Question: 6. Consider a public key cryptography system. Assume that Bob generated his public key as K, and his private key as KB; Alice generated her
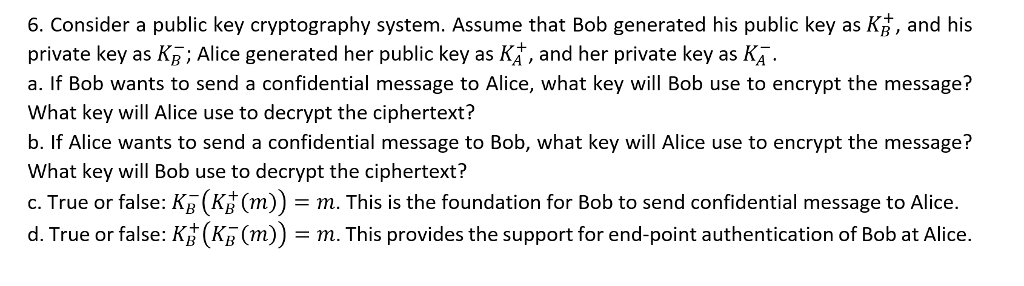
6. Consider a public key cryptography system. Assume that Bob generated his public key as K, and his private key as KB; Alice generated her public key as KA, and her private key as KA. a. If Bob wants to send a confidential message to Alice, what key will Bob use to encrypt the message? What key will Alice use to decrypt the ciphertext? b. If Alice wants to send a confidential message to Bob, what key will Alice use to encrypt the message? What key will Bob use to decrypt the ciphertext? c. True or false: K (KH (m)) - m. This is the foundation for Bob to send confidential message to Alice. d. True or false: Ki (Kg (m))-m. This provides the support for end-point authentication of Bob at Alice
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


