Question: Suppose that the attacker can eavesdrop on an initial 2-message exchange, where a Kerberos client requests the ticket-granting ticket (TGT), and receives one from
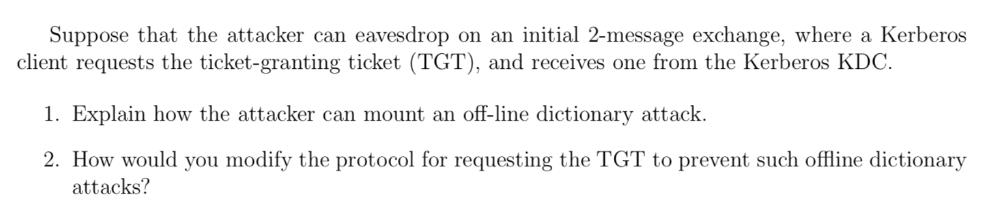
Suppose that the attacker can eavesdrop on an initial 2-message exchange, where a Kerberos client requests the ticket-granting ticket (TGT), and receives one from the Kerberos KDC. 1. Explain how the attacker can mount an off-line dictionary attack. 2. How would you modify the protocol for requesting the TGT to prevent such offline dictionary attacks?
Step by Step Solution
There are 3 Steps involved in it
1 Offline Dictionary Attack In a Kerberos authentication process the initial 2message exchange involves the client requesting a ticketgranting ticket ... View full answer

Get step-by-step solutions from verified subject matter experts


