Question: 4.02. Subnet addressing. Consider the three subnets below, each in the larger 128.119.160/24 network. The following questions are concerned with subnet addressing. Answer each
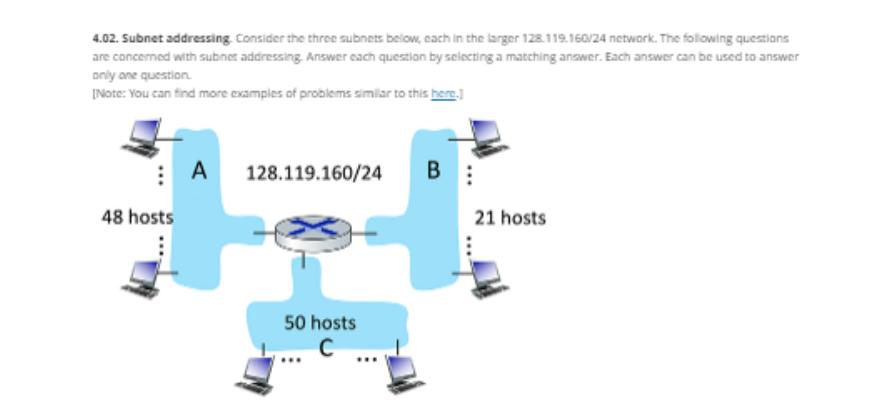
4.02. Subnet addressing. Consider the three subnets below, each in the larger 128.119.160/24 network. The following questions are concerned with subnet addressing. Answer each question by selecting a matching answer. Each answer can be used to answer only one question. [Note: You can find more examples of problems similar to this here.] 48 hosts A 128.119.160/24 50 hosts C B 21 hosts Prompts What is the maximum number of hosts possible in the larger 128.119.160/24 network? How many bits are needed to be able to address all of the host in subnet A? Suppose that subnet A has a CIDRized subnet address range of 128.119.160.128/26 (hint: 128 is 1000 0000 in binary: Subnet B has an CIDRied subnet address range of 128.119.160.64/26. We now want a valid CIDRized IP subnet address range for subnet C of the form 128.119.160.x/26. What is a valid value of x? Submitted Answers
Step by Step Solution
There are 3 Steps involved in it
The images youve provided feature a networking problem focused on subnet addressing The first image shows three subnets A B and C labeled with the num... View full answer

Get step-by-step solutions from verified subject matter experts


