2:24 PM Sun Feb 20 moodle.oakland.edu both of which can be downloaded from the SEED website....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
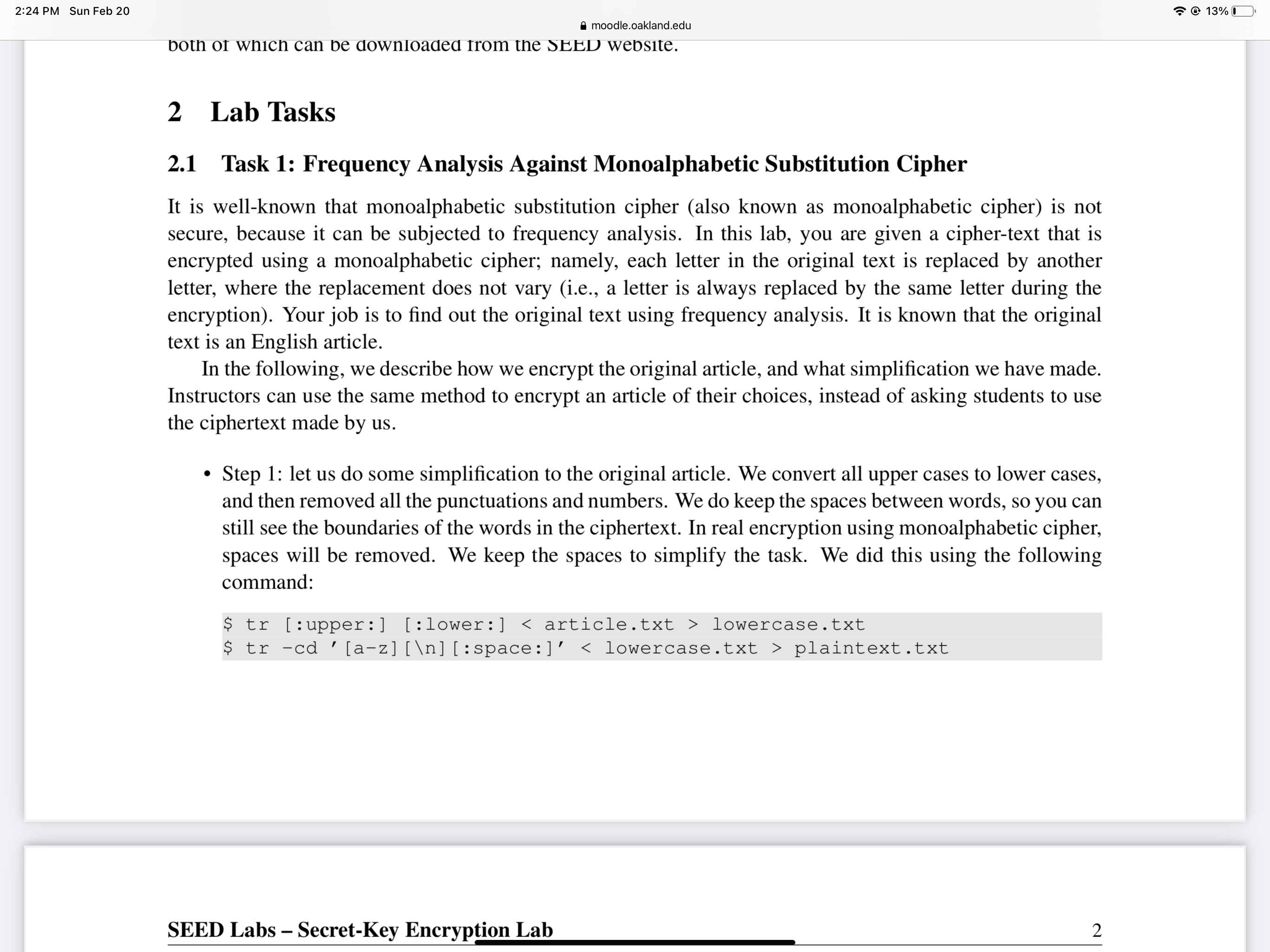
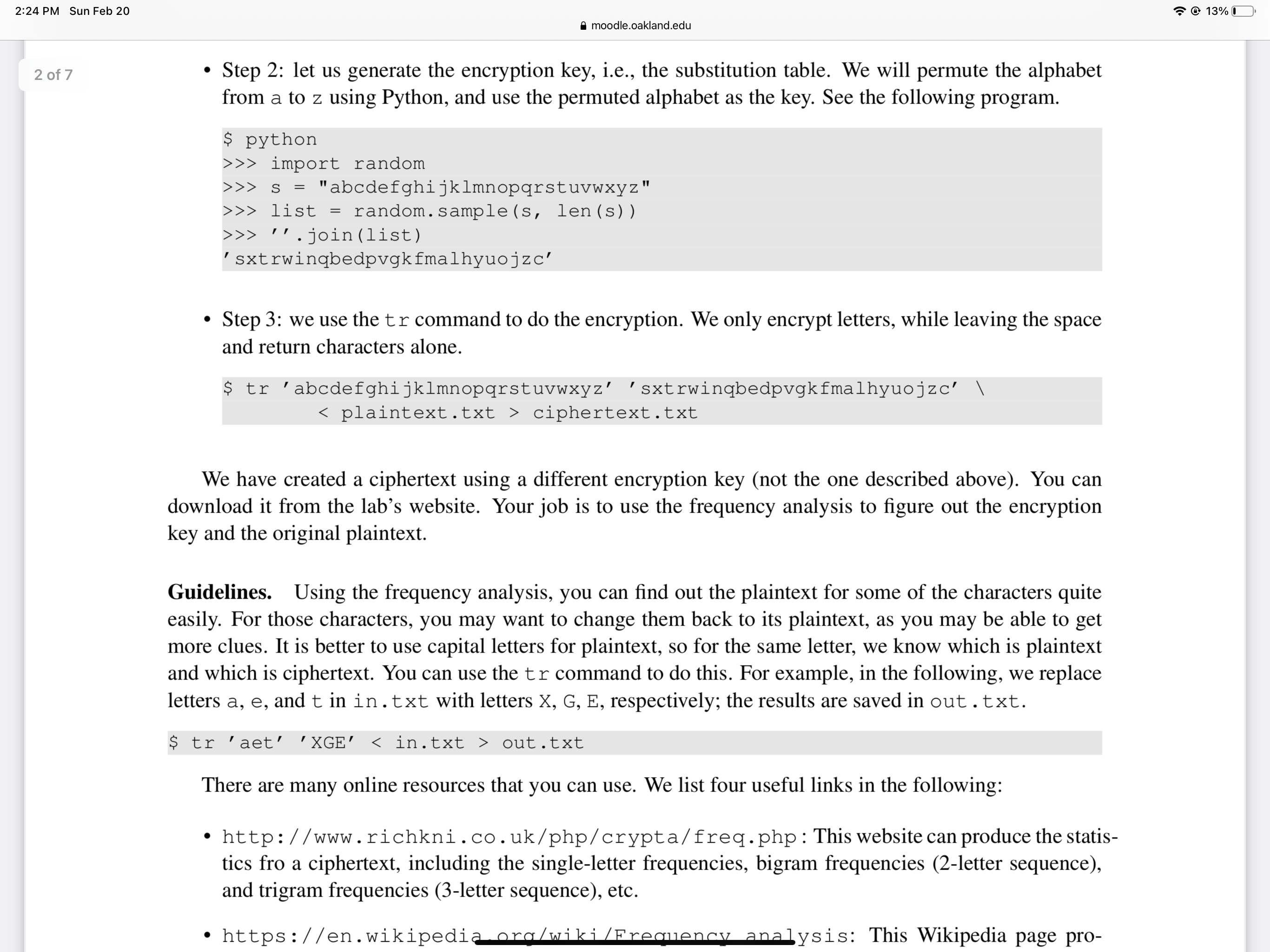
2:24 PM Sun Feb 20 moodle.oakland.edu both of which can be downloaded from the SEED website. 2 Lab Tasks 2.1 Task 1: Frequency Analysis Against Monoalphabetic Substitution Cipher It is well-known that monoalphabetic substitution cipher (also known as monoalphabetic cipher) is not secure, because it can be subjected to frequency analysis. In this lab, you are given a cipher-text that is encrypted using a monoalphabetic cipher; namely, each letter in the original text is replaced by another letter, where the replacement does not vary (i.e., a letter is always replaced by the same letter during the encryption). Your job is to find out the original text using frequency analysis. It is known that the original text is an English article. In the following, we describe how we encrypt the original article, and what simplification we have made. Instructors can use the same method to encrypt an article of their choices, instead of asking students to use the ciphertext made by us. Step 1: let us do some simplification to the original article. We convert all upper cases to lower cases, and then removed all the punctuations and numbers. We do keep the spaces between words, so you can still see the boundaries of the words in the ciphertext. In real encryption using monoalphabetic cipher, spaces will be removed. We keep the spaces to simplify the task. We did this using the following command: $ tr [:upper:] [:lower:] < article.txt > lowercase.txt $ tr-cd ' [a-z] [ ] [:space:]' < lowercase.txt > plaintext.txt SEED Labs - Secret-Key Encryption Lab 2 13% I 2:24 PM Sun Feb 20 2 of 7 moodle.oakland.edu Step 2: let us generate the encryption key, i.e., the substitution table. We will permute the alphabet from a to z using Python, and use the permuted alphabet as the key. See the following program. $ python >>> import random >>> s = "abcdefghijklmnopqrstuvwxyz" random.sample(s, len(s)) >>> list = >>> ''.join (list) 'sxtrwingbedpvgk fmalhyuojzc' Step 3: we use the tr command to do the encryption. We only encrypt letters, while leaving the space and return characters alone. $ tr 'abcdefghijklmnopqrstuvwxyz' sxtrwingbedpvgkfmalhyuojzc' \ < plaintext.txt > ciphertext.txt We have created a ciphertext using a different encryption key (not the one described above). You can download it from the lab's website. Your job is to use the frequency analysis to figure out the encryption key and the original plaintext. " Guidelines. Using the frequency analysis, you can find out the plaintext for some of the characters quite easily. For those characters, you may want to change them back to its plaintext, as you may be able to get more clues. It is better to use capital letters for plaintext, so for the same letter, we know which is plaintext and which is ciphertext. You can use the tr command to do this. For example, in the following, we replace letters a, e, and t in in.txt with letters X, G, E, respectively; the results are saved in out.txt. $ tr 'aet' 'XGE' < in.txt > out.txt There are many online resources that you can use. We list four useful links in the following: http://www.richkni.co.uk/php/crypta/freq.php: This website can produce the statis- tics fro a ciphertext, including the single-letter frequencies, bigram frequencies (2-letter sequence), and trigram frequencies (3-letter sequence), etc. https://en.wikipedia.org/wiki/Frequency analysis: This Wikipedia page pro- 13% I 2:24 PM Sun Feb 20 moodle.oakland.edu both of which can be downloaded from the SEED website. 2 Lab Tasks 2.1 Task 1: Frequency Analysis Against Monoalphabetic Substitution Cipher It is well-known that monoalphabetic substitution cipher (also known as monoalphabetic cipher) is not secure, because it can be subjected to frequency analysis. In this lab, you are given a cipher-text that is encrypted using a monoalphabetic cipher; namely, each letter in the original text is replaced by another letter, where the replacement does not vary (i.e., a letter is always replaced by the same letter during the encryption). Your job is to find out the original text using frequency analysis. It is known that the original text is an English article. In the following, we describe how we encrypt the original article, and what simplification we have made. Instructors can use the same method to encrypt an article of their choices, instead of asking students to use the ciphertext made by us. Step 1: let us do some simplification to the original article. We convert all upper cases to lower cases, and then removed all the punctuations and numbers. We do keep the spaces between words, so you can still see the boundaries of the words in the ciphertext. In real encryption using monoalphabetic cipher, spaces will be removed. We keep the spaces to simplify the task. We did this using the following command: $ tr [:upper:] [:lower:] < article.txt > lowercase.txt $ tr-cd ' [a-z] [ ] [:space:]' < lowercase.txt > plaintext.txt SEED Labs - Secret-Key Encryption Lab 2 13% I 2:24 PM Sun Feb 20 2 of 7 moodle.oakland.edu Step 2: let us generate the encryption key, i.e., the substitution table. We will permute the alphabet from a to z using Python, and use the permuted alphabet as the key. See the following program. $ python >>> import random >>> s = "abcdefghijklmnopqrstuvwxyz" random.sample(s, len(s)) >>> list = >>> ''.join (list) 'sxtrwingbedpvgk fmalhyuojzc' Step 3: we use the tr command to do the encryption. We only encrypt letters, while leaving the space and return characters alone. $ tr 'abcdefghijklmnopqrstuvwxyz' sxtrwingbedpvgkfmalhyuojzc' \ < plaintext.txt > ciphertext.txt We have created a ciphertext using a different encryption key (not the one described above). You can download it from the lab's website. Your job is to use the frequency analysis to figure out the encryption key and the original plaintext. " Guidelines. Using the frequency analysis, you can find out the plaintext for some of the characters quite easily. For those characters, you may want to change them back to its plaintext, as you may be able to get more clues. It is better to use capital letters for plaintext, so for the same letter, we know which is plaintext and which is ciphertext. You can use the tr command to do this. For example, in the following, we replace letters a, e, and t in in.txt with letters X, G, E, respectively; the results are saved in out.txt. $ tr 'aet' 'XGE' < in.txt > out.txt There are many online resources that you can use. We list four useful links in the following: http://www.richkni.co.uk/php/crypta/freq.php: This website can produce the statis- tics fro a ciphertext, including the single-letter frequencies, bigram frequencies (2-letter sequence), and trigram frequencies (3-letter sequence), etc. https://en.wikipedia.org/wiki/Frequency analysis: This Wikipedia page pro- 13% I
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these computer network questions
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
If a= <1,0,1>, b= <2,1,-1>, and c= <0,1,3>, show that aX(bXc) is not equal (aXb)Xc.
-
A company reports the following: Net income........................................$ 375,000 Preferred dividends.................................75,000 Average stockholders'...
-
xplain the relevance and difference of parent company approach and parent extension method revisited in preparing consolidated financial statement.
-
Attracted by the possible returns from a portfolio of movies, hedge funds have invested in the movie industry by financially backing individual films and/or studios. The hedge fund Star Ventures is...
-
Omar Marquez is the audio engineer for Summer Musical Enterprises. The group is considering the purchase of a new sound system consisting of five separate components. The components are arranged in...
-
Write a complete C++ program to check whether the string input is similar when it reads the same backwards as forwards using queue algorithms based on the instructions given. In the class ADTqueue,...
-
You have a portfolio which is comprised of 40% of Stock A and 60% of Stock B. What is the portfolio standard deviation? State of the Economy Probability E(RA) E(RB) 40% 60% Boom .10 20 % 14 % Normal...
-
Consider the least-squares residuals $e_{i}=y_{i}-\hat{y}_{i}, i=1,2, \ldots, n$, from the simple linear regression model. Find the variance of the residuals $\operatorname{Var}\left(e_{i} ight)$. Is...
-
Portsmouth Hospitals NHS Trust promotes equality with due regard to the protected characteristics of age, disability, gender reassignment, marriage and civil partnership, pregnancy and maternity,...
-
Consider the simple linear regression model \[y=\beta_{0}+\beta_{1} x+\varepsilon\] where the intercept $\beta_{0}$ is known. a. Find the least-squares estimator of $\beta_{1}$ for this model. Does...
-
In this zone, we critically evaluate the dark side of emotional intelligence and explore its impact on organisational behaviour in the workplace Over the past two decades, emotional intelligence (EI)...
-
Did you find it helpful to use this chart to identify micro-stressors that impact your day-to-day life? Why or why not?
-
Both consolidation and equity method accounting assume a dollar earned by a subsidiary is equivalent to a dollar earned for a parent, even if not received in cash. The limitations of this assumption...
-
1-Stern observed all of the following results EXCEPT _______ in his experiment. A-one of the recombinant phenotypes was associated with an X chromosome of normal length B-the number of car, B+ male...
-
Yolanda is a cash basis taxpayer with the following transactions during the year: Cash received from sales of products........................................................................$65,000...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-4. Ivan and Irene paid the following in 2012 (all by check or can otherwise be...
-
Diane is a single taxpayer who qualifies for the earned income credit. Diane has two qualifying children who are 3 and 5 years old. During 2012, Diane's wages are $17,100 and she receives dividend...
-
A hydraulic lift in a service station has a \(32.50-\mathrm{cm}\)-diameter ram that slides in a \(32.52-\mathrm{cm}\)-diameter cylinder. The annular space is filled with SAE 10 oil at \(20^{\circ}...
-
A 10-kg block slides down a smooth inclined surface as shown in Fig. P1.80. Determine the terminal velocity of the block if the \(0.1-\mathrm{mm}\) gap between the block and the surface contains SAE...
-
Oil (absolute viscosity \(=0.0003 \mathrm{lb} \cdot \mathrm{s} / \mathrm{ft}^{2}\), density \(=50\) \(\mathrm{lbm} / \mathrm{ft}^{3}\) ) flows in the boundary layer, as shown in Fig. P1.82. The plate...

Study smarter with the SolutionInn App


