from directly appearing in the ciphertext. The modified CBC encryption below sends the IV through the block cipher before including it in the ciphertext: Enck, mill... |me) C {Men = F(k.co) for 1 = 1 to : 4 = F(k, m, 6-1) return call... | ce This ciphertext can be decrypted by first computing := F"(c) and then doing usual CBC decryption on coll-llce. Show that this new scheme is not CPA-secure
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


