a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10)...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
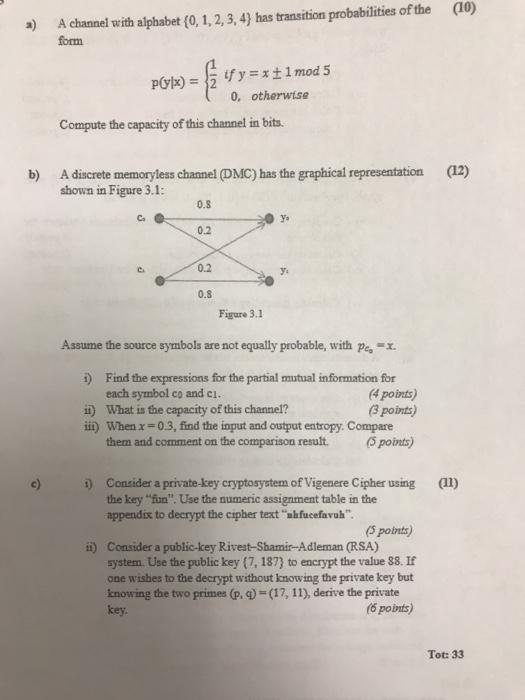
a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10) form P(y|x) = $₁ Compute the capacity of this channel in bits. b) A discrete memoryless channel (DMC) has the graphical representation (12) shown in Figure 3.1: 0.8 0.2 if y=x ±1 mod 5 0, otherwise 0.2 0.8 Figure 3.1 Assume the source symbols are not equally probable, with pe, X. 1) Find the expressions for the partial mutual information for each symbol co and c1. (4 points) ii) What is the capacity of this channel? (3 points) iii) When x=0.3, find the input and output entropy. Compare them and comment on the comparison result. (5 points) 1) Consider a private-key cryptosystem of Vigenere Cipher using (11) the key "fun". Use the numeric assignment table in the appendix to decrypt the cipher text "ahfucefavuh". (5 points) ii) Consider a public-key Rivest-Shamir-Adleman (RSA) system. Use the public key (7, 187) to encrypt the value 88. If one wishes to the decrypt without knowing the private key but knowing the two primes (p, q)=(17, 11), derive the private key. (6 points) Tot: 33 a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10) form P(y|x) = $₁ Compute the capacity of this channel in bits. b) A discrete memoryless channel (DMC) has the graphical representation (12) shown in Figure 3.1: 0.8 0.2 if y=x ±1 mod 5 0, otherwise 0.2 0.8 Figure 3.1 Assume the source symbols are not equally probable, with pe, X. 1) Find the expressions for the partial mutual information for each symbol co and c1. (4 points) ii) What is the capacity of this channel? (3 points) iii) When x=0.3, find the input and output entropy. Compare them and comment on the comparison result. (5 points) 1) Consider a private-key cryptosystem of Vigenere Cipher using (11) the key "fun". Use the numeric assignment table in the appendix to decrypt the cipher text "ahfucefavuh". (5 points) ii) Consider a public-key Rivest-Shamir-Adleman (RSA) system. Use the public key (7, 187) to encrypt the value 88. If one wishes to the decrypt without knowing the private key but knowing the two primes (p, q)=(17, 11), derive the private key. (6 points) Tot: 33
Expert Answer:
Answer rating: 100% (QA)
a To compute the capacity of the given channel we need to determine the channels transition probabilities and calculate the mutual information The tra... View the full answer

Related Book For 

Introduction to Java Programming, Comprehensive Version
ISBN: 978-0133761313
10th Edition
Authors: Y. Daniel Liang
Posted Date:
Students also viewed these accounting questions
-
Analyzing Causes In 2013, it was reported that house prices were increasing for the first time in almost 5 years. Identify the factors that explain why house prices began to rise
-
For the Dupit Corp. case study introduced in Section 11.4, the management science team was able to apply a variety of queueing models by making the following simplifying approximation. Except for the...
-
4 year(s) ago, Mary invested 43,673 dollars. She has earned and will earn compound interest of 11.19 percent per year. In 1 year(s) from today, Zach can make an investment and earn simple interest of...
-
Describe several features of the ACA that are designed to minimize adverse selection. Why might some of those measures not end up working very well?
-
Arrow, a U.S. corporation, annually sells one million starter motors to Bentley, a wholly owned foreign subsidiary organized in Country K. Bentley sells the starters as replacement parts through auto...
-
Explain the difference between basic earnings per share and diluted earnings per share.
-
A trial balance: a. lists only revenue and expense accounts. b. lists all accounts and their balances. c. will help detect omitted journal entries. d. detects all errors that could be made during the...
-
What has Target done well over the years in terms of its integrated marketing communications strategy? What should it do going forward?
-
Find the absolute maximum and absolute minimum values of the function f(a) = 23 -12x2-27x +7 on each of the indicated intervals. Enter - 1000 for any absolute extrema that does not exist. (A)...
-
Kolbec Community College (KCC) has 4,000 full-time students and offers a variety of academic programs in three areas: professional studies, arts, and technology. The professional studies programs...
-
Match each question with the expression that would be used to answer the question. (a) 240 is 120% of what? 1.20 x 240 240 1.20 120240 (b) 120 is what percent of 240? (c) 1.20 x 240 240 1.20 120 240...
-
What is the primary role of quality assurance management as it operates within the information systems function?
-
What is the difference between a discretionary access control policy and a mandatory access control policy? In commercial information systems environments, which type of access control policy is most...
-
Why are existence controls in the boundary subsystem often somewhat simpler than existence controls in other subsystems?
-
The information systems department in your organization has recently purchased a checkpoint/restart facility to support their batch processing operations. Although batch systems are only a small part...
-
Why is it best to strive for minimal specification of standards when preparing information systems standards?
-
onse. (1 mark each) Use the following information to answer the next three questions: The height of a tidal wave approaching the face of the cliff on an island is represented by the = 7.5 cost where...
-
On 1 July 2018, Parent Ltd acquired all the shares of Son Ltd, on a cum-div. basis, for $2,057,000. At this date, the equity of Son Ltd consisted of: $ 1,000,000 Share capital 500 000 shares...
-
Rewrite the preceding program that uses a new greedy algorithm that places an object with the smallest weight into the first bin in which it would fit. Your program should prompt the user to enter...
-
Modify Listing 28.10, ConnectedCircles.java, to enable the user to drag and move a circle. Listing 1 import javafx.application. Application; 2 import javafx.geometry.Point2D; 3 import...
-
Write a program that compresses a source file into a target file using the Huffman coding method. First use ObjectOutputStream to output the Huffman codes into the target file, and then use...
-
Accounting for joint products You have just been hired as the chief cost accountant for the J&M Company. Its major product group is four food processing solutions, which are pro- duced in a joint...
-
Analyzing the impact of different joint costing methods Petro-Edge Corporation manu- factures specialized oils and lubricants for the aviation industry. One product group, manufactured in a joint...
-
Analyzing Joint and by-product data with standard costs Haverly Company makes two chemical solvents used in the production of cleaning compounds. The products are manufactured in a joint production...

Study smarter with the SolutionInn App