Question: 4.5. Identify and write down two (2) standardised signalling protocols for managing traffic engineering (TE) of MPLS paths 4.6. Identify and write down five
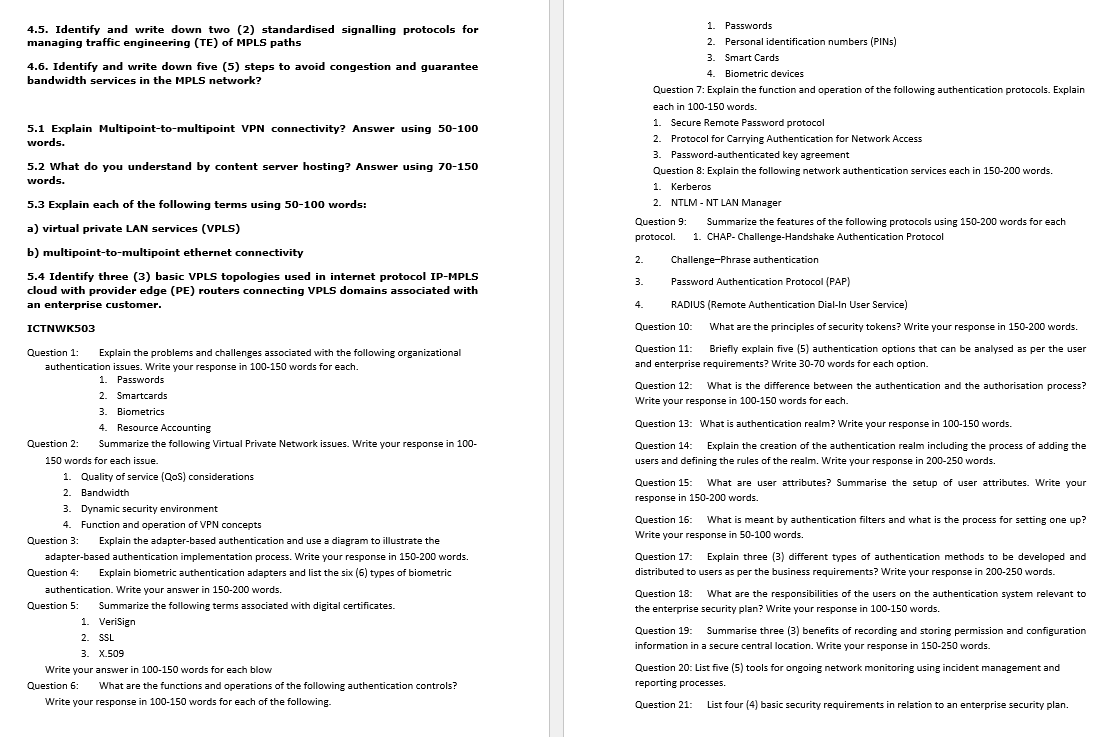
4.5. Identify and write down two (2) standardised signalling protocols for managing traffic engineering (TE) of MPLS paths 4.6. Identify and write down five (5) steps to avoid congestion and guarantee bandwidth services in the MPLS network? 5.1 Explain Multipoint-to-multipoint VPN connectivity? Answer using 50-100 words. 5.2 What do you understand by content server hosting? Answer using 70-150 words. 5.3 Explain each of the following terms using 50-100 words: a) virtual private LAN services (VPLS) b) multipoint-to-multipoint ethernet connectivity 5.4 Identify three (3) basic VPLS topologies used in internet protocol IP-MPLS cloud with provider edge (PE) routers connecting VPLS domains associated with an enterprise customer. ICTNWK503 Question 1: Explain the problems and challenges associated with the following organizational authentication issues. Write your response in 100-150 words for each. 1. Passwords 2. Smartcards 3. Biometrics 4. Resource Accounting Question 2: Summarize the following Virtual Private Network issues. Write your response in 100- 150 words for each issue. 1. Quality of service (QoS) considerations 2. Bandwidth 3. Dynamic security environment 4. Function and operation of VPN concepts Question 3: Explain the adapter-based authentication and use a diagram to illustrate the adapter-based authentication implementation process. Write your response in 150-200 words. Question 4 Explain biometric authentication adapters and list the six (6) types of biometric authentication. Write your answer in 150-200 words. Question 5: Summarize the following terms associated with digital certificates. 1. VeriSign 2. SSL 3. X.509 Write your answer in 100-150 words for each blow Question 6: What are the functions and operations of the following authentication controls? Write your response in 100-150 words for each of the following. Question 9: protocol. Summarize the features of the following protocols using 150-200 words for each 1. CHAP-Challenge-Handshake Authentication Protocol Challenge-Phrase authentication Password Authentication Protocol (PAP) RADIUS (Remote Authentication Dial-In User Service) Question 10: What are the principles of security tokens? Write your response in 150-200 words. Question 11: Briefly explain five (5) authentication options that can be analysed as per the user and enterprise requirements? Write 30-70 words for each option. 2. 3. 1. Passwords 2. Personal identification numbers (PINS) 3. Smart Cards 4. Biometric devices Question 7: Explain the function and operation of the following authentication protocols. Explain each in 100-150 words. 1. Secure Remote Password protocol 2. Protocol for Carrying Authentication for Network Access 3. Password-authenticated key agreement Question 8: Explain the following network authentication services each in 150-200 words. 1. Kerberos 2. NTLM-NT LAN Manager 4. Question 12: What is the difference between the authentication and the authorisation process? Write your response in 100-150 words for each. Question 13: What is authentication realm? Write your response in 100-150 words. Question 14: Explain the creation of the authentication realm including the process of adding the users and defining the rules of the realm. Write your response in 200-250 words. Question 15: What are user attributes? Summarise the setup of user attributes. Write your response in 150-200 words. Question 16: What is meant by authentication filters and what is the process for setting one up? Write your response in 50-100 words. Question 17: Explain three (3) different types of authentication methods to be developed and distributed to users as per the business requirements? Write your response in 200-250 words. Question 18: What are the responsibilities of the users on the authentication system relevant to the enterprise security plan? Write your response in 100-150 words. Question 19: Summarise three (3) benefits of recording and storing permission and configuration information in a secure central location. Write your response in 150-250 words. Question 20: List five (5) tools for ongoing network monitoring using incident management and reporting processes. Question 21: List four (4) basic security requirements in relation to an enterprise security plan.
Step by Step Solution
There are 3 Steps involved in it
Lets break down the questions and provide concise answers for each 45 Standardised Signalling Protocols for Managing Traffic Engineering of MPLS Paths RSVPTE Resource Reservation Protocol Traffic Engi... View full answer

Get step-by-step solutions from verified subject matter experts


