Question: 4. One classic method for composing secret messages is called a square code. The spaces are removed from the english text and the characters
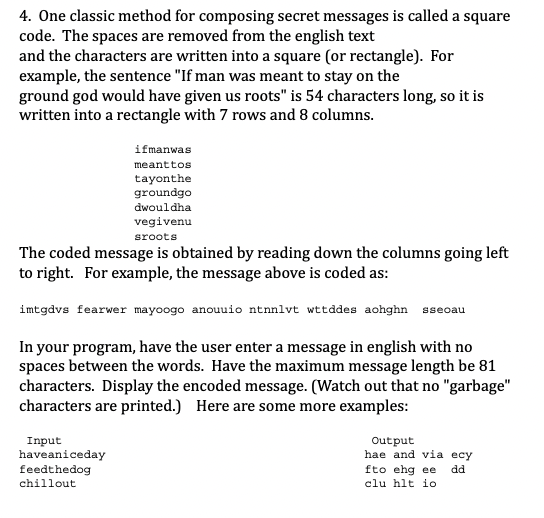
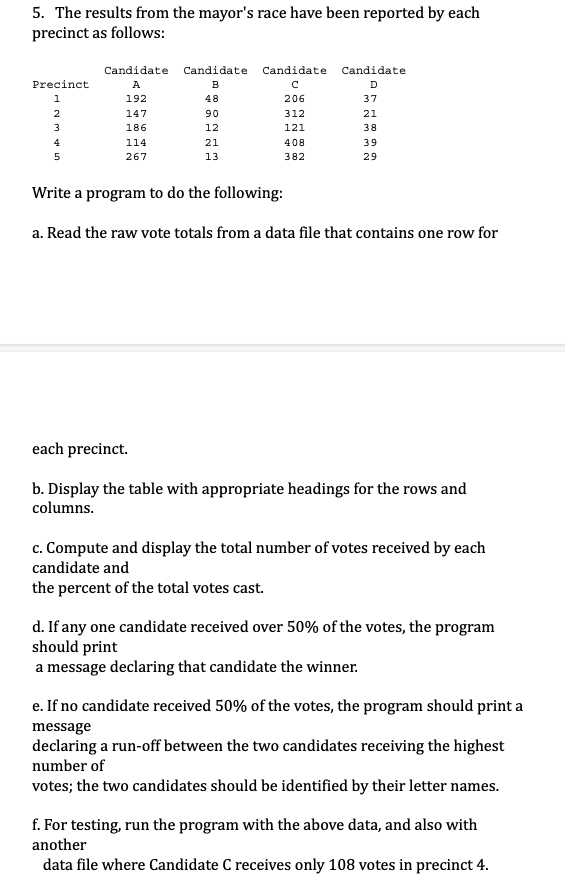
4. One classic method for composing secret messages is called a square code. The spaces are removed from the english text and the characters are written into a square (or rectangle). For example, the sentence "If man was meant to stay on the ground god would have given us roots" is 54 characters long, so it is written into a rectangle with 7 rows and 8 columns. ifmanwas meanttos tayonthe groundgo dwouldha vegivenu sroots The coded message is obtained by reading down the columns going left to right. For example, the message above is coded as: imtgdvs fearwer mayoogo anouuio ntnnlvt wttddes aohghn sseoau In your program, have the user enter a message in english with no spaces between the words. Have the maximum message length be 81 characters. Display the encoded message. (Watch out that no "garbage" characters are printed.) Here are some more examples: Input haveaniceday feedthedog chillout Output hae and via ecy dd fto ehg ee clu hlt io 5. The results from the mayor's race have been reported by each precinct as follows: Precinct 1 2 3 4 5 Candidate A 192 147 186 114 267 Candidate Candidate Candidate B D 48 206 37 90 21 12 38 39 29 21 13 312 121 408 382 Write a program to do the following: a. Read the raw vote totals from a data file that contains one row for each precinct. b. Display the table with appropriate headings for the rows and columns. c. Compute and display the total number of votes received by each candidate and the percent of the total votes cast. d. If any one candidate received over 50% of the votes, the program should print a message declaring that candidate the winner. e. If no candidate received 50% of the votes, the program should print a message declaring a run-off between the two candidates receiving the highest number of votes; the two candidates should be identified by their letter names. f. For testing, run the program with the above data, and also with another data file where Candidate C receives only 108 votes in precinct 4.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


