Question: 4. In many ways, cache memory and virtual memory are similar. But their purposes are different. For example, cache memory is for decreasing effective
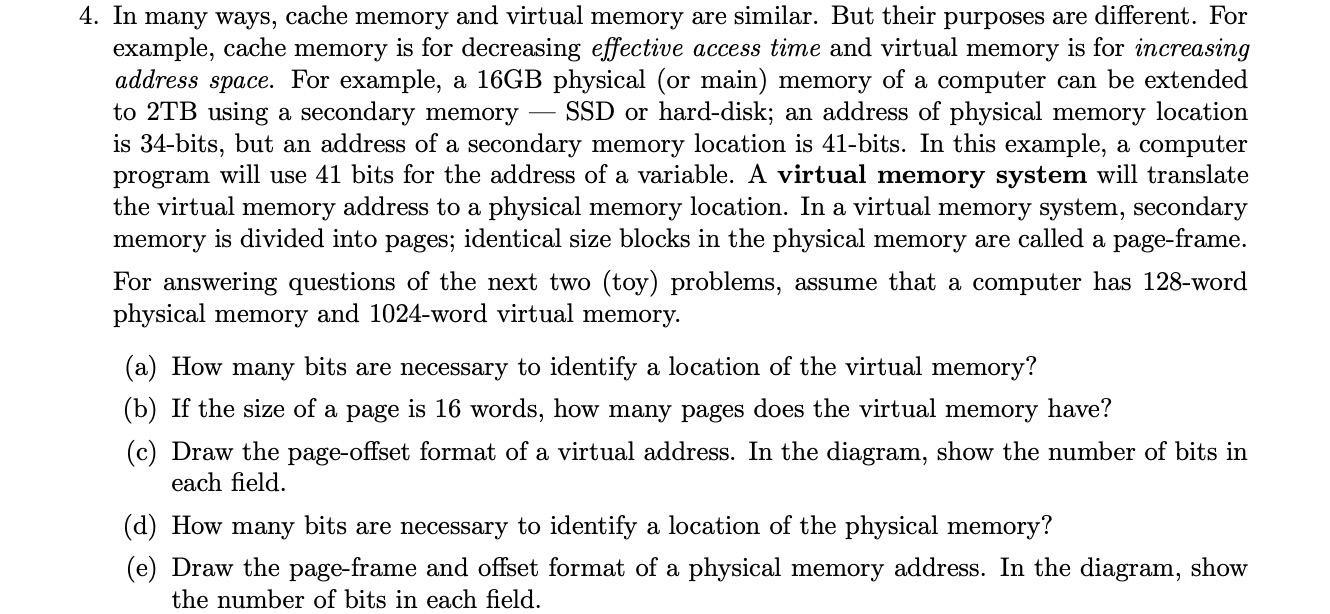
4. In many ways, cache memory and virtual memory are similar. But their purposes are different. For example, cache memory is for decreasing effective access time and virtual memory is for increasing address space. For example, a 16GB physical (or main) memory of a computer can be extended to 2TB using a secondary memory SSD or hard-disk; an address of physical memory location is 34-bits, but an address of a secondary memory location is 41-bits. In this example, a computer program will use 41 bits for the address of a variable. A virtual memory system will translate the virtual memory address to a physical memory location. In a virtual memory system, secondary memory is divided into pages; identical size blocks in the physical memory are called a page-frame. For answering questions of the next two (toy) problems, assume that a computer has 128-word physical memory and 1024-word virtual memory. (a) How many bits are necessary to identify a location of the virtual memory? (b) If the size of a page is 16 words, how many pages does the virtual memory have? (c) Draw the page-offset format of a virtual address. In the diagram, show the number of bits in each field. (d) How many bits are necessary to identify a location of the physical memory? (e) Draw the page-frame and offset format of a physical memory address. In the diagram, show the number of bits in each field.
Step by Step Solution
3.53 Rating (156 Votes )
There are 3 Steps involved in it
a To identify a location in virtual memory we need to use 10 bits because 1024 210 so we ... View full answer

Get step-by-step solutions from verified subject matter experts


