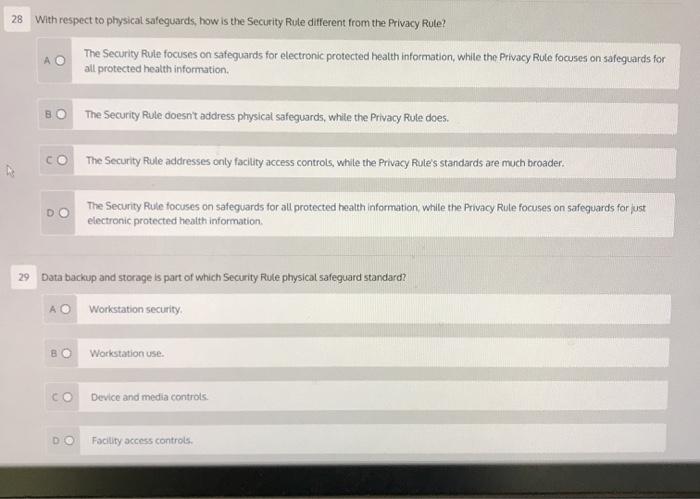
28 With respect to physical safeguards, how is the Security Rule different from the Privacy Rule?...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
28 With respect to physical safeguards, how is the Security Rule different from the Privacy Rule? 22 BO The Security Rule focuses on safeguards for electronic protected health information, while the Privacy Rule focuses on safeguards for all protected health information. В The Security Rule doesn't address physical safeguards, while the Privacy Rule does. The Security Rule addresses only facility access controls, while the Privacy Rule's standards are much broader. The Security Rule focuses on safeguards for all protected health information, while the Privacy Rule focuses on safeguards for just electronic protected health information. 29 Data backup and storage is part of which Security Rule physical safeguard standard? AO Workstation security. Workstation use. CO Device and media controls. Facility access controls. 28 With respect to physical safeguards, how is the Security Rule different from the Privacy Rule? 22 BO The Security Rule focuses on safeguards for electronic protected health information, while the Privacy Rule focuses on safeguards for all protected health information. В The Security Rule doesn't address physical safeguards, while the Privacy Rule does. The Security Rule addresses only facility access controls, while the Privacy Rule's standards are much broader. The Security Rule focuses on safeguards for all protected health information, while the Privacy Rule focuses on safeguards for just electronic protected health information. 29 Data backup and storage is part of which Security Rule physical safeguard standard? AO Workstation security. Workstation use. CO Device and media controls. Facility access controls.
Expert Answer:
Answer rating: 100% (QA)
28 The correct option is A Privacy rule focuses on t... View the full answer

Related Book For 

Statistics The Exploration & Analysis of Data
ISBN: 978-1133164135
7th edition
Authors: Roxy Peck, Jay L. Devore
Posted Date:
Students also viewed these operating system questions
-
How is the security of a firms information system and data affected by its people, organization, and technology? Is the contribution of one of these dimensions any more important than the other? Why?
-
How might using electronic media to report project information lead to problems with control?
-
How does physical access control differ from the logical access control described in earlier chapters? How is it similar?
-
Pricing in imperfect markets (continuation of 22-28). Refer to Problem 22-28. 1.Suppose the manager of Division A has the option of (a) cutting the external price to $195, with the certainty that...
-
Discuss whether the following expenditures meet the ordinary, necessary, and reasonable requirements: a. The Brisbane Corporation is being sued in connection with allegations that it produced a...
-
To improve the quality of the output of any production process, it is necessary first to understand the capabilities of the process (Gitlow, Quality Management, 2004). In a particular manufacturing...
-
Journalize the following adjusting entries at December 31: 1. Services provided but not recorded, $1,500. 2. Salaries earned by employees but not recorded, $2,300. 3. Accrued interest on a note...
-
Lena Kay and Kathy Lauder have a patent on a new line of cosmetics. They need additional capital to market the products, and they plan to incorporate the business. They are considering the capital...
-
1. In Canada, directors owe two legal duties under corporate legislation. Describe these two legal duties and to whom they are owed. 2. There are two different types of contracts which a director...
-
Mr. M has been employed as an engineer by A Ltd., a company incorporated in Hong Kong. During the year ended 31 March 2019, Mr. M had the following income and expenditure. A monthly salary of...
-
Write a paper about The 1993 attack on the World Trade Center
-
Given a Stream, which method would you use to obtain an equivalent parallel Stream? A. getParallelStream() B. parallelStream() C. parallel() D. getParallel() E. parallels() F. None of the above
-
The following diagrams represent the order of read/write operations of two threads sharing a common variable. Each thread first reads the value of the variable from memory and then writes a new value...
-
Fill in the blank with the functional interface from java.util.function that allows the code to compile and print 3 at runtime. _____________ transformer = x -> x; A. Function B. UnaryOperator C....
-
What is the expected result of calling deleteTree() on a directory? Assume the directory exists and is able to be modified. A. It will delete the directory itself only. B. It will delete the...
-
Fill in the blanks: ______________ is a special case of ______________, in which two or more active threads try to acquire the same set of locks and are repeatedly unsuccessful. A. Deadlock, livelock...
-
Provide positive feedback and insight. Respond in full and comprehensive sentences. No numbering, labeling, or bulletins. The company I am reporting on is Hewlett- Packard, also known as "HP". HP is...
-
Match the following. Answers may be used more than once: Measurement Method A. Amortized cost B. Equity method C. Acquisition method and consolidation D. Fair value method Reporting Method 1. Less...
-
The paper Portable Social Groups: Willingness to Communicate, Interpersonal Communication Gratifications, and Cell Phone Use among Young Adults (International Journal of Mobile Communications [2007]:...
-
Acrylic bone cement is sometimes used in hip and knee replacements to fix an artificial joint in place. The force required to break an acrylic bone cement bond was measured for six specimens under...
-
The AARP Bulletin (March 2010) included the following short news brief:Older adults who did 1 hour of tai chi twice weekly cut their pain from knee osteoarthritis considerably in a 12-week study...
-
Each pair of groups that exchanged lists should form one new group. Compare lists and note areas in which the smaller groups agreed and disagreed on their classifications. Discuss the reasons for any...
-
What does this exercise teach you about international business? Heineken is the second-largest brewer in the world, with sales of 21.9 billion. Sixty-four percent of these sales occur outside Europe,...
-
What are the specific factors that enable Heineken to use the approach described and simultaneously make it difficult for some other firms to copy it? What types of firms are most and least likely to...

Study smarter with the SolutionInn App