Question: 7/8 ? Using PKI, Ali encrypted a message using Yahya's public key. Which key is required to decrypt this message a. Yahya's private key O
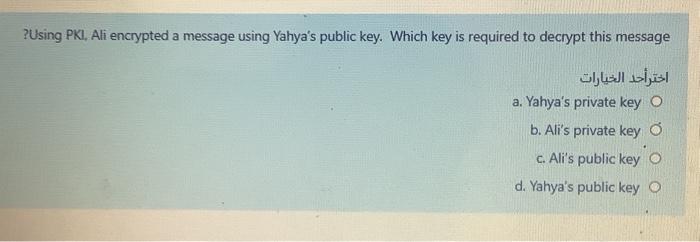
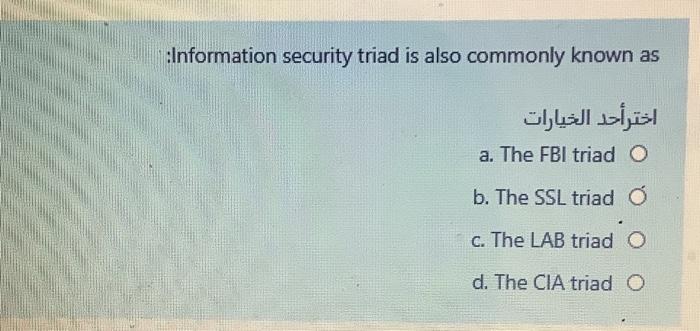
? Using PKI, Ali encrypted a message using Yahya's public key. Which key is required to decrypt this message a. Yahya's private key O b. Ali's private key o c. Ali's public key o d. Yahya's public key :Information security triad is also commonly known as a. The FBI triad O b. The SSL triad c. The LAB triad O d. The CIA triad O
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


